Brexit is now a banned word in my house. The word dominating every headline, every online and offline conversation has left me with a reactionary grimace every time I hear the word. For those of you living off the grid or living under a rock, the UK held a referendum last Thursday 23 to decide if the country would leave or remain as a member of the European Union.
Against all polls and expert opinion, 51.9% of the UK voting public chose Leave, beating the 48.1% who voted to remain. The FTSE plunged, PM David Cameron resigned and opposition leader Jeremy Corbyn faced a party revolt. The Brexit shockwave hit all major markets leaving a number of question marks in its wake.
However, the government failed in more than one respect.
In the build-up to the vote, an IT glitch crashed the Register to Vote website, meaning thousands of voters were unable to complete registration by the midnight deadline on June 7. It was "an IT glitch that should have been anticipated and planned for months ago", according to John Rakowski, Director of Technology Strategy at AppDynamics, and yet, it wasn’t.
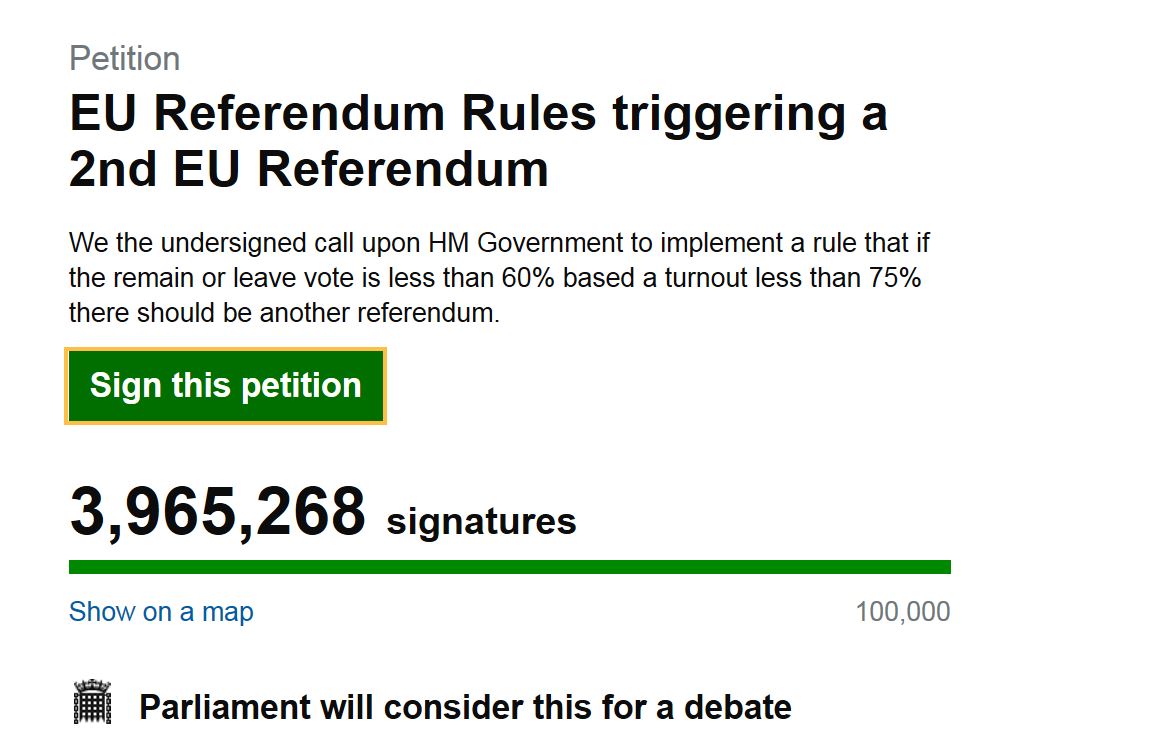
Further IT failings were seen post-referendum, when an online petition calling for a second EU referendum was found to have been hijacked by automated bots adding false signatures. The government’s petitions website seemingly has no system in place in which to detect or deal with bots and, embarrassingly so, there seems to have been thousands of signatures from people in Vatican City and Antarctica. Looking at the use of bots, Rami Essaid, CEO of Distil Networks, told CBR:
"These appear to be fairly simple and automated attacks, so stopping them should be something that can be automated too. However, it’s important that this kind of step gets taken beforehand. Whether it is driven by internet pranksters or by members of the Leave campaign attempting to invalidate the petition doesn’t matter. Sites like this should be hardened against automated attacks carried out by bots.
