In the past five years, ransomware has evolved from a widespread annoyance to a billion-dollar industry and an existential threat to the global digital economy. This has not been driven by technical advances in cyberattacks, which have remained essentially the same throughout. Instead, it is the way in which criminal groups exploit compromised systems to extort their victims that has evolved. Here’s how ransomware extortion tactics have progressed to date.

The global cost of ransomware
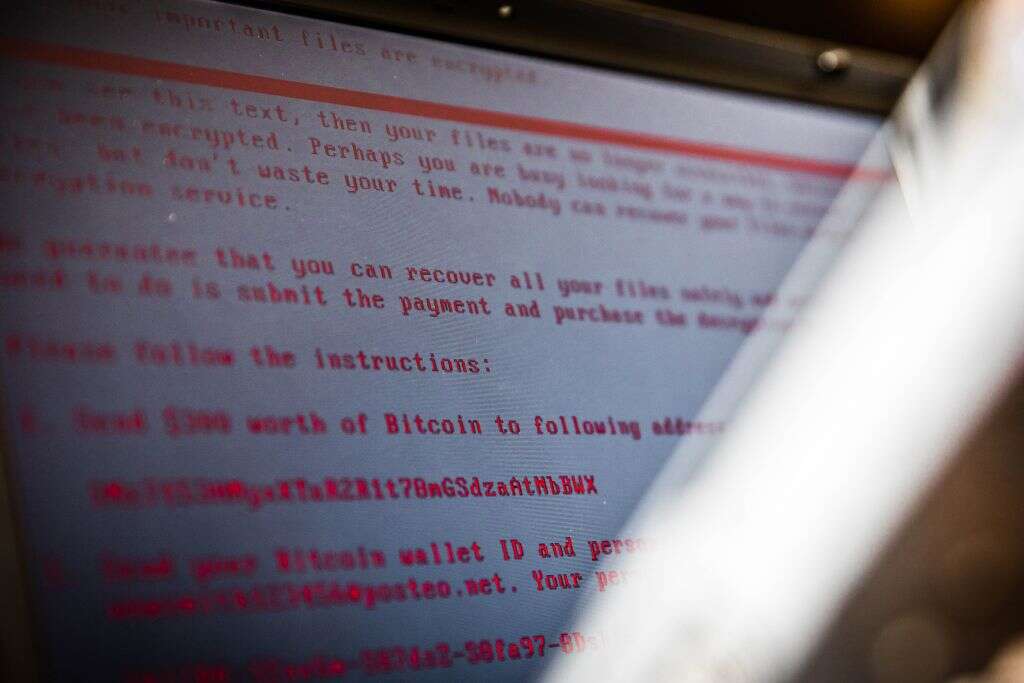
Ten years ago, ransomware attacks were indiscriminate and low value. Criminals would attack any organisation that had been compromised by their malware, and threaten them with either encryption or denial-of-service attack. The typical ransom demand at this time was only a few hundred dollars in bitcoin.
By 2016, ransom payouts worth $10,000 or more were starting to be reported – but that is small change compared to today’s ransom demands. According to research by Palo Alto Networks, the average ransom demand in 2020 was $847,344. The average ransom paid was $312,493 – more than double the 2019 average – with the highest ransom reaching $10m.
And the ransom itself is only part of the cost. According to a survey by Sophos, the average remediation cost of a ransomware attack – which includes the ransom but also downtime and resources required to address the attack – was $1.9m in 2021, up from $760,000 last year.
Researchers at Cyber Security Ventures estimate that the global cost of ransomware will be $20bn this year, up from just $325m in 2015. They predict this figure will grow to $265bn by 2031, by which time a ransomware attack will be launched every two seconds.
How ransomware exploitation tactics have evolved
What has changed over the past five years has not been the sophistication of the attacks themselves. "Ransomware still relies basically on either malicious email [or] poorly secured remote access tools such as remote desktop protocol," explains Ryan Kalember, executive vice president at security company Proofpoint.
Ransomware still relies basically on either malicious email [or] poorly secured remote access tools like remote desktop protocol.
