Tanium
Success
You have successfully submitted your enquiry. Someone from our company will respond ASAP
Tanium

White Papers
Gartner Magic Quadrant for Endpoint Management Tools 2026
Rapid endpoint proliferation and an expanding attack surface are reshaping the endpoint management market. The Gartner® Magic Quadrant™ cuts through the market noise, market direction, and simplifying the decision-making process. Actionable clarity in a crowded market Defensible decision-making Proven track records of vision and momentum Find out what capabilities resulted in Tanium’s recognition as a Leader.
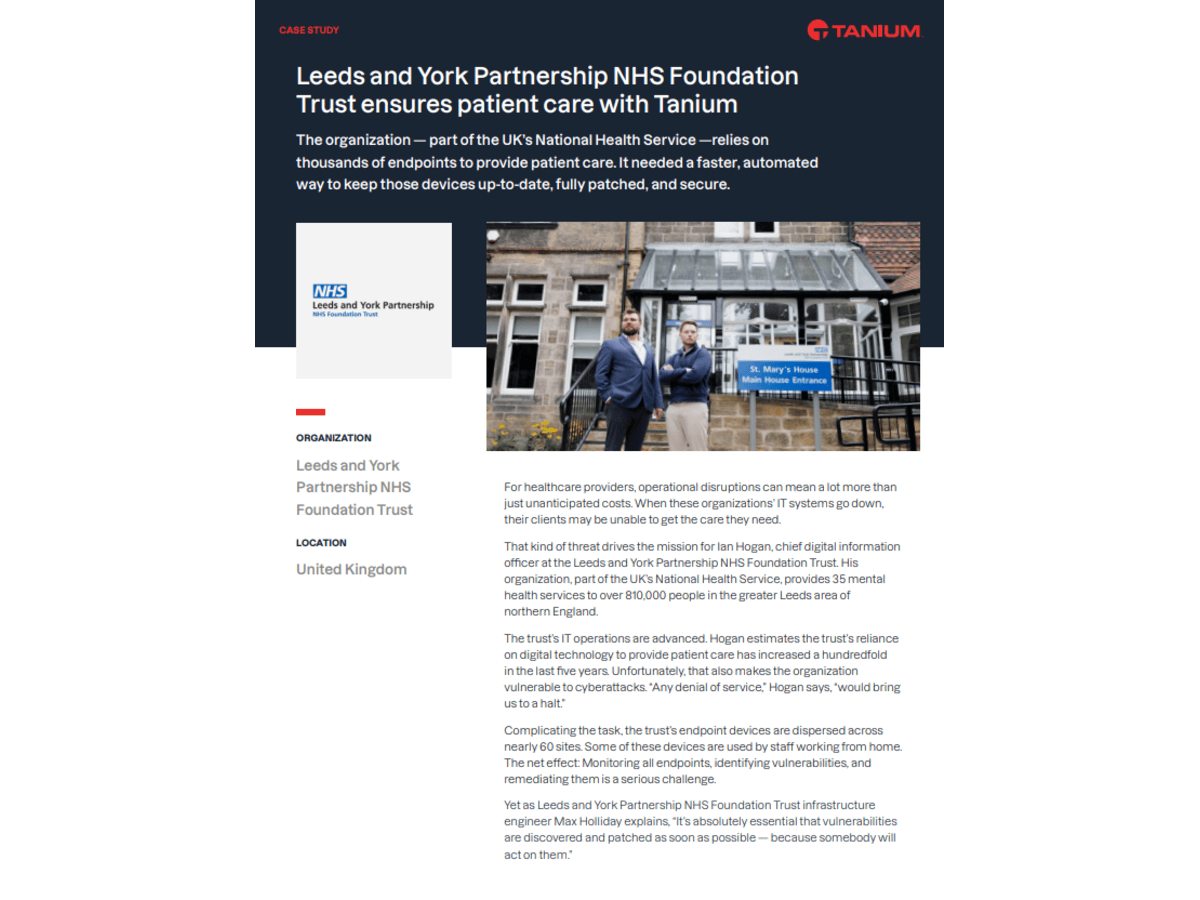
Leeds and York Partnership NHS Foundation Trust ensures patient care with Tanium
Leeds NHS ensures patient care with Tanium. The organization — part of the UK’s National Health Service —relies on thousands of endpoints to provide patient care. It needed a faster, automated way to keep those devices up-to-date, fully patched, and secure.
