Researchers at Russia’s Kaspersky Lab say they have discovered a new ransomware strain dubbed “Sodin” that exploits a Windows vulnerability (CVE-2018-8453) they reported to Microsoft in August last year, demonstrating an array of unusual techniques.
Sodin exploits elevated privileges in an infected system via win32k.sys and takes advantage of the architecture of the Central Processing Unit (CPU) to avoid detection – functionality not often seen in ransomware, among other idiosyncracies detailed by Kaspersky today.
The Sodin ransomware does not require victims to click a phishing link.
Its developers/users instead usually find a vulnerable server and send a command to download a malicious file called “radm.exe” Kaspersky said. (The Windows vulnerability was patched on October 10, 2018. The ransomware is another reminder to those not patching systems that whatever challenges it throws up, it really ought to be a priority…)
Making it harder than usual to detect is its use of the “Heaven’s Gate” technique that lets it execute 64-bit code from a 32-bit running process.

It also uses a hybrid scheme to encrypt victim files. (The file contents are encrypted with the Salsa20 symmetric stream algorithm, and the keys for it with an elliptic curve asymmetric algorithm.)
Sodin Ransomware Part of a RaaS Scheme
Kaspersky said the malware appears to be part of a RAAS – ransomware-as-a-service – scheme.
“Curiously [the] private session key is also encrypted with another public key hardcoded into the body of the Trojan, regardless of the configuration”, Kaspersky Lab’s Orkhan Mamedov, Artur Pakulov, Fedor Sinitsyn wrote today.
“We will call it the public skeleton key. The encryption result is stored in the registry under the name 0_key. It turns out that someone who knows the private key corresponding to the public skeleton key is able to decrypt the victim’s files, even without the private key for sub_key. It seems like the Trojan developers built a loophole into the algorithm allowing them to decrypt files behind the distributors’ back.”
See also: Resurgent Ransomware Attacks Take Out Latest European Victim
A company spokesman explained: “There are signs that the malware is being distributed through an affiliate program. For example, the developers of the malware have left a loophole in the malware functionality that allows them to decrypt files without their affiliates knowing: a ‘master key’ that doesn’t require a distributor’s key for decryption (normally the distributor keys are the ones used to decrypt the files of victims that payed the ransom).”
The added: “This feature might be used by the developers to control the decryption of victim data or the distribution of the ransomware by, for example, cutting certain distributors out of the affiliate program by making the malware useless.”
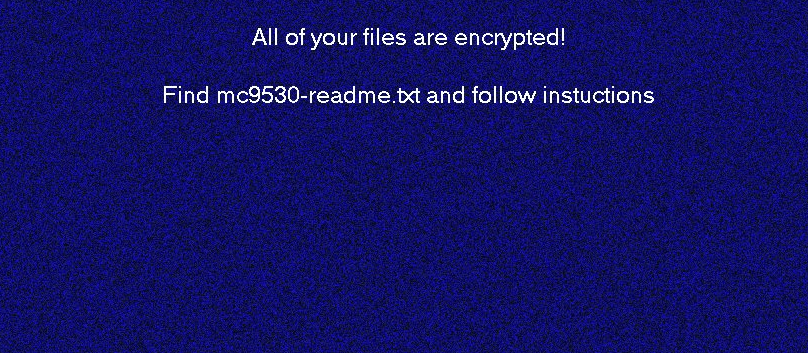
Most targets of Sodin ransomware were found in the Asian region: particularly Taiwan, Hong Kong and South Korea. However, attacks have also been observed in Europe, North America and Latin America. The ransomware note left on infected PCs demands $2500 (USD) worth of Bitcoin from each victim.
The researchers believe that the Heaven’s Gate technique is used in Sodin to bypass emulation-based detection. Emulation-based network intrusion detection systems aim to detect the presence of shellcode in network traffic by temporarily creating objects that the sample interacts with then analysing that interaction, a little like a very lightweight sandbox.






