
Android banking trojan malware SharkBot has found its way back onto the Google Play Store hidden within antivirus and cleaner-type apps, according to a new report by cybersecurity company NCC Group’s Fox-IT. The newly discovered versions are also better at avoiding detection during the app review process.
The original SharkBot appearance was discovered in October last year by researchers at Cleafy Threat Intelligence, who say it appears to be a new generation of Android banking malware. Its goal is to initiate money transfers from compromised devices via automatic transfer systems through keylogging, overlay attacks and SMS intercepts.
When it first reappeared in February this year, Fox-IT found a basic version of the malware code attached to a fake antivirus app that made use of a “Direct Reply” feature in Android that allowed the malware to automatically reply to incoming notifications on the infected device and use that to install further software, in this case, a more advanced version of SharkBot.
To access banking services the original version relied on accessibility permissions and services being enabled within the Android device. This allowed the malware to intercept all the accessibility events including button presses, TextField changes and any touches on the screen.
The latest version, also spotted by Fox-IT researchers, doesn’t require the accessibility features to function. It asks the victim to install the malware as a fake update for the antivirus software they have already installed and this has been found actively spreading in two apps on the Play Store.
Already on tens of thousands of devices
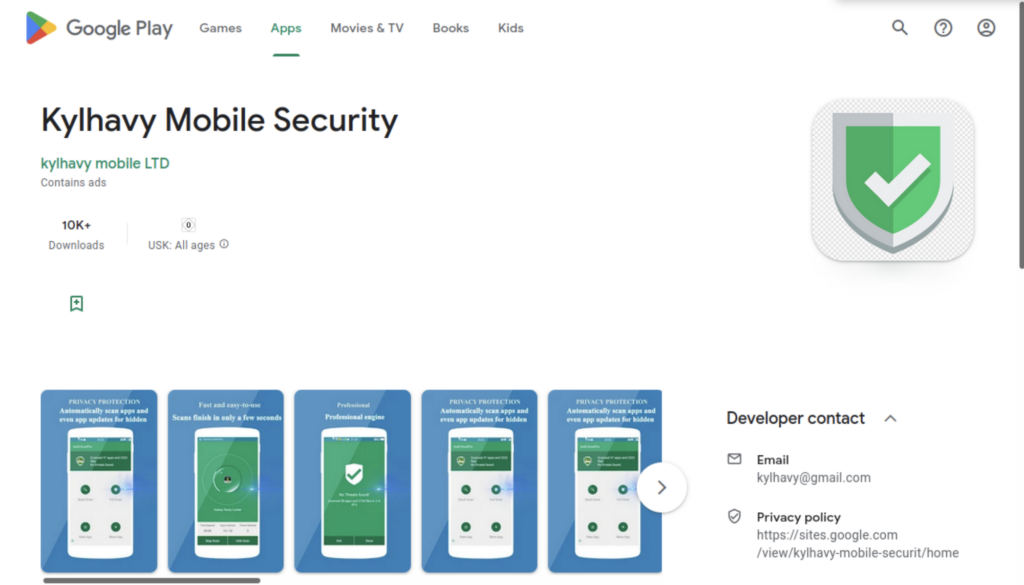
The two apps featuring the malicious code are Mister Phone Cleaner, which has more than 50,000 downloads so far, and Kylhavy Mobile Security which has been downloaded more than 10,000 times.
Known as droppers, these apps have been designed to target users in the US, Spain, Australia, Poland, Germany and Austria and once installed they drop the latest version of SharkBot on the device. This includes an updated command-and-control communication (C2) mechanism, a domain generation algorithm and a fully refactored codebase not present in the original SharkBot.
Fox-IT researchers wrote in a blog post on the new discovery that this version of the dropper makes a request to the C2 server to directly receive the APK file of SharkBot, explaining that “it won’t receive a download link alongside the steps to install the malware using the ‘Automatic Transfer Systems’ (ATS) features, which it normally did,” as this presented too many red flags for reviewers and increased the likelihood of the app being rejected.
“In order to complete the installation on the infected device, the dropper will ask the user to install this APK as an update for the fake antivirus. Which results in the malware starting an Android Intent to install the fake update,” the researchers said.
The dropper then installs the payload in a non-automatic way, making it more difficult to get installed as it requires the user to trust the update, but also more difficult to detect during the review process for the dropper app being published in the Play Store as it doesn’t need accessibility permissions which might raise alarms.
“Besides this, the dropper has also removed the ‘Direct Reply’ feature, used to automatically reply to the received notifications on the infected device. This is another feature which needs suspicious permissions, and which once removed makes it more difficult to detect,” the team wrote. “To make detection of the dropper by Google’s review team even harder, the malware contains a basic configuration hard coded and encrypted using RC4.”
These updates are to get around the new sideloading restrictions introduced in Android 13 earlier this year that make it harder for malware to abuse the accessibility APIs.
Read more: Has Emotet take-down killed the notorious botnet for good?
Homepage shark image by solarseven/iStock






