When you think about cyber security and cybercrime, what immediately springs to mind? Ransomware, fraud, dark web, phishing, malware – all the popular headline grabbers are now firmly in both the consciousness of the public and business alike.

However, although any recognition and raised awareness of cyber security should be welcomed, cyber security is suffering from an attack of tunnel vision. The cybercrime landscape is evolving at break-neck speed, with tactics and methods of attacks extending past the now-familiar ransomware and DDoS to multifaceted attacks that incorporate multiple attack vectors.
As businesses face pressure from all sides, from customers, investors and regulators, how can we keep pace with the evolving cybercrime landscape?
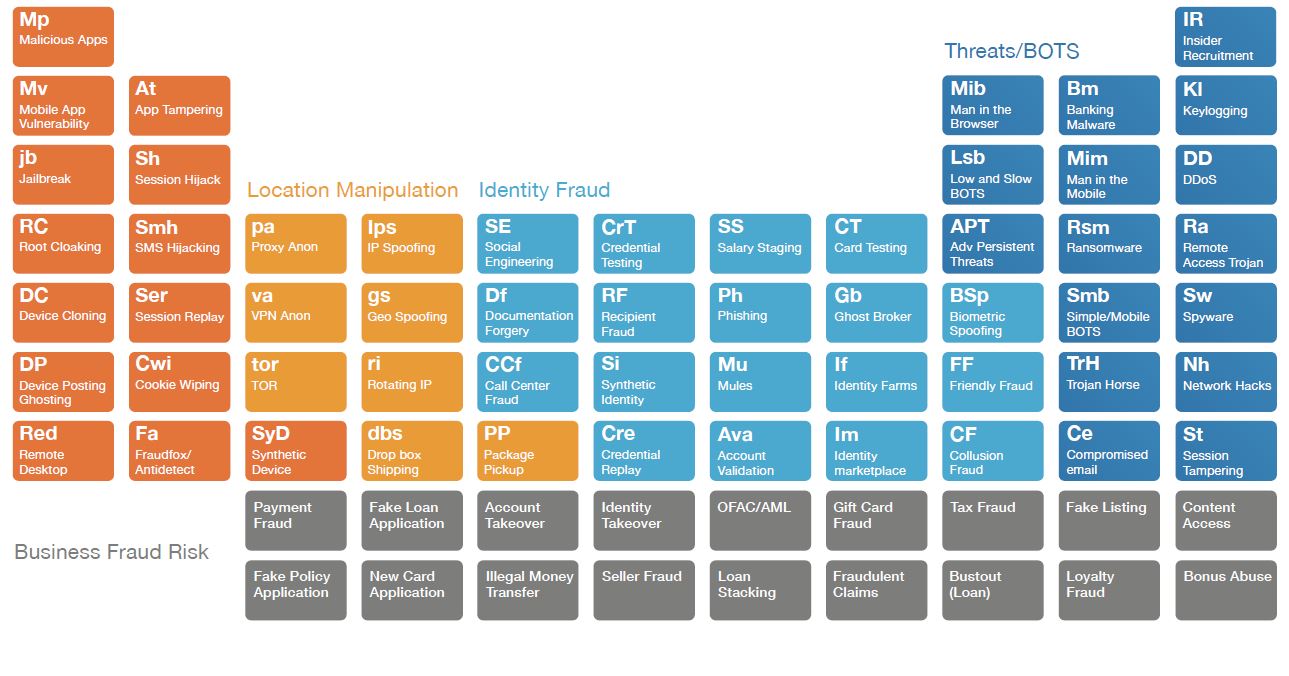
ThreatMetrix has a novel, but effective, way of visualising the ever complex threat landscape, having created a Periodic Table of Cybercrime Attacks. ThreatMetrix has emerged as an astute commentator on the evolving threat landscape, having launched its first cybercrime report three years ago. However, over those years a trend emerged which pushed the security company into creating their own visual representation of cybercrime, as Vanita Pandey told CBR:
“Over the past three years, we have seen attack vectors evolve as cyber-attacks have grown in size, complexity and frequency. Simple, single-vector attacks are rapidly being replaced by complex, multi-vector, globally networked attacks that are powered by identity testing bot attacks and pitch perfect social engineering stunts.
