In June, government agencies were subjected to ten times the average volume of attempted ransomware attacks, according to research from security provider SonicWall. These attacks were part of an unprecedented spike in ransomware activity: more attempted attacks have been recorded this year so far than in the whole of 2020.
The second quarter of the year was especially intense, SonicWall’s researchers revealed. “While Q1 was worrying, Q2 was markedly worse — going into spring, ransomware jumped from 115.8 million to 188.9 million, enough to make Q2 the worst quarter for ransomware SonicWall has ever recorded.”
Government agencies were the primary target of the attacks. "Each month in 2021, there have been far more hits on government customers than any other industry," SonicWall's report states. "By June, government customers were getting hit with roughly ten times more ransomware attempts than average."
In the US, the volume of attempted ransomware attacks targeting government employees far outstripped those in other sectors, SonicWall found. So far this year, government workers have been subject to at least 1,000 attempts per month on average, compared with a few hundred at most in retail, healthcare and education.
The ransomware spree is concentrated primarily on targets in the US, which suffered a 180% increase in attempts compared to the first half of last year, up to 227 million. But it is growing faster in Europe, where organisations saw a 234% uptick. UK organisations endured the second-highest volume of attacks, with 14.6 million, followed by Germany with just over 11 million.
Phishing emails are still among the most common vector for ransomware attacks, according to a recent study by security company Cloudian. This is despite the fact that 65% of companies that recorded email-borne ransomware attempts had implemented anti-phishing training for their employees. "This reflects the increasing sophistication of phishing schemes, with attackers now mimicking emails from trusted associates such as high-level executives."
Why are ransomware attacks on the increase?
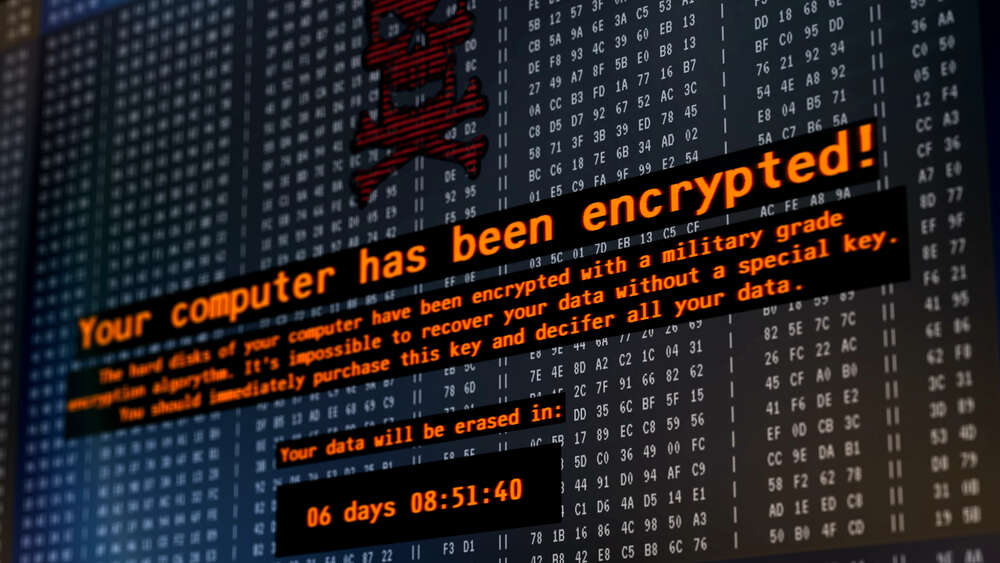
This growing spike in ransomware attempts shows that there is money to be made. According to research by security vendor Sophos, 32% of companies who suffered a ransomware attack had to pay the criminals to decrypt their data in 2020, up by 23% compared to the previous year. This is contrary to the advice of law enforcement agencies.
Recently the US has considered mandating the reporting of cyberattacks to understand the problem further. During a recent senate judiciary hearing reported on by the Washington Post, executive assistant director at CISA Eric Goldstein said "We believe that only about a quarter of ransomware intrusions are actually reported."
Companies who pay the ransom have no guarantee that they will get all of their data back uncorrupted, or that they will not be attacked again. Research by security company Cybereason indicates that, out of respondents surveyed, just 46% regained access to their data following payment and either some or all of the retrieved data was corrupted. Of the organisations that opted to pay the ransom demand, 80% incurred another attack. And of these companies, nearly half (46%) believe these data breaches were at the hands of the same attackers.
Home page image by SynthEx/Shutterstock