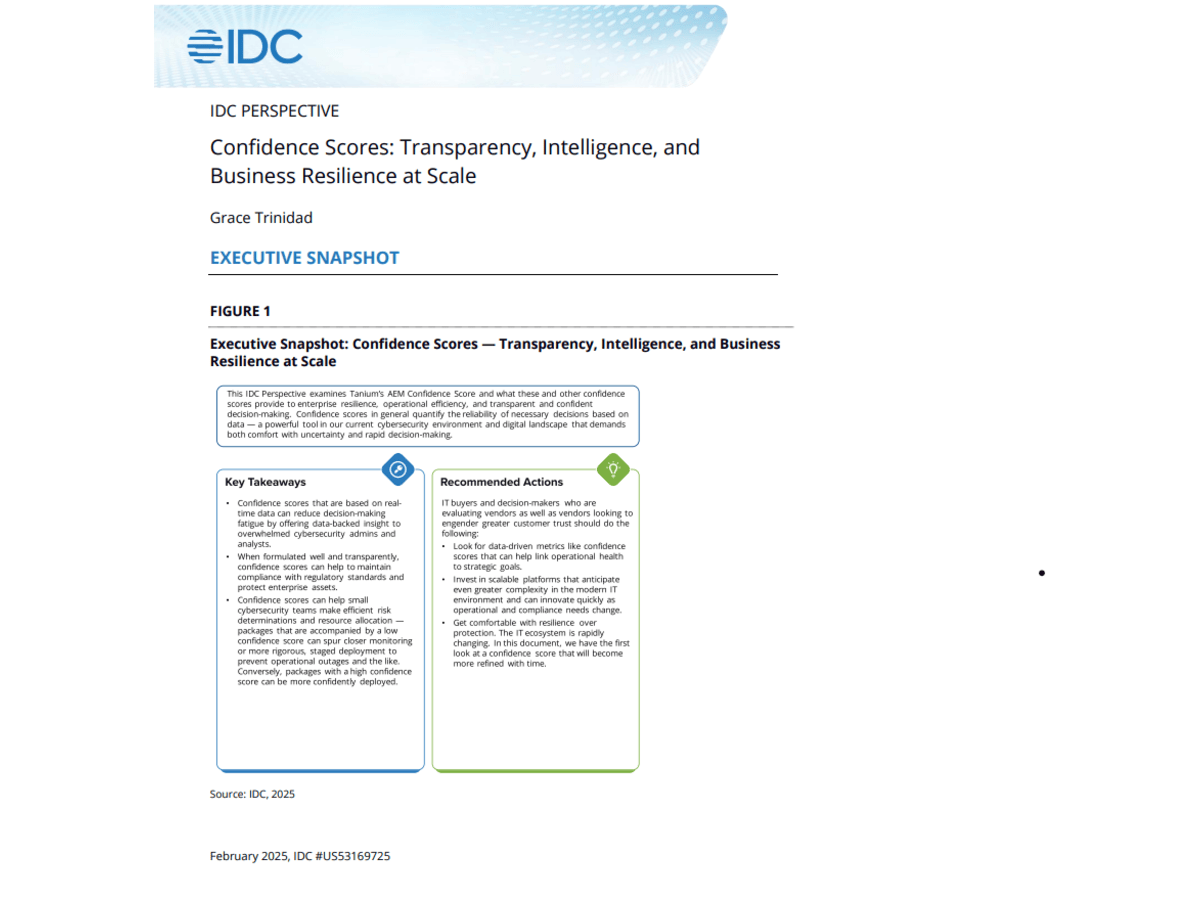
IDC Perspective Confidence Scores: Transparency, Intelligence, and Business Resilience at Scale
In today’s hyper-connected and complex enterprise environments, the role of endpoint management and data-driven decision-making is more critical than ever. IT leaders should: Understand the strategic role of confidence scores in decision-making Learn the key features and functionality when evaluating vendors Discover how confidence scores might evolve and impact the future This IDC Perspective is for executives striving to future-proof their enterprises and explores how Tanium’s recent addition of confidence scores can help.
Achieving complete endpoint visibility with Tanium
Imagine sailing a ship through uncharted waters – without map or compass – and at any time the sail and rigging could disappear. Unfortunately, this is what it can feel like to manage an IT environment without complete endpoint visibility. This helpful guide maps out how Tanium can become your North Star in unpredictable tides. Download it now to find out how Tanium is built to deliver complete visibility and much more.
