Tech leaders should act now to protect their organisations from the growing threat of quantum decryption, says a new report. Concerns that threat actors may soon start deploying quantum technologies to gain access to crucial information were amplified last week when the US government added eight Chinese quantum companies to its banned list, citing their close links with the government in Beijing and the threat this poses to other countries.
The businesses were among 27 added to the so-called “entity list” last week. This prevents named companies from doing business in the US and accessing its technologies. The eight have been added to this list specifically to limit China’s quantum abilities, with concerns raised over quantum advancement of military capabilities and the idea that sensitive encrypted data and virtually signed documents could be stolen and decrypted using quantum systems.
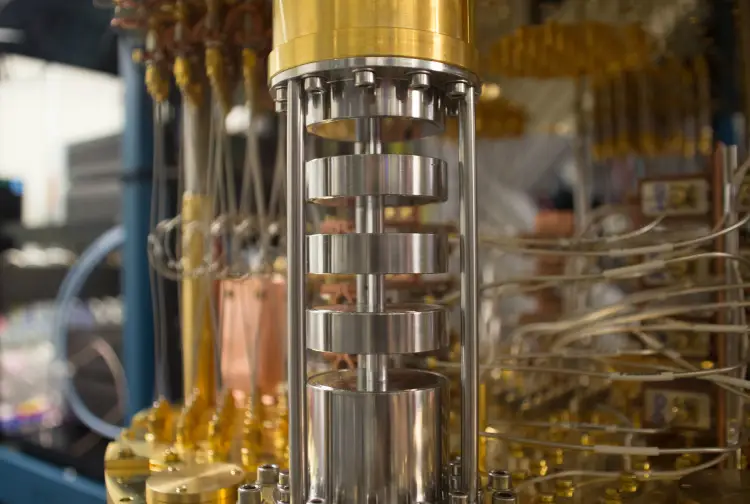
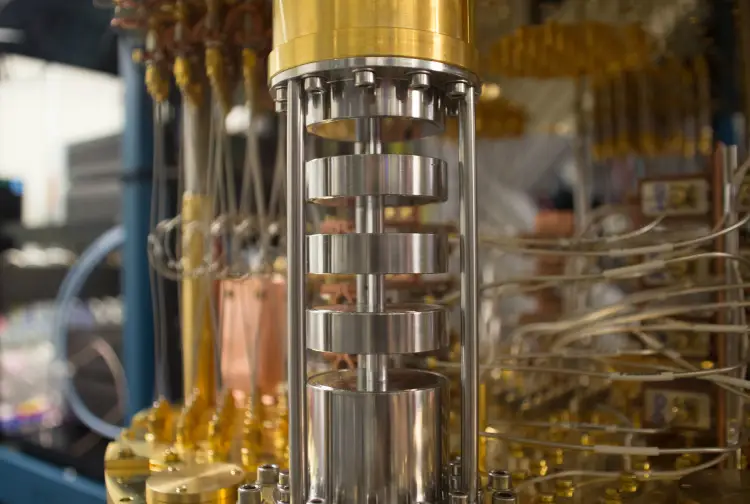
Quantum computing is a market which is coming to maturity. Earlier this month IBM, the market leader in quantum computing, unveiled its Eagle chip, the first to break the 100-qubit barrier. IBM says it believes quantum machines will be outperforming classical computers within the next two years.
As well as boosting military capabilities, advancements in China’s quantum capabilities could lead to a rise in quantum-driven cybercrime, as threat groups seek to get their hands on the latest technologies.
Why is China’s quantum capability a concern for the US?
Much of this worry over China’s quantum abilities is within the context of its geopolitical relationship with the United States, says Greg Austin, senior fellow for cyberspace and future conflict at think tank The International Institute for Strategic Studies (IISS). “The more the US can constrain the development of Chinese supercomputing or the use of US supercomputing capability, the slower will be the development of Chinese missiles and weaponry and spacecraft,” he says.
This is not the first time the US has tried to limit Chinese access to US technology, but its focus is now changing from mainstream systems to emerging technology. “Up to now there’s been a heavy focus on different bits of equipment, banning TikTok and Huawei and 5G” continues Austin. “What’s been happening in the three years since Trump launched the ‘tech war’ is they’ve gradually put more focus on some of the underlying enablers of Chinese advances in military technology, because they’ve been accessing it in ways [the US] doesn’t like.”
Another possible consequence of China and other countries on the Entities List, such as Russia, optimising their quantum capabilities is that encrypted data, documents and infrastructure could be stolen and decrypted using quantum technologies once they are up and running. “A lot of people fear that the era of advanced encryption capabilities of quantum computers will enable China or the United States to decrypt messages that are intercepted now,” Austin says.
Quantum decryption: the threat to businesses
Technology consultancy Booz Allen Hamilton has similar fears, and its new report, Chinese Cyber Threats in the Quantum Era states that “encrypted data with intelligence longevity, like biometric markers, covert intelligence officer and source identities, social security numbers, and weapons designs, may be increasingly stolen under the expectation that they can eventually be decrypted.”
“It’s a current threat, but the impact is in the future,” says IBM’s Michael Osborne. “So everything that we are not protecting today with quantum-safe techniques could be lost into a quantum future. That’s the easiest way to see it.”
Osborne says that when it comes to quantum decryption, there are three main threats to consider. These are “the things we’re building, the data we’re protecting and things like digital signatures, which underpin a lot of digitisation in society,” he says. Unsurprisingly, this covers an incredible amount of sensitive data. “Anything we’re signing today, we will not be able to trust in the future,” Osborne says. “If we’re building systems online, like for house transactions for example, and you have a digital certificate underpinning your claim to property ownership, that could potentially be tricky in future, because it may become easy to [decrypt it and] create other signatures.”
Protections are already available that CISOs and CIOs can incorporate into their cybersecurity models to protect themselves from the growing threat of quantum decryption. The US National Institute of Standards and Technology (NIST) has implemented a Post Quantum Cryptography (PQC) Project, which has been running since 2016 and aims to develop standard algorithms that will protect digital signatures from attacks by quantum computers. In the UK, the National Cyber Security Centre has already designed its first ‘quantum-safe’ cryptographic algorithm.
The authors of the Booz Allen Hamilton report recommend carrying out threat modelling to assess changes to organisational risk posed by the emergence of quantum decryption, as well as developing an organisational strategy for deploying post-quantum encryption, and educating staff to these new risks.
Strict regulation will be required to stop quantum technologies from being used maliciously, argues Osborne. “This will be regulated,” he says. “In the US, NIST will mandate that you have to use this and that algorithm. It’s already the case that the institutions in the US have said you need to start looking and preparing now, and the same in Germany.”
These protective technologies and techniques exist now to protect against future threats, and tech leaders should consider implementing them immediately to avoid great risk.”Anything we’re doing today, which will have a value in the quantum era, should be protected today,” Osborne adds.






