California-based cybersecurity company Fortinet has added an IoT security toolkit to its portfolio, this week releasing a network access controller called FortiNAC.
FortiNAC allows IT and OT teams to document all the connected devices in their IoT network and gives them the ability to shut down, segment and isolate sections of that network.
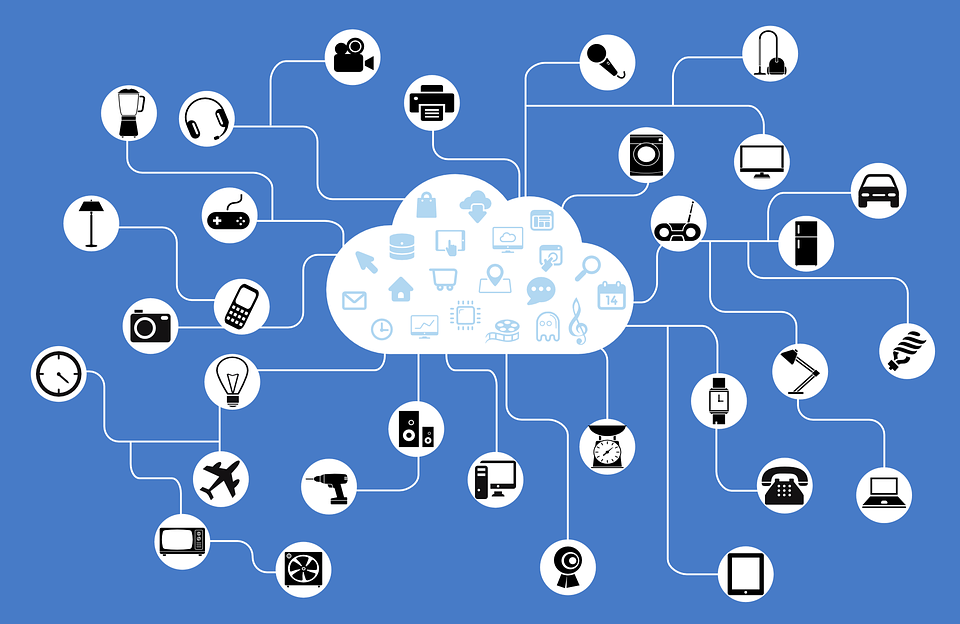
Enterprises across a range of industry verticals are increasingly taking advantage of the big data generated by IoT devices.
Yet devices from a range of vendors pose an increased threat vector with, as Computer Business Review recently reported, patching often slow and IT/OT teams already overrun with security hygiene issues.
See Also: New Mirai Botnet Uses Unsecured IoT Devices to Carry out DDoS Attacks
Fortinet Network Access Controller
FortiNAC works by automatically collecting information regarding any connected devices you have in your network. These are then matched to a library containing profiles for all your devices; it is then given a policy to follow.
Peter Newton Senior Director of Product Marketing at Fortinet wrote in a blog that: “This way, it ensures that all connected devices, anywhere in the distributed network, are not only authenticated, but also subject to context-driven policies that define who, what, when, where, and how connectivity is permitted.”
See also: Bug Hunters Double SCADA Vulnerability Finds
“These rules are then distributed across the network to make sure these devices can only access those applications, infrastructure segments, and assets they have been authorized to touch,” he noted.
The network access controller then has the ability to specify IoT devices to certain networks which can then be segmented as needs be.
FortiNAC works in tandem with Fortinet’s Security Fabric which covers an array of cyber security concerns including an issue alerting systems.
If the Security Fabric identifies a device with suspiciously odd behaviour, such as a smart lightbulb seeking data from a network, then FortiNAC can check that device and if suspicions are confirmed, then isolates it and its surrounding linked devices from the main network while the issue is resolved.
“The Security Fabric automatically correlates threat intelligence to identify other devices that may have also been compromised and then dynamically leverages FortiNAC to isolate those devices as well,” Peter Newton states.
Zeus Kerravala from ZK Research commented in an emailed statement that: “The network access control (NAC) market is seeing double digit growth in revenue, which is being driven by the need for device visibility in the network and concerns over IoT security.”