The Growing Role of AI in Endpoint Management and Security Convergence
Organizations continue to face increasing complexity in endpoint management and security that is driven by the rapid expansion of remote work, rising device and OS sprawl, vulnerability management and incident response challenges, and continuing threats like ransomware. At the same time, the growing influence of AI and automation is reshaping both offensive and defensive strategies—empowering defenders with new tools while enabling bad actors to launch more sophisticated attacks. To gain further insight into these trends, how organizations are attempting to overcome challenges, and the results of their efforts, Enterprise Strategy Group, now part of Omdia, surveyed 364 IT and cybersecurity professionals in North America (US and Canada) responsible for evaluating, purchasing, and supporting endpoint management and/or security technologies.
The Interconnection Between People Process and Technology
People, Process and Technology are the cornerstones of all technological advancement within any organisation. With the dawn of automation and AI upon us, how are industry leaders navigating the growing complexity, security threats and 'the need' for automation? This new research, in partnership with Chief Disruptor, acts as an IT pulse check - providing real-world open and honest insight from within the world's largest organisations. Hear from leaders as they share their current challenges and also their recipes for success when it comes to interconnecting your people, your processes and technology.
Enhance visibility and reduce risk – Tanium ITX and Security Operations for ServiceNow – DE
Transformieren Sie Ihre IT- und Sicherheitsabläufe mit der leistungsstarken Integration von Tanium und ServiceNow - Erleben Sie eine beispiellose Echtzeittransparenz Ihrer Endpunkte, die es Ihnen ermöglicht, Schwachstellen schnell zu identifizieren und zu entschärfen. Profitieren Sie von der Automatisierung Ihrer Arbeitsabläufe, indem Sie den manuellen Aufwand reduzieren und die Effizienz beim Patch-Management und bei der Reaktion auf Vorfälle steigern. Erfahren Sie, wie Sie die Kluft zwischen IT-, Sicherheits- und Risikoteams überbrücken und so Ihre Sicherheitslage verbessern können.
Enhance visibility and reduce risk – Tanium ITX and Security Operations for ServiceNow – FR
Améliorez vos opérations informatiques et de sécurité grâce à l'intégration transparente de Tanium ITX et de ServiceNow - Découvrez comment vous pouvez obtenir une visibilité complète de vos actifs et réduire les risques grâce à des données en temps réel sur les points finaux. Favorisez une meilleure collaboration entre les équipes informatiques, de sécurité et de gestion des risques grâce à des données et des informations unifiées, tout en renforçant votre posture de sécurité et en rationalisant les opérations grâce aux capacités inégalées de Tanium ITX et de ServiceNow.
Enhance visibility and reduce risk – Tanium ITX and Security Operations for ServiceNow
Transform your IT and security operations with the powerful integration of Tanium and ServiceNow - Experience unprecedented real-time visibility of your endpoints, enabling you to quickly identify and mitigate vulnerabilities. Benefit from workflow automation by reducing manual effort and increasing efficiency in patch management and incident response. Learn how to bridge the gap between IT, security and risk teams to improve your security posture.
AstraZeneca – DE
Kein IT-System ist eine Insel. Deshalb kann ein Unternehmen, das seine Anwendungen, Daten, APIs und Geräte integriert, von zusätzlicher Effizienz, Produktivität und Agilität profitieren. Das ist der Fall bei AstraZeneca. Mit einem Jahresumsatz von 45,8 Milliarden US-Dollar im Jahr 2023 hat das in Großbritannien ansässige Pharmaunternehmen, das 1999 aus der Fusion von Astra AB und Zeneca PLC hervorging, heute eine Menge zu integrieren. Dazu gehören: * Mehr als 89.000 Mitarbeiter * In mehr als 100 Ländern tätig * Und etwa 125.000 Endgeräte, die von privaten Laptops bis hin zu Unternehmensservern reichen Erfahren Sie, wie AstraZeneca die Vorteile der Integration von Tanium mit Microsoft und ServiceNow nutzt.
AstraZeneca – FR
Aucun système informatique n'est isolé. C'est pourquoi une organisation qui intègre ses applications, ses données, ses API et ses appareils peut bénéficier d'une efficacité, d'une productivité et d'une souplesse accrues. C'est le cas d'AstraZeneca. Avec un chiffre d'affaires annuel de 45,8 milliards de dollars en 2023, cette société pharmaceutique basée au Royaume-Uni, issue de la fusion en 1999 d'Astra AB et de Zeneca PLC, a aujourd'hui beaucoup de choses à intégrer. Cela comprend *plus de 89 000 employés *une présence dans plus de 100 pays *et quelque 125 000 dispositifs d'extrémité allant des ordinateurs portables personnels aux serveurs d'entreprise Découvrez comment AstraZeneca tire parti des intégrations de Tanium avec Microsoft et ServiceNow.
