In today’s increasingly digital world, the more connected organisations become, the more exposed they are to outside threats. A quick glance at the headlines showcases a number of recent attacks – like WannaCry and NotPetya – that have shaken organisations worldwide, demonstrating the significant reputational and financial damage that exists in the wake of a major data breach.

And organizations are starting to take note, realizing it’s a matter of if, not when this type of attack will occur. In fact, according to SailPoint’s Market Pulse Survey, an alarming third (33 per cent) of companies in the UK have experienced 1-2 breaches in the past year, and 43 per cent believe they are likely to be breached in the next 12 months, meaning there’s no end in sight.
These breaches are costly, with the majority of UK businesses (26 per cent) losing up to £19,000 on average. They also vary in their impact to the business, with over half (56 per cent) of UK businesses breached in the last year experiencing business downtime, 46 per cent experiencing financial losses and 34 per cent suffering reputational damage.
A major part of the problem is the lack of visibility into who is doing what and the kind of risk those actions represent – a challenge that can only be addressed by identity, which is the new perimeter in today’s digital world. A user’s identity is the red thread that links people, applications, data and devices in an organisation, which is increasingly more important with the proliferation of the cloud, bring-your-own-device (BYOD), and shadow IT.
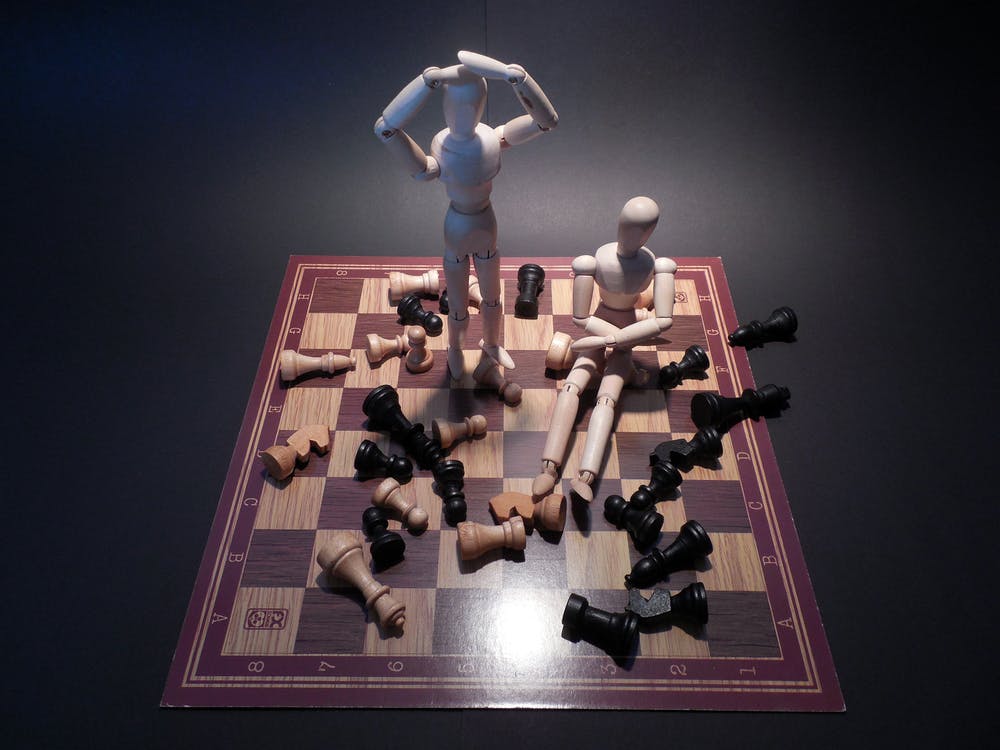
The identity ‘trilemma’
The constant influx of cyber threats is causing headache upon headache for enterprise IT teams who already have difficult jobs and that’s not the only problem they face. Departments outside of IT are adopting software-as-a-service (SaaS) solutions to appease business users, often introducing these technologies without IT oversight. Coupled with an overall lack of employee understanding of what actions can create dangerous exposure points for the organisation, and far more cybersecurity risk is being created outside of the IT department’s field of vision. However, it still falls to IT to mitigate these risks.
The question remains: how can IT protect what they can’t see? The combination of increased access to cloud-based applications, a surge in shadow IT activity that falls outside of IT’s purview and a disregard for company-wide policies has resulted in an identity ‘trilemma’. Outlining corporate policies is a first step in addressing these exposure points, but organisations must take a multipronged approach to identity governance, maintaining awareness of employee access to applications from all locations and across all devices, and then devise ways to secure them.
IT teams in the dark?
In the wake of the data breach pandemic, most organisations will take stock of their current security controls and work to identify where exposure points lie. The increased use of shadow IT and BYOD across organisations means that there is now a proliferation of exposure points within the enterprise that IT does not have direct visibility into. And while seven out of 10 companies have embraced BYOD and shadow IT, less than half have formal policies in place to protect corporate data. This is a dangerous and problematic situation for IT to be in as they work to shore up their organisation’s defences. How can IT prevent and protect areas of exposure that they don’t know about?
With many concerned about shadow IT and BYOD as organisational exposure points, it is clear that enterprises need to not only develop clear-cut corporate identity governance policies, but actively enforce those policies company-wide for comprehensive visibility into IT networks.
Implementing policy
While the majority of risks are created outside of IT, it is still the responsibility of IT leaders to react to today’s workplace trends by implementing and enforcing corporate security identity policies. Despite organisational policies designed to govern access and to help secure the enterprise, there is a disconnect between what is ‘allowed’ and what actually takes place across departments. Of the companies that have such corporate security policies in place, three in 10 reported that their users are not following them.
Clearly, outlining and enforcing corporate security policies will only go so far. Unless organisations become better equipped to control and manage who has access to sensitive information, organisations will remain exposed to security risk. For IT to consistently manage business operations in a secure way, identity must be at the centre of the enterprise’s security structure.
A hybrid environment
Today’s hybrid approach to storage and data access, coupled with the acceleration in cloud adoption makes it challenging for IT leaders to gain full visibility across their entire IT landscape. In tandem with that, even though many enterprises are moving to the cloud first, they still typically have a variety of legacy applications that will remain on-premises. This creates an incredibly complex, hybrid IT environment that needs to be managed and governed holistically.
This presents some clear security challenges. In order to govern the hybrid IT environment, organisations must answer the question – “who has access to what?” This applies to the entire IT ecosystem and is key to gaining visibility into all data, applications and users irrespective of their location or device. This approach is part and parcel to implementing a strong identity governance programme to address the risks of today and tomorrow.
With nearly one third (23 per cent) of UK businesses believing that they are likely to be breached without realising it in the next 12 months, seeking a solution to the identity trilemma is a matter of urgency. Managing and governing identities will allow companies to support and empower their users while securing and governing user access across today’s modern, highly digital enterprise.






