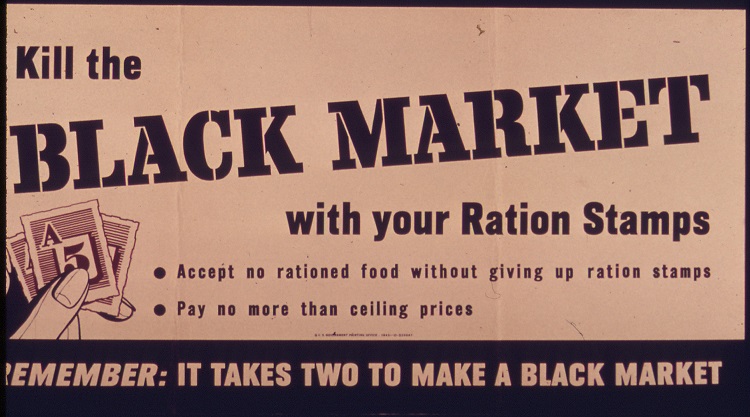
Black markets, defined as underground economies in which goods or services are traded illegally, tend to flourish in wartime. During wartime, restrictions are often placed on resources needed for the war effort, with black markets surfacing to supply rationed goods at inflated prices. Black markets were widespread in World War II, while Prohibition in the United States serves to highlight how black markets seize upon lucrative opportunities at opportune moments in history.
The emergence of a new kind of warfare is again seeing the emergence of underground economies, but this warfare is not fought on the battlefield – it is being fought in cyberspace.
The rise of darknet market websites such as Silk Road have emerged selling compromised credentials, malware, digital goods, weapons and drugs.
These black markets, make no mistake about it, are big business. In the criminal complaint brought against founder Ross Ulbricht, Silk Road was found to have made $1.2 billion in revenue and $79.8 million in commission between 2011 and 2013 alone. Remember, that number is just for Silk Road and does not take into account the numerous BitTorrent sites and peer-to-peer file sharing networks profiteering from the illegal buying and selling of goods.
Illegal businesses, just like their legitimate counterparts, are always seeking new revenue streams, and it seems the darknet underworld has got a lucrative new revenue stream set in its crosshairs – the Internet of Things. The IoT described as a lucrative revenue stream is more than accurate, with Gartner putting the value of the IoT black market at more than $5bn by 2020.
The IoT tradable commodity is, of course, data, and with the promise of 25 billion connected ‘things’ by 2020, the amount of data to be sold and bought could be monumental in size.
It is not just the amount of data which raises concerns, but the type of data generated. Those 25 billion connected ‘things’ have the potential to collect intimate details of our everyday environment, due largely to the fact that the IoT is relevant in nearly every industry – our finances, homes, cars, even the clothes we wear can generate and transmit data.
It is this growing proliferation in IoT data which, as Tim Erlin, Director of Security and Product Management at Tripwire told CBR, is to blame for attracting the attention of cybercriminals.
"As we rely more and more on data produced by IoT devices, the value of controlling that data increases. At some point, it will pass the threshold from ‘interesting security research project’ to ‘profitable criminal enterprise.’ As soon as the target is big enough, organized crime finds a way to get involved."
Cybercriminals have also seized upon the fact that the IoT, at this time, is a relatively easy target. Nick Pollard, UK General Manager at Guidance Software, told CBR:
"As the vast scope of the IoT broadens as well as the security risks associated with the IoT, manufacturers of IoT devices perhaps do not have resources available to ensure that every loophole or flaw has been covered. The potential therefore exist for successful security breaches to be exploited on a black market."
The IoT money maker is, as previously mentioned, data, and products and services enabling the theft of data, and the selling of already stolen data, will fuel the IoT black market.
This is not a new business model, with the market in stolen data already doing booming business in cybercriminal marketplaces today – for a mere $190 you can buy bank login credentials, while a meager $20 to $35 can buy stolen credit and debit cards in the UK.
However, data theft is only one of two possible attack scenarios arising from data on the IoT black market. The other attack scenario is data manipulation – a well known, and well regarded, current method used to make data easier to view and analyse.
Data manipulation is used by criminals for two purposes – the first is to provide the wrong information to those using data, while the second is silent manipulation. Silent manipulation, as Quocirca’s Clive Longbottom tells CBR, draws yet more parallels with physical warfare; as physical war leads to casualties and death, so too may silent manipulation.
"The second, and more dangerous, is the silent manipulation. As an example here would be the SCADA attack on Iran a couple of years back. By subverting the operating system of IoT devices, the black hats (OK – possibly foreign government workers) managed to make the uranium centrifuges spin too fast and so break down. In this case, it forced Iran to the negotiating table – in other cases, such as with nuclear reactors, armaments and pharmaceuticals, it could be used to create mass-scale deaths."
