Joining an ever growing list of companies hit by mega breaches, Weebly has confirmed its systems have been hacked in a breach affecting not only millions of users, but also tens of millions of websites.
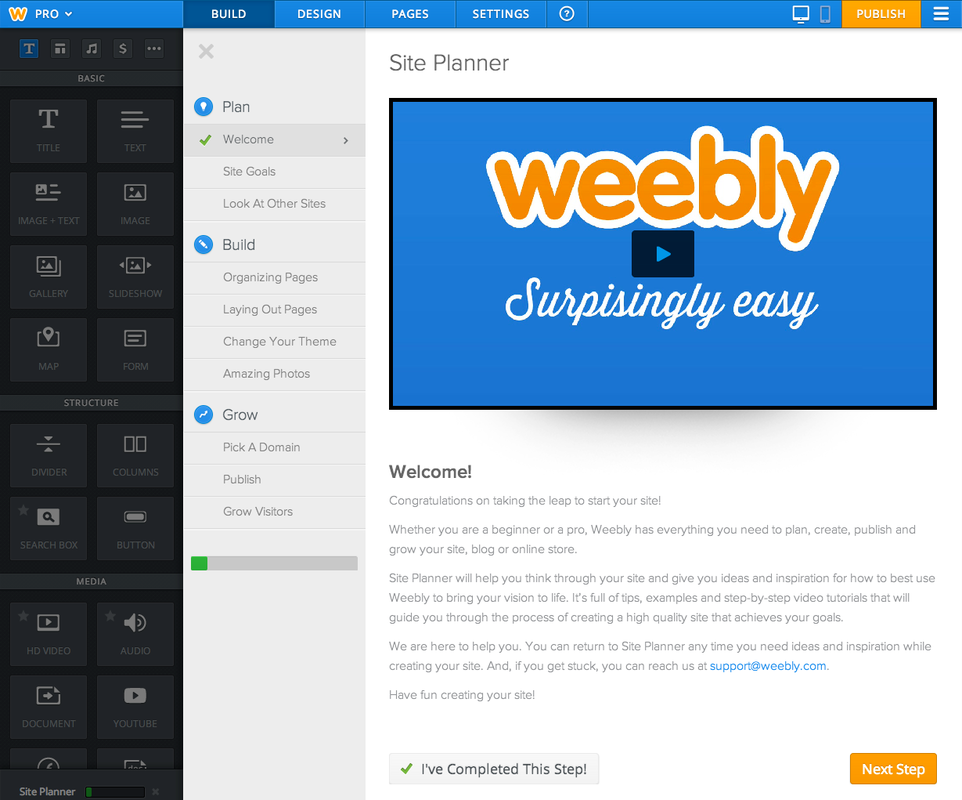
Weebly, a San Francisco-based company which lets people build websites, was cited by ZDNet as saying:
“At this point we do not have evidence of any customer website being improperly accessed.”
“We do not store any full credit card numbers on Weebly servers, and at this time we’re

not aware that any credit card information that can be used for fraudulent charges was part of this incident.”
According to breach notification site LeakedSource, more than 43.4 million accounts were stolen in the attack, thought to have been carried out in February. In a summary of the hack, LeakedSouce reported:
“Well known San-Francisco based “drag-n-drop” website creator Weebly.com had information on 43,430,316 users leaked from its main database in February of 2016. This database was provided to us by an anonymous source.
“Each record in this mega breach contains a username, email address, password and IP address. Unlike nearly every other hack, the co-founder and CTO of Weebly Chris Fanini fortunately did not have his head buried deeply in the sand and actually responded to our communication requests. We have been working with them to ensure the security of their users meaning password resets as well as notification emails are now being sent out.”

LeakedSource also alleges that Foursquare, a search-and-discovery mobile app, has also fallen victim to a breach – although little details were revealed as to when the attack may have occurred.
LeakedSource claims that more than 22.5 million accounts were stolen in an alleged breach, with ZDNet confirming that a sample of the supposed stolen accounts included email address, first and last name, gender, location, Facebook ID and Twitter username.
However, a spokesperson for Foursquare told ZDNet that ‘no breach has occurred’ following an internal investigation.
Commenting on the mega breach, Imperva’s Deepak Patel said: “The ease of getting millions of stolen credentials, with the fact that users will always continue to reuse passwords simply because they are human, makes brute force attacks more effective than ever and forces application providers to take proper measures to protect their users.
“As we see again in this case, data from breaches is hot merchandise on both sides of the legitimacy fence with the security marketplace on one side and the dark market on the other. To prevent brute force attacks, security officers should not rely on password policies only, but should take specific detection measures like rate limiting login attempts, detecting login attempts from automated browsers, treating with caution logins from unexpected countries and anonymous sources, and comparing login data to popular passwords and stolen credentials.”