Ryan Kalember, Proofpoint
Instead, it is how ransomware groups use these attacks to extort money from victims that has evolved.
Firstly, attacks have become much more targeted. Instead of threatening any compromised organisations, ransomware groups identify and nurture lucrative targets, a practice known as 'big game hunting'. Campaigns can last months, as attackers research their victims and quietly infiltrate their systems. And as they have become more targeted, ransomware attacks have grown more lucrative, prompting more criminals to get in on the act. There was a 500% increase in ransomware attacks on enterprise organisations in 2019, according to figures published by Forrester at the time.
Secondly, ransomware gangs have added the threat of leaking stolen data online to their arsenal. In November 2019, attackers using the Maze ransomware strain threatened to use email addresses, security certificates and other sensitive information that had been stolen from security vendor Allied Universal as the basis for a malicious spam campaign. To prove that they had the ability, the attackers published a sample of the stolen files – including contracts, medical records, and more – online. This new 'double extortion' technique was soon copied by other groups.
Meanwhile, encrypting data is becoming less significant as an extortion technique. In Sophos' survey, only 54% of respondents said that, during the most significant ransomware attack their organisation suffered in 2021, attackers were successful in encrypting their data, down from 73% in 2020. "This indicates that the adoption of anti-ransomware technology is paying off," Sophos concluded.
Now, an increasingly professional and competitive underground industry is exploring new ways to extract ever more money from targets. "They're limited only by their own creativity in terms of making it very difficult for an organisation not to pay," says Kalember.
Lately, ransomware groups have been using cybersecurity insurance to price their ransoms. "They can read information on the victim's cyber insurance policy and set the ransom at the upper limits of [what the policy will pay out]," explains Jamie MacColl, research analyst in cyber threats and security at UK think tank the Royal United Services Institute. "It's very hard for the victim, or the ransom negotiator, or the insurance company, or whoever's involved in that decision-making process, to then say 'this is too high for us,' as the criminals can just present a screenshot of a document that says their coverage is $10m."
Some of the groups are threatening to short stocks or leak the news of a breach to stock brokers.
Jamie MacColl, RUSI
Some criminals are using stolen personal information to cold call employees of target organisations, to push them to press their bosses to pay the ransom. And now, groups are looking to stock markets to increase the pressure on their victims. "Some of the groups are threatening to short stocks or leak the news of a breach to stock brokers," says MacColl. So far, these threats have not come to fruition.
The future of ransomware exploitation tactics
This year has seen a spate of high-profile organisations falling victim to ransomware attacks, such as the Colonial Pipeline and the Irish health service. This may not last forever, MacColl explains, as hitting conspicuous targets may be against the attackers' interests. "There's a fine line that they have to tread between creating public pressure on victims to increase the likelihood that they'll pay, and going after targets that create so much public awareness that pressure on governments to go after them more aggressively increases."
Instead, experts expect the nature of the technical attacks to evolve. Bharat Mistry, technical director of the UK and Ireland at security company Trend Micro, believes that the practice of encrypting a target organisation's entire systems will decline in favour of easier but equally disruptive tactics such as tampering with critical data. "They've done something, but they're not telling you what they've done," he says. "You are still online, but what they've done is change the integrity of the data, [and] you're still going to have to pay them."
Kalember believes organisations' cloud-based systems may come under fire. "Cloud has a lot of security advantages, but it also has the disadvantage that you can do a lot of things very quickly across an entire environment," he explains. "You could encrypt everything that is sitting in three buckets on [large cloud providers] and no one backs that stuff up. Rolling back would be a nightmare."
Given the pace of innovation in ransomware exploitation tactics, cracking down on individual techniques is unlikely to stem the ongoing global spree, says Kalember. Instead, it will require governments to police the cryptocurrencies they use to receive funds, he argues. "A policy-based response that runs through cryptocurrency is the only answer," he says. "Limiting their ability to do a specific extortion technique will not be as good as limiting their ability to actually monetize the access that they get right now."






