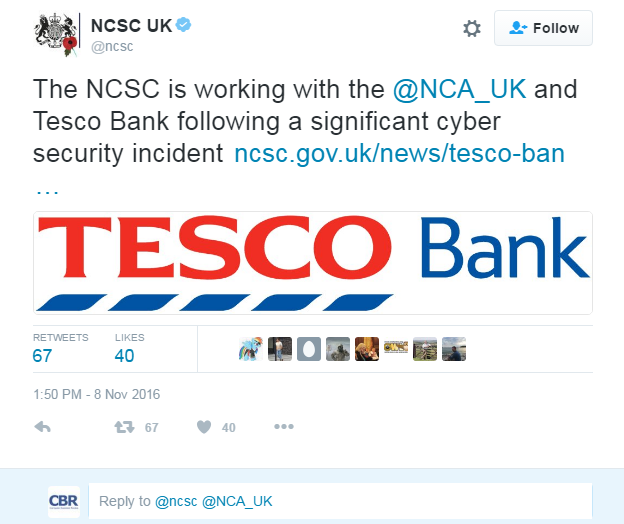
Following the breach at Tesco Bank which saw at least £2.5m stolen and which is under investigation by the National Cyber Security Centre CBR asked forensics experts from Nuix what happened and what happens next.
CBR: Where would you start if you were investigating the Tesco breach?
Paul Slater, Global Head of Investigations, Nuix: Data breach investigations are just like any other investigation I have done in my career, whether it be investigating child exploitation rings or investigating financial crime – the main difference is that you are looking at potentially different sources of evidence.
The challenging thing with breach investigations is ticking time – where a typical investigation wants to find out everything about what happened, where, how, who did it and why. However, it is a balancing act as for an enterprise, especially a retail bank, the focus is on finding out what was compromised and limiting and containing the breach as quickly as possible to reduce the public-facing impact – and returning to ‘business as usual’.
I would start by getting the right people in the room – key stakeholders from across the business, IT, security, finance, press office etc. Then – with my investigations team – I would start to map out what we know – the evidence landscape. Most organisations don’t know what they have in terms of potential evidence sources or where it is.

Read: Tesco Bank Hack: 20 Key facts about the Bank and its IT systems
CBR: The emphasis is always on discovery, response, mitigation – will investigation, arrest, prosecution ever follow?
Paul Slater: The investigation, arrest & prosecution are law enforcement responsibilities. Businesses can help them by having an incident response plan in place that takes into account the forensic readiness of your business. Simple things like ensuring that server clocks across your business are in sync and that all relevant logging is switched on. Simple measures such as this make investigating, and ultimately finding crucial bits of evidence and trails for arrest and prosecution.
Stuart Clarke, Nuix’s CTO – Cybersecurity: In recent years we have seen a number of arrests associated with data breaches and I expect this to continue as investigations successfully identify the perpetrator/s. Investigating a data breach is incredibly important not just to understand how the breach happened, but also to learn and build intelligence repositories, which will subsequently help improve our security posture in future.
Read: Tesco Bank Hack: 6 vital questions that need answers
CBR: There are questions being raised because ‘cash’ was taken from individual accounts – has this happened before at this scale? Does this single this breach out as unique?
Stuart Clarke, Nuix’s CTO – Cybersecurity: Facts are limited but the activity suggests this is a sophisticated attack, however it is far too early to say. To say this breach is unique is not important at this time. This is yet another data breach where the sensitive information of customers has been threatened. Securing sensitive information including PII (Personally Identifiable Information), PHI (Protected Health Information) and PCI (Payment Card Information) data must be a top responsibility and priority of those who process and control this data.
Paul Slater as its Global Head of Investigations at Nuix. Slater will be at the head of Nuix’s activities around law enforcement and policing, government, and enterprise investigations. He will further contribute to the development of Nuix Investigation & Response and its integration with Elasticsearch as a database back end.
Paul Slater’s previous role at Nuix waS Executive Director of EMEA and Director of Forensic Solutions. Before joining the company in 2013, Slater worked for more than 20 years as a police officer and consultant in investigations, digital forensics and eDiscovery, including as interim head of the digital forensics unit in the UK Serious Fraud Office.






