Ransomware has emerged as a critical threat to businesses and government organisations in recent years. The ongoing outbreak of ransomware attacks is costing the global economy dearly: according to IBM, the average cost of a ransomware breach is $4.62m. But who are the perpetrators of these attacks and how can organisations protect against them? Here is everything you need to know about ransomware.

What is ransomware and how does it work?
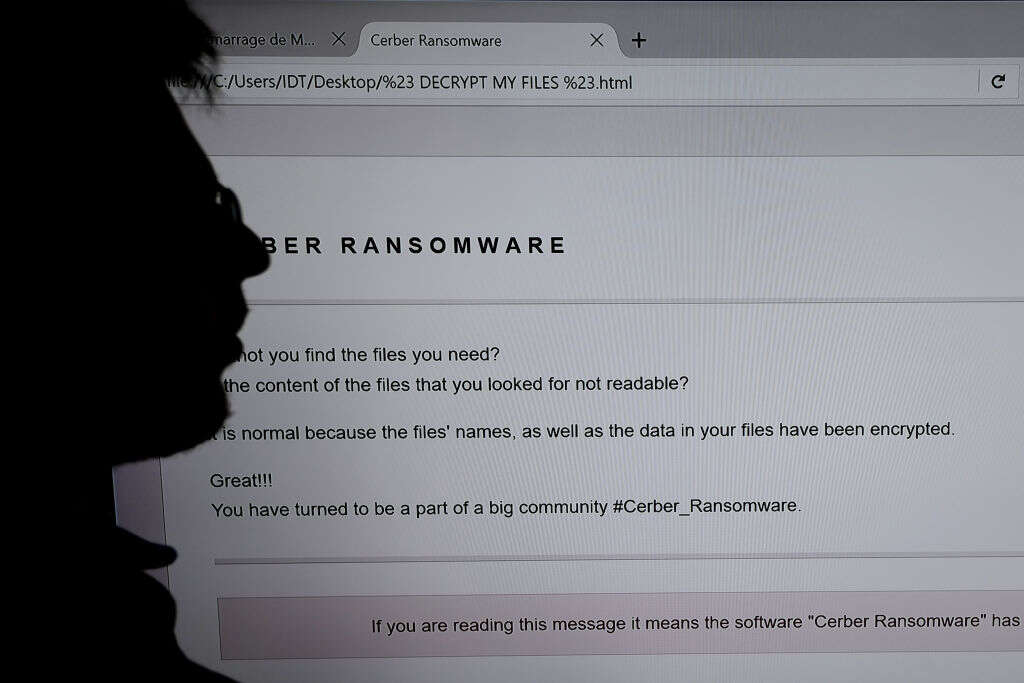
Ransomware is a type of malware designed to incapacitate target systems, often by encrypting data, in such a way that allows criminals to demand a ransom from their victims. The most common ways in which malware infections occur are via remote desktop systems, email phishing and vulnerabilities in software products, according to research by security provider Coveware.
Ransomware has been around for decades but has become much more prevalent in recent years. According to advisory PwC, this is due to the emergence of ransomware-as-a-service (RaaS), whereby cybercriminals create and distribute ransomware, then sell access to criminals who don’t have the skills to create it themselves. Ransomware has also been accelerated by the number of people working from home on their own devices during the pandemic, PwC says.
The groups behind the ransomware attacks are also using more sophisticated techniques to extort their victims. In addition to encrypting data, they are increasingly threatening to publish it online (a technique known as 'double extortion') and launch distributed denial of service (DDoS) attacks.
What are the main examples of ransomware attacks?
Although only a quarter of ransomware attacks are reported, according to US cyber security agency CISA, a number of high-profile incidents have made the headlines, capturing the attention of the public and policymakers.
The attack on the Colonial Pipeline in the US earlier this year was the first high-profile attack on US national infrastructure. The oil pipeline, which carries 45% of the US east coast’s diesel, petrol and jet fuel, was disrupted in May by ransomware from the notorious RaaS group DarkSide, prompting US President Joe Biden to declare a state of national emergency. The company ended up paying a $5m ransom to get its systems back online.
