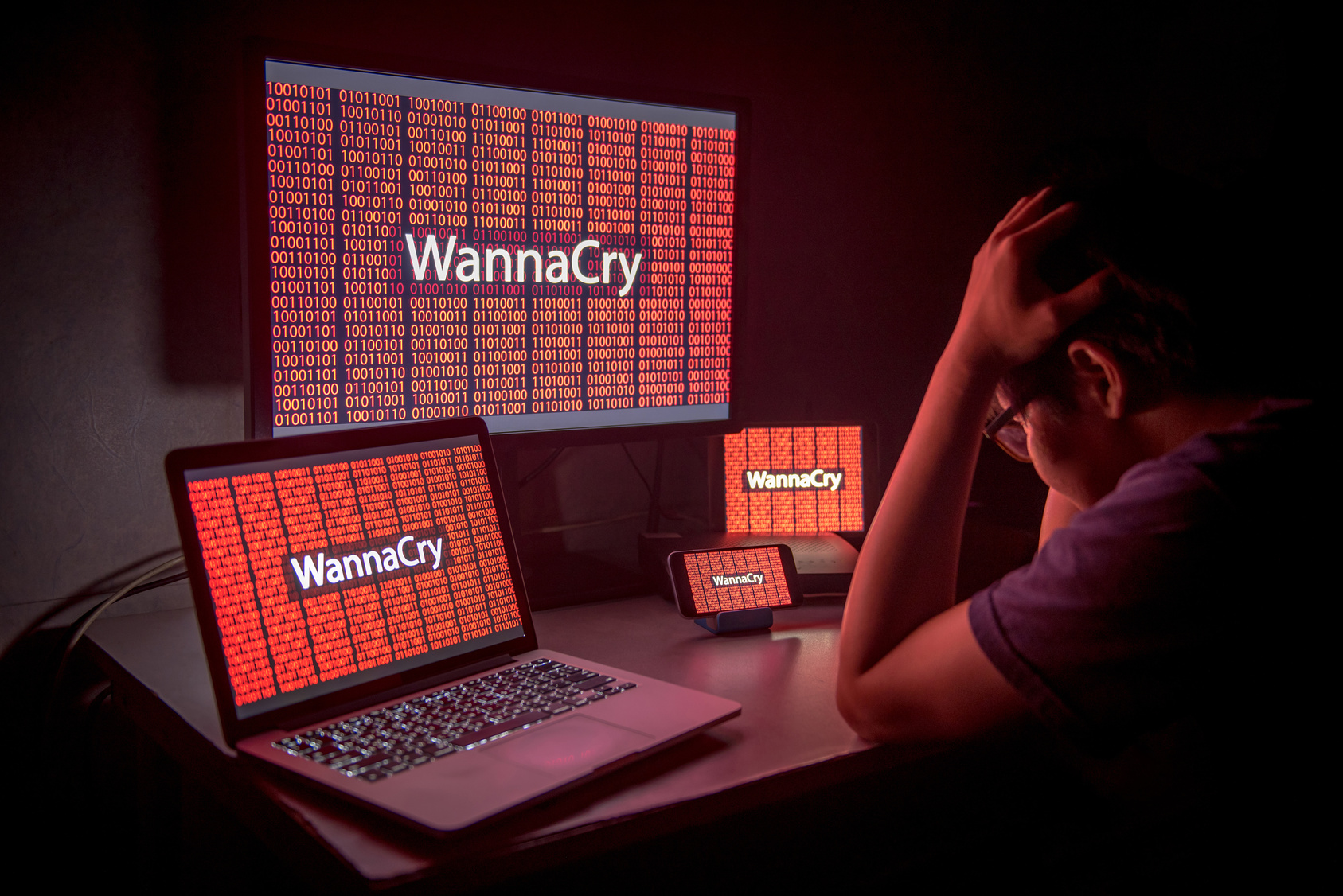
The Wanna Decryptor (Wannacry) attack is being cited as the largest ransomware attack in history – it was certainly the largest and most disruptive cyber attack ever launched against the UK’s National Health Service (NHS).
The attack, which struck organisations across the globe on May 14 2017, knocked 40 NHS hospitals offline and cut access to computers for 24 trusts. This resulted in diverted A&E services across affected hospitals, fewer GP services available across the country and cancellations to time-sensitive and life-changing operations.

The ransomware locked down critical NHS computers, displaying nothing but a message from Wannacry’s criminal architects demanding payment or face getting NHS data destroyed. Engineers continue to work tirelessly, days after the infection ran rampant through unsecure NHS systems.
