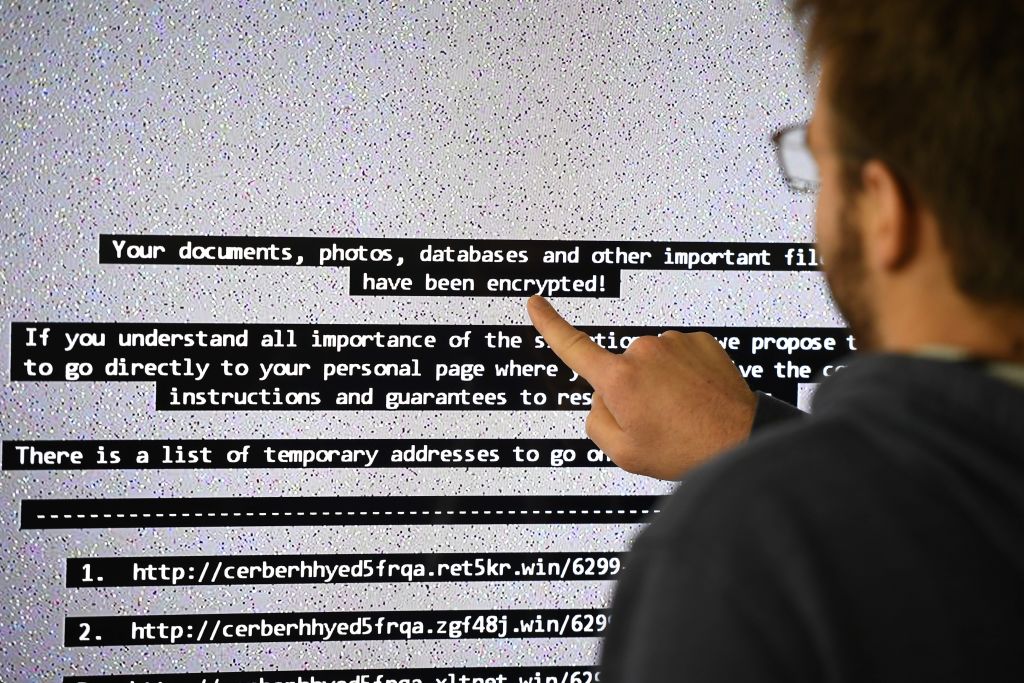
Ransomware is fuelling a global cybercrime spree, with high-profile businesses, public sector organisations and infrastructure operators falling victim to hackers every week. According to cryptocurrency researchers Chainalysis, the total value of ransoms paid by victims grew by 311% in 2020 to $350m.
Behind these attacks lies an increasingly professional industry, with networks of affiliates co-ordinating to identify, infiltrate and extort valuable targets. At the centre of this industry sit the ‘gangs’ that build and operate the malware that makes the attacks possible. Some use this malware to extort victims directly, while others offer ransomware-as-a-service (RaaS), helping other criminals target specific organisations.

The top ten ransomware gangs
Recent analysis of the distribution of the malware used in ransomware attacks so far this year, conducted by security provider BlackFog, reveals the top ten ransomware gangs in 2021. Although the identities of group members are mostly unknown, understanding their intentions and ways of operation can help organisations anticipate attacks.
1) REvil (aka Sodin or Sodinokibi)
In 2019, a ransomware gang known as GandCrab shut down – not because they had been caught, but because they wanted to retire after making $2bn. But ransomware-as-a-service group REvil appeared soon after, and it is believed to have been founded by GandCrab's core developers.
According to BlackFog, REvil's malware was present in 13.1% of ransomware attacks detected this year. A separate report from security company Esentire found that REvil has launched 161 successful attacks so far, 52 of which took place in the first four months of this year.
REvil is the perpetrator of one of the most noteworthy attacks of 2021, targeting a company in the Apple supply chain called Quanta, which manufactures the Notebook computer. The Sodin gang demanded $50m in Bitcoin from the company after encrypting its data, threatening to release technical details of current and future hardware.
When Quanta did not pay, the gang reportedly turned to Apple itself for the money. REvil also performed an attack on electronics manufacturer Acer, demanding the same sum of $50m.
"REvil seems to be the top one because they're just so brazen," explains Blackfog CEO Darren Williams. "The fact that they brazenly talk about how much money they're making says a lot. They claim to have made $100m in 2020. They're saying they want to make a billion dollars. They've got some pretty big egos in that sort of group."
Earlier this year, a purported REvil member told security intelligence provider Recorded Future that affiliates had used its malware to compromise military systems and other critical infrastructure.
"I know at the very least that several affiliates have access to a ballistic missile launch system, one to a US Navy cruiser, a third to a nuclear power plant, and a fourth to a weapons factory," the interviewee says. "It is quite feasible to start a war. But it’s not worth it—the consequences are not profitable." Whether or not this claim should be taken seriously can be debated: PR is a crucial component of the RaaS business model.
As with many of the most top ten ransomware groups, REvil is believed to be based in Russia. The group has not targeted victims based in the country, which could indicate that it is avoiding local law enforcement.