Ultimate Guide to Endpoint Management
The Ultimate Guide to Endpoint Management is an A-to-Z guide providing a foundational overview for IT and cybersecurity professionals of all skill levels. Explore chapters packed with research and guidance, usable strategies and advice from industry experts. Plus, dive deeper into topics that matter most such as endpoint policies, the key components of endpoint management, and how to select the right platform for your organization.
Tanium Autonomous Endpoint Managment (AEM) – AEM Overview
Tanium AEM leverages real-time insights from all Tanium cloud-managed endpoints to recommend and automate changes on endpoints within a customer’s environment in a safe, scalable way with its real-time platform. It empowers IT and Security teams to confidently and efficiently scale operations and improve the security posture of the environment.
AstraZeneca
No IT system is an island. That’s why an organization that integrates its applications, data, APIs, and devices can benefit from added efficiency, productivity, and agility. That’s the case for AstraZeneca. With annual sales of $45.8 billion in 2023, the UK-based pharmaceutical company has a lot to integrate. That includes more than 89,000 employees operating in more than 100 countries, and some 125,000 endpoint devices ranging from personal laptops to enterprise servers. Learn how AstraZeneca keeps its IT systems and vital research activities up and running with the help of Tanium.
Operationalizing the NIST Cybersecurity Framework (CSF) 2.0 with Tanium
Operationalizing the NIST Cybersecurity Framework 2.0 with Tanium. NIST CSF 2.0 represents a framework for building resilience and alignment in cybersecurity. Tanium can help support organizations operationalize the framework to achieve robust security and compliance in an ever-evolving threat landscape.
Digital Employee Experience (DEX)
Think of how much the workplace has changed over the past few years: In early 2020, many, if not most, corporate employees worked from central offices and exclusively used organizational devices to access data via firewall-protected corporate networks. Fast-forward to today, where hybrid or remote work arrangements are commonplace, and employees often use personal devices to access sensitive data through their home networks. With this abrupt shift to remote work during the pandemic, the subsequent onset of hybrid workforces, and ongoing digital transformation initiatives, the employee experience as we knew it no longer exists. Furthermore, this discrepancy between how organizations think of employee experiences, and what their employees are actually experiencing, is creating a number of costly and frustrating challenges. Download to find out more.
Enhance visibility and reduce risk with Tanium ITX and Security Operations for ServiceNow
Transform your IT and security operations with the powerful integration of Tanium and ServiceNow - Experience unprecedented real-time visibility of your endpoints, enabling you to quickly identify and mitigate vulnerabilities. Benefit from workflow automation by reducing manual effort and increasing efficiency in patch management and incident response. Learn how to bridge the gap between IT, security and risk teams to improve your security posture.
Tools designed for security could be your biggest cybersecurity threat
Digital transformation has changed how businesses operate, making them more agile and responsive to the markets they serve. But this transformation has come at a cost — a rambling web of software tools and applications, cloud infrastructures, and decentralized application services. And this complexity presents a big challenge to cybersecurity teams. In tandem with digital transformation initiatives has been the rise of the remote workforce, making traditional network perimeters a thing of the past. Many IT resources now operate outside the corporate firewall and are vulnerable to cyber threats of all kinds. The result? A much larger and more varied attack surface. Download to find out more.
3 Steps to Accelerating Microsoft Defender for Endpoint with Tanium
3 Steps to Accelerating Microsoft Defender for Endpoint with Tanium. Tanium and Microsoft empower more effective and resilient IT operations and security at scale by combining unprecedented analysis and automation with realtime visibility, control, and remediation.
