Cybersecurity was already on the board agenda among UK public sector organisations before Covid-19.
Chris Naylor, outgoing chief executive at the London Borough of Barking and Dagenham, assesses risks on two dimensions: their likelihood and their potential impact during a panel on cybersecurity at New Statesman and Tech Monitor‘s recent Public Sector Technology Symposium. In the past five years, cybersecurity risk has climbed both rankings, Naylor explained. “It’s got a lot more of my attention as a result.”
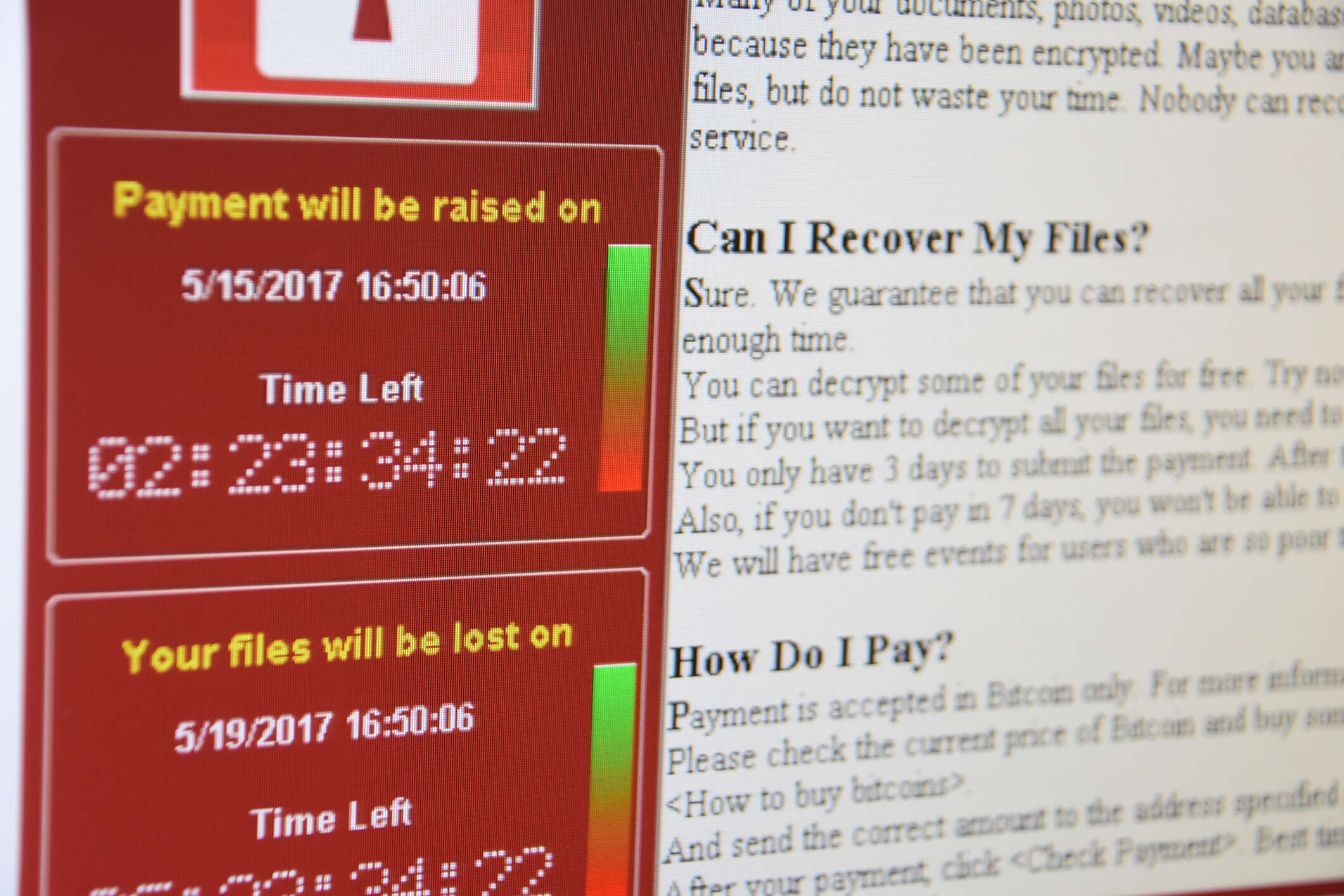
But the pandemic and the accompanying bout of ransomware put the UK public sector’s readiness to the test. That readiness has proved to be a “mixed bag,” said Jonathan Lee, UK director of public sector relations at panel sponsor Sophos. Collaboration between government and the cybersecurity industry helped public sector organisations improve their preventative stance against threats, Lee said, but “I think we can do better”.
Cybersecurity in the public sector: information overload
Adrian Boylan, head of IT, Moorfields Eye Hospital NHS Foundation Trust shared that, while awareness of cybersecurity issues has improved significantly in recent years in the public sector, many smaller organisations do not have the resources to tackle all the threats they face. And while there is a wealth of advice and information available from government bodies and suppliers, it can be overwhelming, he added.
Similarly, Boylan said, compliance with cybersecurity guidelines and frameworks can be overwhelming for smaller organisations, especially when added to the practical work of securing and monitoring IT systems. “Perhaps we should move away from the more resource-intensive, annual exercise of asserting that we meet theoretical guidelines or points of principle back towards a practical assessment [of cybersecurity],” he said.
Responding to cybersecurity threats
If it wasn’t already obvious, the ongoing ransomware outbreak has made it inescapably clear that cybersecurity threats have changed significantly in the past decade. Defences need to evolve as well, said Lee.
The human dimensions of cybersecurity are vital, not just in preventing breaches but also in detecting and responding to them too, explained Shelton Newsham, divisional information security officer at UK Health Security Agency and a former police officer specialising in cybercrime. When it comes to the technical teams handling IT security, a range of perspectives and experience is vital. “Having someone who is technically aware but not technical is really, really important,” he explained. “They will spot things that the people with the real technical ability who are immersed in trying to contain an incident [may not].” These ‘technically aware’ staff can often help police attribute attacks and, in some cases, identity the attackers.
Non-IT staff, meanwhile, also play an equally vital role in incident response, Newsham explained.
Bad news to share? Build up your trust bank
How should public sector IT leaders communicate security risks to senior management? Naylor shared his approach to maintaining awareness of ongoing risks: a monthly assurance board meeting, in which the heads of strategic departments, including cybersecurity, raise risks that need to be addressed. “In essence, I’m leaving the burden of judgment with them to tell me what they think I need to know,” he said. Crucially, though, he asks that departmental heads don’t just describe the risk but identify a call to action. “I need to know the consequence of what I’m hearing,” he says. “It’s not good enough for people to go, ‘Well, this thing happened’. What I really want to want to know is, what do you want me to do about it?”
This meeting can provoke some difficult conversations. During a secondment to Birmingham City Council, Naylor was asked for £20m to address cybersecurity issues. “Sometimes I don’t want to hear it,” he said. But “we have to hear it and we have to create spaces in which to hear it.”
And when an IT leader has to raise a cybersecurity issue that requires an immediate and extensive response, it helps to have built up trust within the organisation. “Get trust in your trust bank so that when you need to pull the lever, they’re ready to hear you,” Naylor advises. “If you’re running a tight ship inside your IT department, [it] builds the confidence of people like me so that when you come to us with a request for additional funding or resources or action, we are in the headspace to respond to that.”
Homepage image by tzahiV / iStock






