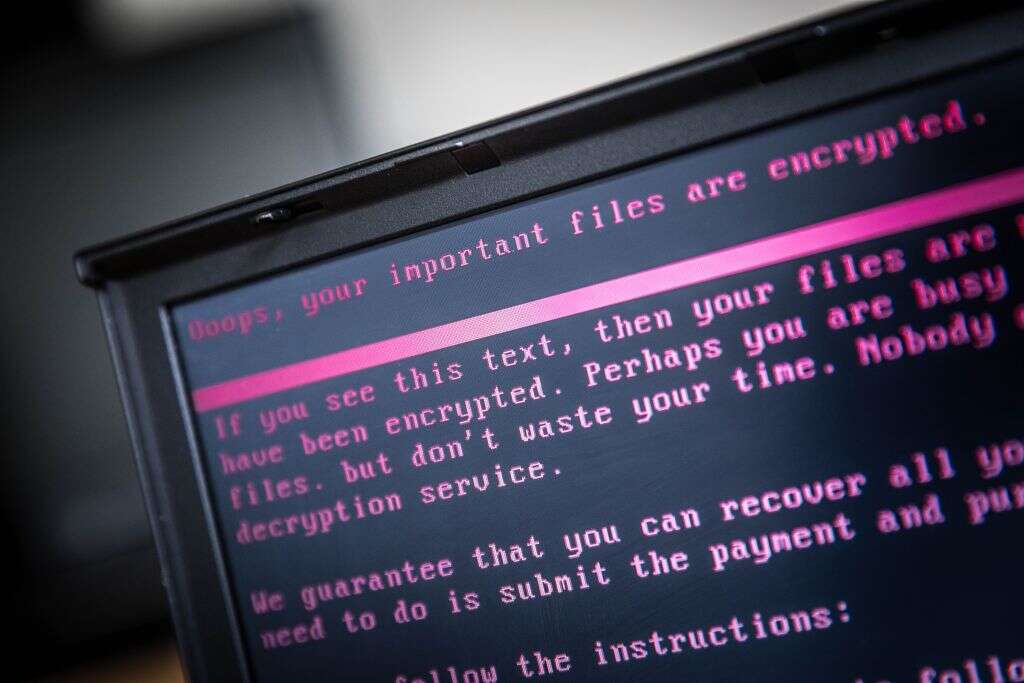
From the Colonial Pipeline attack to ongoing disruption to the Irish health service’s IT systems, ransomware attacks have claimed high-profile victims and achieved widespread notoriety this year. The scale and success of these attacks reflects the growing sophistication of ransomware-as-a-service (RaaS) operations. Vying to boost their market share, the groups – such as DarkSide – behind these RaaS services are becoming increasingly professional, prompting one analyst to coin the term ‘ransomware-as-a-corporation’.
Criminals have been using malware to extract ransoms from their victims since the 1980s. The technique has grown steadily since then but a watershed moment came in 2019, when a prominent ransomware gang called Maze threatened not just to withhold access to data it had stolen from a security staffing company online, but to publish it online as well. This so-called ‘double extortion‘ now accounts for 77% of ransomware attacks, and has led criminals to demand higher ransoms – the average ransom payment grew 171% in 2020, up to $312,493, according to research from Palo Alto Networks – and to pursue more prominent victims.

How ransomware groups like DarkSide manage their reputations
By making ransomware a more public affair, double extortion has also transformed the underground industry that provides ransomware services. “I think double extortion has definitely improved the professionalisation of these ransomware groups,” says Stefano De Blasi, a researcher at cybersecurity company Digital Shadows.
“Once you only had to deal with encryption and decryption,” he explains. “Now we’re talking about maintaining a data leak site, having someone take care of the press releases, having someone who takes care of the graphics, someone who takes care of managing when and how that data is uploaded to the site.”
Managing public perception is an especially important part of the ransomware business, with groups such as REvil and DarkSide issuing press releases for their attacks. “There is definitely a PR side of things,” explains Jason Hill, head researcher at cybersecurity firm CyberInt. “If nobody publicises their activity, then nobody could be worried about it.”
Research by security provider Kaspersky describes how ransomware groups cultivate a public profile to reassure victims that they will receive their data if they pay the ransom. “To ensure that their ability to restore encrypted files would never be questioned, they cultivated an online presence, wrote press releases and generally made sure their name would be known to all potential victims,” it says.
The need for a public profile explains why some groups have taken pains to present themselves as essentially ethical actors. Last October, DarkSide donated $20,000-worth of stolen bitcoin to two international charities (neither of the charities kept the stolen funds). “We are apolitical,” the group said in a recent press release. “Our goal is to create money, not creating problems for society.”
This concern for reputation management extends to a surprising degree of support for their victims, to ensure data is effectively restored once the ransom is paid. “When you’re talking about big ransoms, potentially millions, if someone pays and they don’t get their data back, everyone is going to know about that,” explains Hill. “There’s only so many times you can scam people.”
As a result, groups will provide technical support to their victims once the ransom is paid, says Hill. “They don’t want their reputation to be tarnished by not restoring things.”
The professionalisation of ransomware groups
As ransomware operations have become more complex, they require a growing range of specialist skills – researchers describe networks of ‘affiliates’ who collaborate on attacks – and an increasingly formal management structure. Analysis by security company Tetra Defense details the emergence of managers in RaaS operations who recruit affiliates and approve ransom negotiations.
Another role to have emerged in the ransomware ecosystem is that of the initial access broker (IAB). This role has evolved from that of ‘bot masters’ who control access to networks of compromised devices that are used in distributed denial of service (DDoS) or brute-force attacks. Rather than selling access to these networks en masse, IABs look for high-profile and potentially lucrative organisations in their networks.
Once they have identified a potential target, the IAB will ‘groom’ them – they “perform some reconnaissance, escalate privileges or install further tooling,” explains Victoria Kivilevich, a threat intelligence analyst at Israeli cybersecurity company Ke La – before sharing access in exchange for a cut of the ransom. “Once a target is ripe and ready, it can be offered on cybercrime markets where ransomware affiliates can acquire it and move forward with the final attack,” says Kivilech. Last year, DarkSide posted a job advert on the dark web for an IAB with access to companies with a net worth of $400m or higher.
Will ransomware groups be defeated?
One reason ransomware groups are becoming more conspicuous and pursuing more prominent targets is that they have not been caught. “At some point, I think cybercriminals have started to think they are invincible, so they keep pushing the limit,” says De Blasi. “That’s why I think right now they’re getting bolder and bolder.”
Without an international, coordinated response from law enforcement, ransomware attacks on big businesses and critical national infrastructure are likely to continue, he adds. “As more attacks on critical national infrastructure, health and the education sector are successful, cybercriminals will continue to operate until, of course, some strong response from law enforcement agencies all over the world, an international approach, is taken against them.”