AstraZeneca takes advantage of Tanium’s integrations with Microsoft & ServiceNow
No IT system is an island. That’s why an organization that integrates its applications, data, APIs, and devices can benefit from added efficiency, productivity, and agility. That’s the case for AstraZeneca. With annual sales of $45.8 billion in 2023, the UK-based pharmaceutical company, formed by the 1999 merger of Astra AB and Zeneca PLC, today has a lot to integrate. That includes more than 89,000 employees operating in more than 100 countries, and some 125,000 endpoint devices ranging from personal laptops to enterprise servers. Keeping all those endpoint devices running is a big, vital job. “Leadership gauges my success on system availability,” says Jeff Haskill, AstraZeneca’sVP of enterprise technology services. “Can they do their research to developmedicines and reach patients? If we have an outage, the medicine literallystops moving.” Research forms a huge part of AstraZeneca’s work. The company employsover 13,000 R&D specialists – almost 15% of its total workforce – in five research centers worldwide. R&D investments last year totaled $10.9 billion, almost a quarter of annual revenue. Looking ahead, AstraZeneca says it intends to develop at least 15 new medicines by 2030. Download to find out more.
Cybersecurity in Europe
The cybersecurity landscape in Europe is as diverse as the 44 countries in it. Their cyber outlook reflects each one’s varying attitudes towards risk, privacy, and security as well as the key organisations that operate nationally or regionally. Despite that diverse outlook, Europe’s biggest enterprises are united in the challenge they face not only in preventing a cyberattack - whether it is delivered through phishing attacks, supply chain hacks, or social engineered targeting - but in being resilient enough to recover from one when it happens. Taking steps to defend against attack will not guarantee that you can prevent one. But planning to be as resilient as possible does give you the best chance to recover. Forewarned is forearmed. Organisations that take a mainly proactive, preventative approach to cybersecurity are significantly less likely to have experienced a cyberattack or data breach than those who adopt a resigned, reactive approach. Having the right toolset in place will help, as will adopting a zero-trust defence which assumes that there is a breach and so verifies each request as though it originates from an open network. To learn about Europe’s cybersecurity landscape and give yourself the best chance of being resilient enough to recover from a cyberattack, download the whitepaper here.
Views from the c-suite: why endpoint management is more critical than ever before
Cyber threats like ransomware are increasing, and endpoints are more varied, numerous, and distributed than ever before. By following the strategies outlined in Views from the C-suite: Why endpoint management is more critical than ever before, security teams can reduce the risk of cyberattacks and ensure that when attacks occur, they can be contained quickly and efficiently. Download to find out more.
The Essential Eight
The Essential Eight is a baseline set of mitigation strategies that the Australian Cyber Security Centre (ACSC) has recommended to make it harder for adversaries to compromise computer systems based on actual incident data. While implementation of the Essential Eight does not guarantee against a successful attack, the objective is aimed at significantly reducing the attack surface. Learn how Tanium is assisting organisations with increasing their maturity levels and overall compliance through this new whitepaper. Download to find out more.
End-to-end Management Across Your IT and OT Estate
Manufacturers are evolving at a rapid rate, centred around automation and digitalisation; the race to drive productivity and profitability is on. However, the challenges of today’s stark macroeconomic environment, a continual need for regulatory compliance, and legacy digital infrastructure all are hindering transformation. Every manufacturer's IT estate is vastly different and the existing complexity of legacy IT and OT technology and equipment is becoming a prime target for ransomware attacks. Our new research report details the state of play with IT & OT modernisation and how visibility should be at the heart of your transformation strategy. Download the paper here:
The Complex Environment Facing Financial Services
The financial services industry is in a state of flux. The global landscape shift caused by the pandemic caught the sector off-guard and accelerated the need to abandon conformity and transform to meet the needs of a new digitally-driven world. The sector is at a tipping point in its embrace of digital transformation, and disruptive technologies such as Artificial Intelligence (AI), Machine Learning (ML), cloud services, advanced analytics and blockchain are leading the way in enabling new services and capabilities. However, new technologies bring new challenges, new opportunities and further compliance responsibilities. Download our new research report to learn about the future of the banking/insurance and what it means for cybersecurity as institutions seek to manage risk, secure technology, and drive innovation.
Full visibility and real-time threat response: Helping retailers achieve proactive IT Security
The risk of a cyberattack, and its potential consequences, are a persistent threat for the retail industry. The risk is an additional worry on top of today’s significant current concerns: inflation, supply chain challenges, the impact of global conflicts and the ever-greater importance of e-commerce, which have all led to fundamental shifts in the demands on retailers' IT departments. Such are the challenges that not all of them are always adequately dealt with. With obsolete technology, a lack of visibility of the overall IT estate, and a backdrop of continuing cyberattacks, the risk to retailers’ reputations of delivering a poor customer experience through a breach or latency issues is one which must be addressed as an absolute priority. To learn more about the risks being faced by retailers and see how they can be overcome, download the whitepaper here.