“For this reason, the way we present and analyse different attack vectors was being brought into sharper and sharper focus. We wanted a better way to visually make sense of attacks and to understand the intricate connectivity of different types, groups and approaches to cybercrime. “
The periodic table format provided the digital identity company with an ideal way in which to visualise and make sense of attacks. The scientific elements were replaced with specific attacks, with said attacks grouped together in their appropriate ‘family’. With business risks represented in place of the Lanthanides and the Actinides, the table was ideal in visualising how different types of attacks sat within broader overall groups.
 “To me, the periodic table represents one of the best understood models of categorization,” said Pandey, the Vice President of Product Marketing at ThreatMetrix.
“To me, the periodic table represents one of the best understood models of categorization,” said Pandey, the Vice President of Product Marketing at ThreatMetrix.
“We may not remember much from our secondary school Chemistry class or we may struggle to name the first 5 elements, but the periodic table has universal recall and recognition. It also automatically prepares the reader to expect a large amount of information, albeit categorized in an organized manner.
“Using this approach helped us to broadly categorize attacks into four key areas: device spoofing, location manipulation, identity fraud, and threats and bots, and visually represent the different individual attack vectors that could fall under these broad groups. It also gave us a clever way to demonstrate the intricate and interconnected make-up of attacks that we see in the Network, and help our customers develop more effective strategies to mitigate them.”
The benefit of the table is twofold – it not only shows just how comprehensive and interconnected the cybercrime landscape has become, but it also allows businesses to anticipate different risks they may face. Part of the development of the table was seeing how criminals can combine different elements to attack a business which, as Pandey told CBR, shows how the table “takes on quite a dynamic persona as we examine how different elements can form different combinations of attacks across industries.”
“We can see how a bank account takeover might begin with a low and slow bot attack, which leads to identity theft, a social engineering attack which installs some remote access software, which then results in a session hijack, then perhaps a money transfer to a mule account which could well breach OFAC / AML legislation,” said Pandey, explaining how the dots can be connected using the table.
Pandey went on to explain that the fraudster could take the initial identity theft that was harnessed via the bot attack and simultaneously use it to take out a fake insurance policy. This part of the fraud could be done via a ghost broker scheme which relies on document forgery. Fully highlighting the depths of the cyber rabbit hole, this could also be part of a collusion with a criminal network that results in an illegal money transfer.
 “Likewise, that illegal money transfer for the original bank account takeover, could fund an illegal gambling syndicate,” Pandey told CBR.
“Likewise, that illegal money transfer for the original bank account takeover, could fund an illegal gambling syndicate,” Pandey told CBR.
“So this just seeks to show that categorizing and labelling different methods of attack can help us better understand the complex and interconnected nature of fraud in 2017.”
Maybe coming as no surprise from a security company concerned with users’ digital identities, Pandey names identity spoofing attacks as the “most pernicious attacks in the Network.” However, the thinking behind such a statement makes sense, with people able to buy anti-malware software or replace a compromised device – they cannot, however, buy a new identity.
“As cybercriminals get smarter, it becomes harder and harder for businesses to genuinely understand who they are transacting with: cybercriminals are becoming so adept at behaving like legitimate customers using a patchwork quilt of stolen identity data that their fraudulent transactions often appear wholly legitimate,” said Pandey.
“In addition, I think insider fraud is a big threat to businesses as we move into the latter half of 2017. Insider fraud played a big part in many of the high profile financial services breaches that made headlines last year. It isn’t just about looking to securing your customer base, but also ensuring employees are vetted with the same rigour.”
Like the cyber landscape, the periodic table will continue to evolve, with customers already asking ThreatMetrix about collaborating and adding vectors such as piracy. As new patterns emerge, the challenge may not be in how the periodic table evolves, but actually how cybercrime is categorised as it continues to morph and evolve.
The periodic table serves as a visual cure for all those businesses suffering from tunnel vision, obsessing and pouring resources into one or two attack vectors. No attack vector should be viewed on its own, with such a strategy pure folly in today’s interconnected threat landscape.
“For businesses, the key now is to be prepared for new forms of attacks that can leverage any of the attack surfaces or vectors,” Pandey concluded.