As the situation unfolds — with latest reports pointing the finger of accusation toward North Korea — the question remains: why was the NHS so vulnerable to Wannacry?
A leaked NSA cyber superweapon
The ransomware used to attack the NHS was developed to combine a critical Windows exploit with a self replicating virus, spreading the malware quickly across vulnerable Windows machines.
The exploit in question, known as ETERNALBLUE, is generally considered by the infosecurity community to have been developed by the U.S. National Security Agency (NSA). By using the ETERNALBLUE exploit to gain remote access, an attacker can then spread malware across vulnerable machines over a local network.
The exploit was leaked on 14 April 2017 by hacking group The Shadow Brokers. By ingeniously combining the Wannacry exploit with a self-replicating worm, as yet unknown cyber criminals were able to subsequently launch the world’s largest ransomware attack.
By developing the secret ETERNALBLUE exploit, without proper disclosure to Microsoft, the NSA share a significant proportion of the blame for the Wannacry attack.
The death of Windows XP
In the wake of the Wannacry attack, the NHS is being denounced for its continuing use of the outdated Windows XP operating system.
When the ETERNALBLUE exploit was first leaked on 14 April 2017, Microsoft released a security patch for non-legacy products. As is standard, this did not include the legacy Windows XP software in use across the NHS.
In fact Microsoft’s support for Windows XP officially ended on 8 April 2014. And whilst the NHS did pay Microsoft to continue security updates, the deal was ended as an austerity measure in 2015.
This meant that the Windows XP operating system used by the NHS was not updated in line with modern security threats, like Wannacry.
Microsoft have shouted for years that Windows XP users must upgrade — without regular security patches the operating system’s security cannot be guaranteed. It’s a basic rule of cyber security, but one clearly not always obeyed.
NHS Digital was completely ignored
The ETERNALBLUE exploit was no secret; NHS Digital issued a patch capable of preventing the Wannacry ransomware two months prior to the attack.
If this patch was properly applied across each NHS trust, it would have prevented the Wannacry attack by eliminating the initial ETERNALBLUE exploit.
Once the ransomware infected NHS machines, it quickly travelled across the NHS network spreading from computer to computer. At this point computers which were not updated with the NHS digital security patch were compromised.
This lack of discipline in patching new versions of Windows is a massive contributing factor to the NHS’ Wannacry weakness. By failing to apply the patch from NHS Digital, individual NHS trusts allowed the Wannacry virus to run rampant.
In response to the global Wannacry attack – and a clear lack of enthusiasm towards upgrading from the legacy operating system — Microsoft took the exceptional step of releasing an emergency patch for Windows XP.

A lack of cyber security investment and standards in NHS trusts
The ransomware attack has raised questions regarding the critical lack of cyber security investment, awareness and governance within the NHS.
Accountability for IT standards, including security, vary massively across the NHS. Worryingly, some trusts do not have a single person responsible for IT sitting on their board.
In 2013 it was reported that, when secretary of state for health Jeremy Hunt was briefed on the security risks that a lack of IT standards would create in the NHS, “Hunt never grasped the problem.”
Businesses (and governments) still don’t ‘really’ care
Cyber security is a shared responsibility and the recent attack makes this fact painfully obvious. That so many computers were susceptible to the Wannacry virus two months after Microsoft’s patch is shocking, showing that top-level employees either don’t understand the risk or don’t care.
At the centre of the attack, Microsoft is taking aim at governments for stockpiling vulnerabilities, like the NSA-leaked ETERNALBLUE.
Worryingly this isn’t the first time a government organisation has lost control of a stockpiled exploit – vulnerabilities stored by the CIA were revealed on WikiLeaks.
Instead of being responsibly disclosed, the Wannacry exploit was leaked, cutting short the time Microsoft and businesses worldwide had to react.
“Repeatedly, exploits in the hands of governments have leaked into the public domain and caused widespread damage,” wrote Microsoft’s Brad Smith. “An equivalent scenario with conventional weapons would be the U.S. military having some of its Tomahawk missiles stolen.”
Could it happen again?
Reports show the Wannacry attack caused substantially less financial and operational damage than expected. Nonetheless, the attack is a wakeup call, drawing attention to a critical lack of cyber security understanding and awareness in the NHS and worldwide.
Blocking future ransomware attacks will require an investment in cyber security education – from basic cyber security education for employees at every level, to qualifying IT teams with security knowledge through industry standard cyber security, like GIAC’s GCIH certification.
This will not be fixed quickly. In the meantime these attacks will continue. This is not the end of Wannacry and new mutations are being spotted already.






