Sellafield nuclear site has denied claims it has been the victim of cyberattacks by hackers linked to Russia and China, who reportedly left malware in its networks undiscovered for years. The site has been criticised by a nuclear industry regulator for shortcomings in its cybersecurity measures and could face further action.

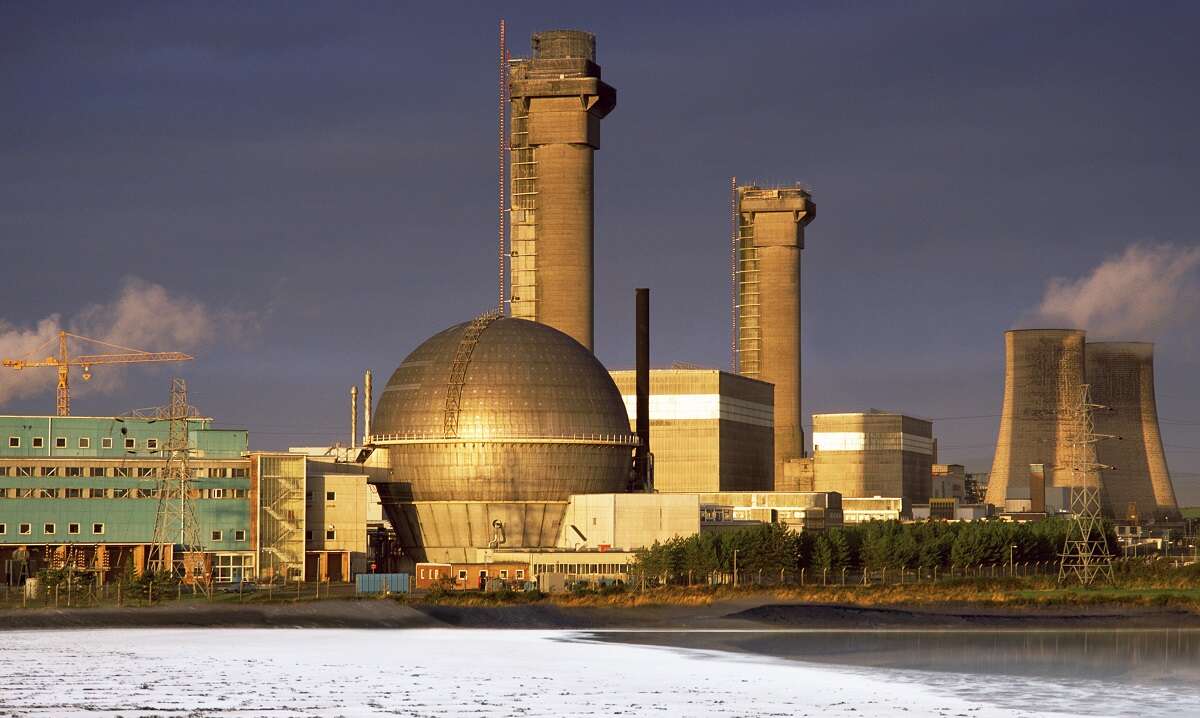
Formerly a nuclear power station, the 650-acre Sellafield site in Cumbria is now used for nuclear waste processing and decommissioning. According to an investigation from the Guardian, security breaches have been detected in its networks dating back to 2015.
Sellafield nuclear site’s cybersecurity deficiencies
Malware was first detected on Sellafield’s network as far back as 2015, according to the Guardian investigation dubbed ‘Nuclear Leaks’. It is thought to have been planted by hackers with links to Russia and China, according to a source quoted by the newspaper.
It is alleged that Sellafield, which employs 11,000 staff, failed to disclose the breaches for several years, and that the problem only came to light when staff at a third party discovered they were able to access Sellafield’s network from external machines, and called in the Office for Nuclear Regulation (ONR). It has since been investigated by the industry regulator, which has found shortcomings in the site’s cybersecurity provisions and may launch prosecutions, the Guardian claims.
An ONR spokesperson said Sellafield was failing to meet cybersecurity standards, and said: “Some specific matters are subject to ongoing investigations, so we are unable to comment further at this time.” The organisation’s most recent annual report said that “improvements are required” by Sellafield when it comes to cybersecurity.
A Sellafield spokesperson said: “We have no records or evidence to suggest that Sellafield Ltd networks have been successfully attacked by state actors in the way described by the Guardian.
“Our monitoring systems are robust and we have a high degree of confidence that no such malware exists on our system.” The spokesperson added that the company takes “cyber security extremely seriously” and that all its systems and servers have “multiple layers of protection”.
Critical infrastructure under attack
Critical infrastructure sites like Sellafield are attractive targets for nation-state-backed hackers, and the UK and its allies in the Five Eyes security alliance have issued repeated warnings in recent years that providers of power and communications infrastructure could be subject to attacks.
Last month, the UK’s National Cybersecurity Centre (NCSC) warned in its annual report that critical infrastructure sites need better cybersecurity, but that the situation is improving. The government has said it will set cybersecurity targets for infrastructure providers to ensure their defences are up to scratch.
Jamie Ahktar, CEO and co-founder at security vendor CyberSmart, said: “It almost goes without saying, but the details of this breach are very concerning. Not only does the potential identification of ‘sleeper’ malware illustrate the sophistication of state-sponsored attacks but if the breach has lain undetected since 2015 it poses serious questions about Sellafield’s cyber defences.
“Given that the site has faced several problems with its cybersecurity over the years, we hope this incident serves as a reminder, not just to Sellafield, but to all parts of the UK’s critical infrastructure and the small businesses that work in tandem with it to take cybersecurity seriously.”






