1. Robots Take Over
An apt point to kick off with, seeing as CES 2016 has been over-run with smart, intelligent, autonomous devices, cars and appliances. Even fridges are today being developed with in-built intelligence. The threat of the robot is not just seen in the consumer world, with IBM’s cognitive system, Watson, enabling a new partnership between people and computers.
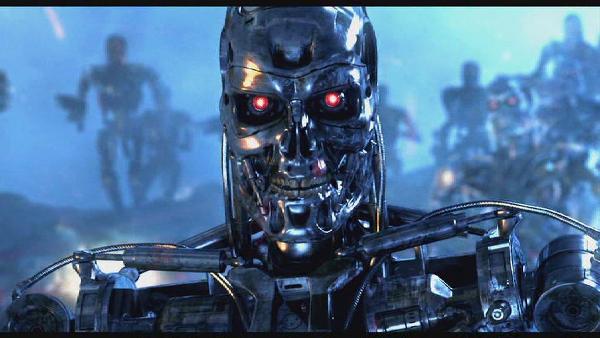
Many a Hollywood movie has illustrated the threat of robots taking over – but how likely is a terminator-esque judgement day in 2016? For Catalin Cosoi, Chief Security Strategist at Bitdefender, it is not a subject to take lightly.
"A singularity that will consider humans as deprecated. I’m not kidding, artificial intelligence could be more evolved than we know. Worst case scenario, A.I. goes terribly wrong and is misused against humans as a form of social control and conformity."
2. Safe Harbour Delay
Last year the European Court of Justice declared the European Commission’s trans-Atlantic data protection agreement invalid. Although EU privacy law bans the movement of citizen data outside of the EU, the EC and US agreed a deal in 2000 whereby EU citizens’ data could be transferred by American companies to the US.
Since being declared invalid, due in part to data protection issues post-Snowden, the EC and the US have been negotiating on a new framework for the transfer of personal data. Nothing yet has been set in stone, and this ongoing delay is something that Michael Hack, SVP of EMEA Operations at Ipswitch, believes could be one of the worst things to happen in 2016.
"The worst thing that could happen in technology this year is that the EU council and regulators continue to stall in issuing guidance around Safe Harbour and how it fits into draft new data protection regulation – the GDPR. Businesses are calling out for more information on data handling, security and privacy.
"Since the CJEU rejected the Safe Harbour rules back in October, there has been no official advice or guidance on what this means for business. The implications of the ruling could render many global companies in a tough spot, specifically companies that rely on the free transfer of data between the EU and US."
3. IPv6 Ignored
Internet Protocol version 6 is the most recent version of the Internet Protocol, or IP. This is a communications protocol that provides location and identification for computers. Predecessor IPv4, which still routes most traffic today, had a capacity of approximately 4.3 billion addresses, a number which finally suffered exhaustion on 3 February 2011.
Promising larger address space, simplified processing and route aggregation across the Internet, the IPv6 has been deployed but, argues Nathalie Künneke-Trenaman, IPv6 Program Manager at the RIPE NCC, not enough companies are making the transition from IPv4 – an issue which could prove to be a big problem in 2016.
"The biggest mistake of 2016 would be for industries to ignore the need to deploy IPv4’s successor, IPv6, which already has 10% adoption globally. There are supposed workarounds which operate by sharing one IP address with many people, but that means if anything goes wrong, even more people are affected.
"The Internet is built on principles of end-to-end connectivity, and we run the risk of stifling technological innovation by limiting how devices can connect to each other. Now is the time for IPv6."
4. IoT Incompatibility
The IoT is growing at a tremendous rate, with numerous devices spanning from automobiles to home appliances. However, the industry has been vocal in its criticism of the lack of standards – an issue which is stifling innovation and halting any further adoption. The Internet of Things could do so much in a number of industries and truly transform daily lives, but, as Gordon Haff, cloud evangelist at Red Hat, told CBR, the industry is holding itself back through a lack of standards.
"The Internet-of-Things (IoT) has enormous potential to use data from pervasive sensors to save energy, improve health, and generally provide an interface between the digital and the physical worlds but a plethora of incompatible communications standards could continue to be the norm. Wi-Fi (including the recently announced HaLow), ZigBee, NFC, Bluetooth (including an LE variant)… The list goes on.
"Sure, different standards are needed for different purposes. There are legitimate tradeoffs, especially around battery life in particular. But sometimes one gets a sense that the industry isn’t even trying to be interoperable."
5. Blockchain Rush
2015 saw companies scramble to research and adopt blockchain technologies. Financial institutions such as Barclays, Nasdaq and UBS brought blockchain on board, while technology companies such as IBM and Samsung also looked in to how blockchain could be used to boost business.
Blockchain is a permission-less distributed database based on the well-known Bitcoin protocol. It maintains an ongoing growing list of transaction resistant to tampering.
Although currency is the best known use case of blockchain, other applications in areas such as healthcare, are also possibilities. The main danger for 2016, as Rob Woods, co-founder and managing director at the Certificate in Finance and Technology told CBR, is that there is a potential for companies to rush blockchain projects which could lead to a negative impact on business.
"Blockchain itself is not a negative thing – it represents innovation and progress. But it’s also seen a huge amount of hype in 2015, which has fuelled an adoption race – and this is exactly the sort of scenario that can lead to problems. Clearly it’s important to innovate, but while the early bird may get the worm, it’s the second mouse that gets the cheese and there are definitely traps to be avoided when trying to capture blockchain cheddar. A reckless dash to get ahead can mean corners are cut, overly ambitious timelines for projects are overrun and errors introduced.
"Blockchain is here to stay, but it’s important that due care and attention is taken when adopting it. A well-considered strategy and a team of technologists that know exactly what they are doing and where it fits into the wider picture may be the difference between being caught in a trap and a wonderful feast.
6. Snooper’s Charter Gets The Green Light
Debate around the UK government’s Investigatory Powers Bill was fierce in 2015, but the real trouble could start in 2016. Seeking backdoors into encryption under the guise of national security, security experts are unanimous in their argument that any weakening of encryption will give hackers an access-all-areas pass into people’s communications.
With the privacy of every UK person on the line, Greg Aligiannis, Senior Director of Security at Echoworx, believes that the worst thing to happen is for this law to pass.
"We’ve seen the emergence of data privacy become a much wider talking point in the UK with the introduction of the Investigatory Powers Bill. If the UK government gets it own way, this will be undoubtedly be one of the worst developments to happen this year. Cyber-surveillance is no different than old school wire-tapping.
"However, the government requires court approval for a wiretap and only after they demonstrate evidence of reasonable suspicion. It should not be allowed to circumvent existing laws based on the type of media being surveilled. These laws were put in place to protect the average law abiding citizen from this kind intrusion. The same rules should apply regardless of whether its phone conversations or web and social media use being tapped."