As not to be blamed for fanning the flames of IoT panic, this type of data manipulation will only be used in cases where the cybercriminals can get a good return on investment – this means that large enterprises, financial institutions and government agencies will most likely be the target. Tripwire’s Tim Erlin explained to CBR:
"Data manipulation will be reserved for high value use cases, as it will be more costly to implement and provide less ongoing profit for the criminal. At some point, it will be possible to purchase altered sensors or firmware that allows a third party to affect outcomes by altering the data collected. "
Although the loss of life is at the extreme end of the scale, data manipulation is a real threat to global businesses. Banks, for example, could have their whole security systems undermined, thus endangering customer trust and damaging brand reputation – and reputation, as we all know, only needs one data or security breach to sink a brand in the publics’ eye. Quocirca’s Clive Longbottom said:
"There is a new threat around two factor authentication where banks have been forced to move from a one time code sent via SMS to one being sent by a voice call. It is possible for a black hat to manipulate the phone so that it won’t ring, but will automatically forward specific calls to a device of their choice. Therefore, if they have the basic details of your bank account, they can initiate a transaction, and when the second factor is required, they get it nominally sent to your phone – but receive it on theirs instead."
This example of 2FA in banking crosses over to the consumer side of the IoT, an area which is just as much under threat from the IoT black market as businesses. Smart home devices, in particular, offer a window into your day-to-day life, and by gathering this data thieves can map patterns exposing your daily routines. Longbottom said:
"Heating cycles; use of smart appliances; access to internet-based services and so on will all show when you are active and when you are not – and when you are not at home. Thieves can then use this to know when is the best time to break in to your house and how long they will have. With broad access they can then manipulate security systems, such as smart locks and IP CCTV systems so as to make such a break in harder for the police to investigate."
We have identified that data is the commodity underpinning the IoT black market economy, but what products and services will be traded by the black hats? According to Rob McFarlane, director of Head Labs, ‘Products and services will exist on both the hardware and software side of the equation with devices becoming available which alters data or steals information.’
The goal of using and controlling firmware will also motivate the use of IoT ransomware, leading to an increase in trust-based attacks using digital keys and certificates. This again is of real threat to both the enterprise and consumer, as the control of your data will be out of your hands. The question is, will you pay up for that data?
Explaining IoT ransomware, Kevin Bocek, VP Security Strategy and Threat Intelligence at Venafi, said: "From a single point of compromise – the digital certificate – hackers and cybercriminals can take over a whole network of hundreds, thousands or even millions of smart ‘things’. This can then be used to blackmail companies – cease operations, take on huge disruption, or pay up."
The words ‘hacker’, ‘black hats’ and ‘cybercriminals’ have occurred throughout this article, but who are these faceless criminals benefitting from this illegal activity? Sure, the obvious stereotypical hacker – the lone mid-level, hooded perpetrator working out of a basement – will of course benefit from this black market, especially in the trade of stolen financial data.
Cyber gangs and state-sponsored hackers may also seize upon the opportunity that silent data manipulation may afford.
Controversially, however, it is the seemingly legitimate companies which may take full advantage of what is offer on the black market. As Rob McFarlane, director of Head labs, told CBR:
"I don’t think the type of illegal activity we’re talking about is limited to evil tech gangs bent on skimming your bank accounts or hijacking your digital wallet at Starbucks. We should be more worried about outwardly legitimate seeming enterprises that need to fake data in order to pass regulation, make a sale or manipulate customer activity to pad their numbers."
This opinion is shared by Manfred Kube, head of M2M segment at Gemalto, who agreed that businesses could use the black market to manipulate numbers to the advantage of their business. He told CBR:
"There are multiple examples of where people or companies could benefit from the black market, such as taxi drivers being able to manipulate their meters to show more miles or tachographs being changed to indicate a lorry has driven less miles. There could also be scenarios where fraudsters sell devices on the black market to manipulate power consumption readings so consumers get charged less."
The IoT black market is of huge concern to both businesses and consumers, but the impact of this economy on the IoT market in general must not be overlooked. The existence of an IoT black market will undermine trust in products and devices, as Gemalto’s Kube told CBR:
"When buying an IoT device from a reputable retailer or supplier there is an implied trust from the consumer that they will able to use the device and know that their data will not be compromised or put in any danger. With the black market this trust is eliminated as anything bought or sold here cannot be guaranteed to be 100 per cent secure or reliable, which in turn can cause compromised systems and loss of data."
As the race to secure IoT devices and data accelerates, the adoption of IoT in the mainstream is also put at risk.
"More time and money will need to be spent on encryption and authentication security which may result in a slowdown of IoT rollout." Rob McFarlane told CBR.
However, there is always a silver lining to be found. While data is bartered for on the black market and devices are compromised, security vendors can find opportunity in the IoT underground economy.
Firstly, the black market will highlight security as a focus for IoT designers, increasing security investment and pushing designers towards new methods, designs and innovations.
The IoT black market has yet to really materialise, but the threat of this underground economy is very much real. As cyber warfare continues to evolve, the trick is to for security experts to keep evolving at the same pace as the black hats, and also face the reality that wherever there is sensitive and valuable data, there will be someone trying to access and use it illegally.
This article started by drawing on the physical black markets seen in history – it is worth noting that the black markets of old were restricted in the sense that buyers had to have knowledge of location, or have the right connection, in order to make an illegal purchase. These new black markets, however, require only one thing – an internet browser.
The access is unrestricted, open to everyone. This more than doubles the reach, danger and risk posed by the IoT black market.