Shortly after, a ransomware attack struck JBS, a Brazilian-owned meat company and the world's largest processor of fresh beef and pork. This attack, perpetrated by famously ruthless ransomware gang REvil, shut down the company's operations in Australia, Canada and the US. JBS reportedly paid an $11m ransom. This time, Biden sought to "engage directly with the Russian government on this matter" to encourage it to tackle ransomware gangs, many of whom are believed to operate in the country.
REvil is also believed to be behind a ransomware attack that exploited a vulnerability in remote access software from US software company Kaseya in July 2021. The software is used by managed services providers, allowing the group to encrypt the data of up to 1,500 end-user organisations. REvil affiliates reportedly offered a 'universal decryptor' to unlock all affected companies' data for $70m.
How did ransomware get so bad?
In addition to the growing sophistication of ransomware gangs, the pandemic has been an important driver for the ongoing ransomware spree, according to research by KPMG. People's anxieties about Covid-19 gave criminals ample opportunity to trick them into clicking nefarious links, while the widespread switch to homeworking meant workers were using their own devices and accessing work systems remotely, opening up new security vulnerabilities.
Another important driver has been the advent of cryptocurrencies, says Ryan Kalember, EVP in cybersecurity strategy at Proofpoint, which offer an untraceable way for criminals to receive payment. "In the early days of DDoS attacks and extortion, you had e-cash and wonky early internet currencies and you also had traditional bank transfers which you don't want to be dealing with as a cybercriminal," he says. "Now because of cryptocurrency, they can actually get paid."
Why doesn’t antivirus stop ransomware?
Antivirus software typically works by detecting known information security threats. However, sophisticated cybercriminals and state-backed advanced persistent threats deal in new and undocumented threats in order to compromise their target systems. This means that, while deploying antivirus software and keeping it up to date is an important part of any cybersecurity strategy, antivirus alone is not sufficient to deter all security attacks, including ransomware.
How to protect your systems from a ransomware attack
In a recent interview, an alleged member of the LockBit ransomware gang said that one of the best ways for organisations to defend against its attacks is to employ a full-time 'red team' of security experts who constantly test their defences for vulnerabilities. Organisations should also "regularly update all software, perform preventive talks with a company’s employees to thwart social engineering, and most importantly, use the best ransomware-fighting antivirus," they said.
In order to limit the danger and potential damage of malware infections, the UK's National Cyber Security Centre advises companies to focus on four areas: ensuring their data is backed up; preventing malware from entering and spreading within their organisation; preventing malware from running; and preparing for an incident. "Plan for an attack, even if you think it is unlikely," it says.
Bharat Mistry, technical director of the UK and Ireland at Trend Micro, advises companies to focus on people and process, as well as technology, when defending their organisations. "People are number one. You can do so much here without doing heavy technology investment," he says. "Secondly, the process; what are the procedures and policies that they have in place?" For example, he advises that companies follow the '3, 2, 1' principle when backing up their data: "Three copies of a backup, on two separate media and one off-site."
What does the future hold for ransomware?
Ransomware has grown from being a peripheral cybersecurity threat to a matter of geopolitical concern, and governments are rallying to crack down. The US government has established a ransomware task force (RTF), a coalition of over 60 experts in industry, government, law enforcement, civil society, and international organisations to tackle the threat. The RTF works closely with the Global Cyber Alliance, also spearheaded in the US, which builds programmes, partnerships, and tools to make the connected world safer and more secure. The EU has also assembled a joint cybercrime unit, which was created to protect national infrastructure within Europe.
Eliminating the threat entirely will require a widespread modernisation of legacy systems across business and government. This is no quick task, says Greg Austin, senior fellow at the International Institute for Security Studies. "It's a very long process, a process that takes a decade or two, not one or two years," he says.