2) Conti (aka Ryuk or Wizard Spider)
The group known as Conti ranked joint first with REvil in BlackFog's analysis, accounting for 13.5% of attacks so far. Having emerged in 2018, however, it has been responsible for more successful attacks to date: coming in at 352 in total, including 63 this year, according to Esentire.
In March of this year, the FBI released a warning about the group after it attacked the Irish healthcare system. Conti has less of a public profile than REvil but while other groups appear to have some ethical limitations on which organisations they will target, Conti has contributed to a wave of attacks on the healthcare and education sectors this year. In March, for example, Broward County School District was compromised and Conti demanded a $40m ransom. When the district refused to pay, the ransom was dropped to $10m, after which the gang leaked 26,000 documents onto its blog.
According to analysis by cybersecurity company Digital Shadows, Conti has targeted victims in Russia, suggesting the group is not based there.
3) DarkSide
DarkSide is a relatively new group, having carried out just 59 attacks since it emerged last year, according to BlackFog, 34 of which took place in 2021. But its malware is already widespread, accounting for 11.5% of threats, and it is perhaps the best-known group.
It actively courts a public profile and a reputation for operating ethically: it issues press releases, it has tried (unsuccessfully) to donate some of its proceeds to charity, and it once vowed not to target national infrastructure. Despite that, DarkSide is best known as the perpetrator of the Colonial Pipeline attack which disrupted the supply of oil to the east coast of the US early this year.
DarkSide exemplifies the increasingly professionalised nature of ransomware groups. In addition to its PR efforts, the organisation has established a 'customer service' division to ensure its victims' systems are restored in good order once they pay their ransom. "If you want to gain ... big money from a victim company, then they're going to need to feel that [you are] going to return the data to them, and not just escape with the money," explains David Emm, principal security researcher at Kaspersky.
4) CLOP (aka FANCYCAT)
The group operating the CLOP malware was the first to demand more than $20m in ransom. The target, German IT provider Software AG, refused to pay. The gang has attacked 53 victims in total, including 35 this year, and its malware variant appeared in 11.5% of attacks in May.
Earlier this month, six alleged members of the CLOP gang were arrested in Kiev, following an international investigation including law enforcement agencies from the US and Korea and cryptocurrency exchange Binance. Since then, however, the group has continued to publish data stolen from its targets online.
5) Egregor
Now-defunct ransomware group Maze is credited with inventing the 'double extortion' technique, in which attackers threaten to publish stolen data as well as locking down their victims' systems. The group disbanded last year but many believe that its core members are behind a new threat named Egregor. This group's malware first emerged in September 2020 but accounted for 8.2% of attacks in May 2021.
Egregor, whose name reportedly derives an occult word meaning "the collective energy of a group of people especially when aligned with a common goal," has committed at least 71 attacks across 19 countries worldwide, according to Esentire.
6) DopplePaymer
First spotted in 2019, DopplePaymer is believed to be the group behind the BitPaymer ransomware strain, due to similarities in code, ransom notes, and payment portals. Its malware was present in 6.6% of ransomware attacks from January to May this year, according to BlackFog. The gang has perpetrated 186 attacks, 59 of which have been carried out this year, Esentire found.
The FBI issued a warning about DopplePaymer in December 2020 after a spate of attacks on healthcare systems in Europe led to the death of a patient in Germany. "In September 2020, a DopplePaymer attack against a hospital in Germany left emergency service personnel unable to communicate with the hospital," the FBI reported. "At least one individual requiring emergency services was re-routed to a hospital 20 miles away. This individual later died."
7) Babuk
A smaller ransomware gang, Babuk was only discovered this year. But it is growing quickly and has already attacked five big enterprises, one of which paid $85,000 after negotiations. It accounted for 4.9% of ransomware attacks from January to May this year, according to BlackFog.
The group claims to abide by an ethical code, avoiding NGOs, educational facilities, healthcare and companies with less than $4m in annual revenue. But, according to security company CyberInt, it has targeted private clinics, major universities, and charities that support LGBTQ+ and BLM causes, "the latter likely demonstrating the bigoted views of the threat actor".
8) Ragnar
The group known as Ragnar, whose Ragnar Locker malware accounted for 3% of ransomware attacks this year, was the subject of a flash warning from the FBI last year. In April, the then-unknown group had extorted $11m from an unnamed victim, on the threat of publishing ten terabytes (TB) of company data. "Since then, Ragnar Locker has been deployed against an increasing list of victims, including cloud service providers, communication, construction, travel, and enterprise software companies" the FBI flash warning reads.
9) Hotarus
Also accounting 3% of ransomware attacks from January to May, Hotarus is best known for its attacks on the Ecuadorian Ministry of Finance and the country's largest bank Banco Pichincha. An alleged member of the group posted 6,500 records including email, identity card numbers, and passwords, claiming they were from the Ministry of Finance, corroborated by security researcher Germán Hernández on Twitter.
10) Astro
The final group in BlackFog's top ten ransomware gangs is the group behind the Astro Locker malware. Its ransomware strain is very similar, if not identical, to another threat named Mount Locker, which is known to be less sophisticated than those of other, more prolific gangs. According to researchers at security provider Sophos, there is evidence to suggest that the group rebranded to improve its reputation.






