
Robert Hannigan, the former director of GCHQ and now executive chairman of security firm BlueVoyant International, has long held a close interest in the security of critical national infrastructure (CNI). Having overseen the creation of the UK’s National Cyber Security Centre, his views have been informed by a bird’s eye view of threats to not just CNI, but UK Plc more broadly.
Now, as the co-author of a new industry “Foresight Report” on cybersecurity for Industrial IoT (IIoT) – alongside colleagues at global safety charity Lloyd’s Register Foundation and the University of Oxford – he has been taking a close look at the technology that is set to prove integral to so much future energy, transport, built environment, and manufacturing infrastructure.
Hannigan, like his co-authors is concerned by much of what he sees.
New security threats to IIoT environments are emerging rapidly, while current approaches to security do not scale, or have not been robustly tested in the OT space.
Organisational mindset, regulation and insurance approaches that can build preventative security practices are urgently needed, the report suggests, pointing to the widespread abuse of poorly secured credentials, breakdown of risk control dependencies, supply chain risk and more. And regulators, Hannigan thinks, are not doing enough…
He joined Computer Business Review (CBR) to discuss the report.

Was there anything that you found in writing and researching this report that stood out as particularly surprising or worrying?
One of the worrying things was that the enthusiasts for the adoption of IoT in the industrial space — some of those who are most far advanced, including healthcare — are not necessarily the ones who worry most about security.
There is a lack of correlation between adoption and security best practice. That’s setting us up for some difficulty.
Has the high-profile nature of ransomware attacks, for example, not focussed minds in the OT/industrial space?
Companies continue to be really worried about business interruption, particularly in manufacturing.
The engineering and operational mindset is ‘let’s keep this going at all costs’ because the pressures to do so, commercially and otherwise are the key driver. And that doesn’t necessarily make for good security.
On the other hand, you can’t just stop everything. Trying to engineer security in-flight remains a real challenge.
Is it time for regulators to step in more robustly?
I think there will need to be greater regulation.
The sort of ‘best practice’ and ‘hoping for the best’ and ‘kitemarks’ approaches aren’t really working, because they’re not changing the market.
In the market, there’s not enough incentive to spend more money on products that have greater security built in, if you can just do it on lowest cost and churn out millions of devices with virtually no security. The market isn’t correcting.
And I think the only way to do that really is a mixture of regulation and insurance.
We saw in the Solarium Commission report in the US — a cross-party report on what to do about cyber at a high level for the US to improve its defences — a recommendation which I thought was very interesting: liability for manufacturers and software producers for these [IIoT] devices.
There’s a delicate balancing act here: you can’t make Apple and Microsoft liable for flaws in the next OS, or you’ll never get one. Software has flaws.
But there has to be a point at which manufacturers take responsibility.
How does your time at GCHQ inform your views on this?
I think one of the big lessons we learned was government can’t do everything.
The reason we created the NCSC was because of this huge demand for GCHQ to go and do everything. And this just wasn’t realistic. So you had to be quite clear about what were the limits [to government intervention].
Bringing together expertise, which government does have, with private sector resources and skills, to magnify both, was another thing.
One of the highlights in this report, incidentally, is just the shortage of skills generally in cyber security, particularly in the industrial and OT space. That’s going to be a particular problem when the IIoT really kicks in more.
Where are boards/business leaders in this?
Things have improved. Fifteen years ago it was very hard to get anybody interested in cyber security. But governance, I think, is a big problem: who’s responsible for what, particularly in the complicated OT space.
That’s a big problem. It goes right to the heart of how companies are organized and how their boards work. But I think it’s changing.
It was very interesting to see with the Marriott case, the ICO basically saying you “failed to do cyber due diligence” without actually saying what that is. I guess that’s a regulator’s prerogative [laughs].
See also: Bank of England Taps New Tool to Track ROI of Software QA
The biggest complaint I get from boards is “how do I know what expenditure will reduce the risk?”
They’re very familiar with reducing risk in health & safety or finance; they’ve got very comfortable about knowing what the risk thresholds are, and what they can do to reduce those thresholds while never eliminating it — because you can’t. [But they still lack clarity on how to do that in security].
“The supply chain is vast — and they very often looking at the wrong priorities…”
They’re [also] quickly realising that the supply chain is vast and represents a whole new world of risk.
So typically in BlueVoyant, we see companies who may have 10,000 suppliers, and they can realistically look at a tiny percentage of those actively, with pen tests etc. The rest, they will tend to use questionnaires.
And that’s inevitably never going to be very effective for the obvious reasons.
But I think also they’re very often looking at the wrong priorities.
In what sense?
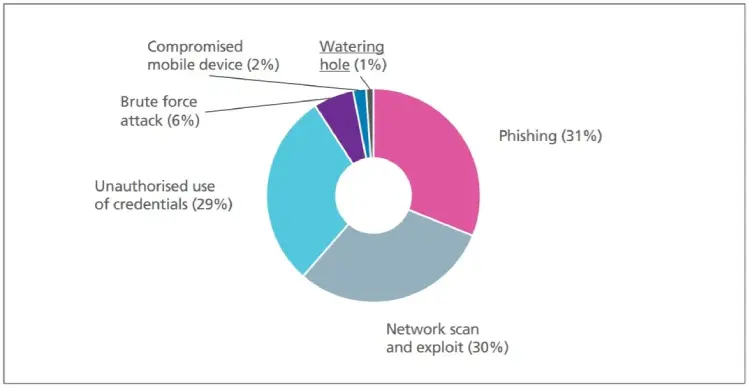
If you look at the incidents of the last few years in the utility sector, most attacks now seem to be delivered through the supply chain.
Some of the nation state ones have been delivered through really quite small suppliers; lawyers, for example, who have a deep connection into the business, are trusted, but whose security is probably not where it should be. So trying to quantify that risk and prioritise it, I think is absolutely key.
The risk might not be with your Top 10 biggest suppliers…
Looking at this report’s risks and mitigation section, there’s a lot of “doesn’t scale”. Talk us through that.
Patching’s not scaling now even in the IT space.
Some businesses still aren’t even taking clearly risk-based approaches. If you try to apply patching practices to the OT space, well… first of all, a lot of OT devices and networks are not really patchable: you can’t apply the same sorts of upgrades to them that you would expect you in the IT space. We have to find a smarter way of monitoring them than simply saying, well, ‘we’re going to expect you to upgrade it’.
What do you think the balance to strike here is between businesses that want to innovate, want to introduce more automation and establishing the risk of doing that?
There are things that can be done, of course.
An absolutely essential thing is separating that management plane from the operational space.
So many attacks are delivered by the same engineer using the laptop for management/internet-connected work and to control the operational spaces work.
That is classically how attackers — particular hostile nation states — get in. So it’s obviously a very good idea to exercise discipline.
[But] I think the commercial drivers to be connected are ever-stronger.Take an example like aviation. Aircraft engine manufacturers are increasingly not making money by selling the engines. They make their money by servitisation, using better telemetry and connectivity.
So all the drivers for the future are going to be about connectivity. That’s how we’ll get greater efficiency, greater environmental benefits. The world in which you can pretend that IT and OT networks will never be joined is not the real world, for better or worse. Cutting yourself off is going to be possible for anyone but a tiny number of very small businesses.
But you will really need to have an iron discipline [to be secure].
Read the Foresight Report here.