"While sites like this can often cope with large scale attacks like Denial of Service, bot attacks are often overlooked. Bots are mainly targeted at financial gain through ad fraud or account hijacking, so the website designers may not have thought about protecting against them previously. However, improving security should mean that all potential mis-uses of IT and sites should be considered at the start and prevented."
When responding to a cyber attack or breach in the private sector, brand and reputation are major factors in incident response – and it is no different in the public sector. The customers are UK citizens, who have seen the democratic process threatened by ineffective IT infrastructure and a lack of preparation and planning.
James Mayo, Vice President of Sales and EMEA Public Sector lead at Unisys, told CBR: "Cyber threats go far beyond hacking and data collection and can have a direct detrimental impact on the democracy of a whole nation.
"Cyber security is not just about data protection, it involves protecting the integrity of the democratic process, which governmental institutions should take very seriously. Although the government has assigned specific budget to counteract security breaches, the spend and deployment is simply not taking place fast enough to counteract the tenacity and speed of these hacking incidents."
Mayo highlighted that the hijacking of the petitions website only serves to show the UK public that breaches and cyber attacks occur across governmental institutions as well as private sector organisations – and maybe the public sector should start taking an approach like the private sector, as Peter Duffy, CTO at Sumerian, told CBR:
"You can expect a high-volume of website traffic around the time of a referendum and given the limited resources available to IT managers at public bodies, there is a need to be smart about right-sizing IT infrastructure to deal with peaks and troughs in demand. Adopting a proactive rather than reactive approach to IT service management through predictive analytics and advanced scenario modelling will enable IT managers to calculate and plan the necessary IT to cope with demand and thus avoid potential IT outages.
"Yet despite the obvious benefits of this technology, a survey we recently conducted found that almost 50% of businesses still rely on spreadsheets to perform capacity planning. If Government departments want to reassure citizens they can manage an effective IT operation, while at the same time avoid unnecessary costs across their IT environments, they need to move away from a manual and unstructured approach to IT capacity planning."
Any mention of manual and unstructured approaches to IT always points the finger of blame straight at outdated legacy systems which, as Stephen Morgan, co-founder of Squix argues, is not always the number one cause of IT issues:
"Legacy systems and the siloed nature of government departments (including the IT systems and their supporting teams) often hold back the development and advancement of digital processes. In some cases, it isn’t the outdated systems that cause issues for IT, but the archaic structure of the organisation".
With legacy systems and cyber threats threatening democratic process, it is easy to advise the public sector to upgrade legacy systems, adopt a devops approach and fully embrace what they preach for the digital economy. However, it is integration that is key. Stephen Morgan said:
"To ensure that online services succeed, public sector organisations must go beyond just creating a website, and focus attentions on integrating it with the customer experience as a whole. If a digital strategy is thought of as a website alone, departments will find themselves left with an expensive and unused system that has an increased reliance of analogue systems.
"A good website is only as good as the information and infrastructure that it is built upon. With this in mind, government departments need to examine all customer touch-points holistically to ensure that back-end processes are not disjointed from front-end interfaces."
This call for integration is echoed by Colin Reid, CEO of TotalMobile, who argues that the ‘gaps in government IT go far beyond websites crashing and bots hijacking online petitions." Reid argues that there are fundamental decisions being made in government IT which are negatively impacting people’s lives and costing taxpayers billion. He said:
"For example, one of the biggest issues we all face is the lack of interoperability in government IT systems. The £12bn National Programme for IT in Health tried and failed to ensure that systems interoperate. It’s now five years after that initiative was scrapped and we’re still nowhere near having systems that talk to each other. This seems crazy as it’s something which is well advanced in the private sector, you only have to look at Slack or Xero to see people benefiting from third party integrations.
"The government needs to facilitate integration between systems by telling suppliers to actually do what they’ve signed up for, as without this, I fear the technological abilities of the NHS will not advance as quickly as we need it to. It’s just another gap which is derailing government IT."
The pre-referendum website crash and post-referendum bot attack serves to highlight to the average UK citizen that the government is not infallible when it comes to IT – just like private companies it faces cyber attacks and moments where traffic surges and the network can’t cope. The citizen, the consumer, demands more from government IT services and legacy systems, archaic organisational structure and a lack of integration means that the public sector is failing to deliver.
Although IT may be pretty low on the interest scale in the wake of Brexit, for a government looking to champion a digital economy a transformation of services and delivery must be taken. Until that transformation happens, well, thank goodness the actual vote was done with paper and pencil.






