It’s the secret government organisation you’ve probably never heard of: a team some 50-strong working at the heart of British cryptography, whose efforts help to secure the most closely guarded communications of Her Majesty’s Government (HMG).
The United Kingdom Key Production Authority (UKKPA) secures a sprawling array of networks, radios, weapons and other sensitive infrastructure from would-be eavesdropping eyes and ears, using technologies that marry all the technological sophistication and weight of the modern nation state, with tools that one exasperated industry leader close to the work describes as “all a bit 1960s really”.
The task of the little-known UKKPA – technically part of the National Cyber Security Centre (NCSC) which, in turn, falls under the aegis of GCHQ – is to produce, distribute, and audit the use of cryptographic keys. (Strings of characters used within an encryption algorithm for altering data, so that it appears random).
This is not entirely the digital effort the most would presume: while in today’s world, the notion that a cryptographic key might be a tangible thing that requires physically carrying around the country would seem borderline absurd, for the UKKPA physical media is all in a day’s work: in 2018 the authority processed [pdf] 3,800 orders for key material; or 145,000 physical keys for 170 customers across government.
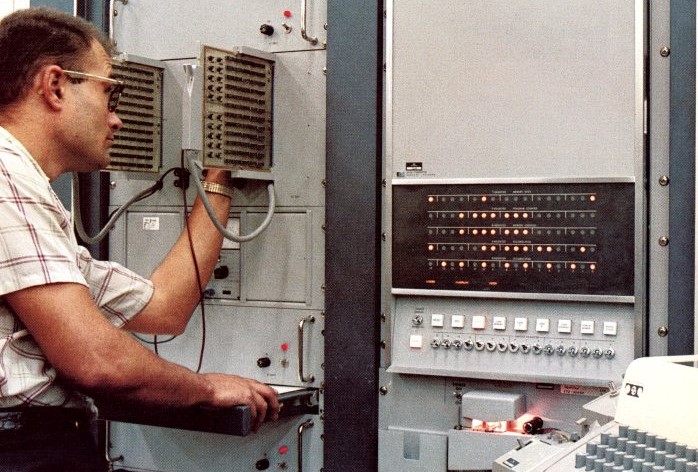
There’s a startling reason for this substantial workload: the UKKPA still uses rolls of punched paper tape for swathes of its key distribution, despite ongoing attempts to phase out its use. (Punched paper tape is a data storage medium. On the ribbons of tape, a hole represents a binary 1, and the absence of a hole a binary 0.)
“We’ll Probably Have a Party”

The UK is not alone in the ongoing use of this legacy technology at the heart of the national security system: across the Atlantic, British intelligence partners at the National Security Agency (NSA) have faced a similar challenge, but appear to be significantly ahead when it comes to phasing out its use.
“[In terms of punched tape key production] we’re down from the millions into the hundreds; the final production line is later this calendar year. Then we’ll probably have a party,” the NSA’s Neil Ziring tells Computer Business Review drily in a call.
The agency’s museum is being lined up to take the production infrastructure, the NSA Capabilities Directorate’s technical director says in an extended conversation, noting: “Our position is that electronic key management is a stronger way of providing cryptographic security to our customers than physical artefacts like a paper tape.”
For the Full Conversation, Read This: NSA Technical Director Neil Ziring on a Hard-to-Kill Technology
The little-known ongoing use of punched tape outside of the sector – “is this a homage to Alan Turing?” one incredulous head of global threat detection asks Computer Business Review – is particularly prevalent among military users, where an eclectic range of systems require robust symmetric encryption, but where change comes slowly, electronic key distribution system roll-out has been patchy, and hardware refresh cycles don’t happen with the press of a button.
Across the military meanwhile, the keys that the UKKPA distributes (Computer Business Review could not obtain a breakdown of key distribution mediums, but understands punched tape volumes are still significant) will be “squirted” into a sweeping range of secure infrastructure, including the cockpits of fighter jets, military radios and submarines.
Firstly, however, they need to get there.
This is where the UKKPA’s “comsec accounting” or information assurance role comes in: the responsibility for not just producing, but distributing, updating, and auditing the keys, which need to be changed on a regular basis: both for security reasons, and because the “boxes” holding them stop working if not refreshed regularly.
Alongside this set of tasks – less James Bond and Q; more Amazon and spreadsheets – it also works closely with a small coterie of private sector partners to develop the hardware that secures these keys, once they have been pulled off punched tape; a partnership crucial to Britain’s sovereign cryptographic capabilities.
Speaking in the NCSC’s austere London offices, deputy director for national security, Jacqui Chard – sporting a nose stud and an aura that suggests she may not suffer fools gladly, despite her patience with Computer Business Review – says: “A majority of the [UKKPA] team are doing ordering and production. Checking and tracking is probably a third of the effort. It’s kind of hard to measure.
“We’ve got customers from the Ministry of Defence (MoD), the Home Office, the police forces, the intelligence agencies to protect our communications; so those kinds of customers use our materials: all the kinds of places where the government wants to protect its most sensitive material, and its using these crypto boxes to do that.
“There are some commercial customers, but those are when they are providing services to government. So they might be a service provider of a network system into the MoD that’s running the system in which the boxes are in, so they need the keys to run the system, but it’s under the authority of the MoD in that case.”
“Helping Industry Sort out Interfaces”
She adds: “We’ve got a really good industrial base in the UK that designs, develops and manufactures modules, boxes, racks. As our military forces, our departments change their networks, change their operating structures, change their communications needs; as NATO has new missions, what’s required of any of the network components changes.

“As a result, quite often we’re involved with helping industry sort out the interfaces of the boxes; the really straightforward stuff.”
For all the deputy director’s no-nonsense explanations it is, perhaps predictably, here that things start to get somewhat less than straightforward than she suggests.
Many Plates to Spin…
The deputy director presides over a challenging task: with HMG intent on sustaining a sovereign capability in cryptography – which promises freedom of military action, among other benefits – she needs to help balance a complex array of requirements from multiple parties.
These, in essence, boil down to making sure that indigenous private sector partners are on tap with the capabilities needed at this level, despite not being able to offer them the visibility into demand (and tools to create it) that you get in unrestricted commercial market. With government procurement being a sometimes dysfunctional and sclerotic thing, this is a delicate juggling act.
Many of the private sector partners that make the hardware (known colloquially as “cryptos”) for the keys chafe as a result at their heavily reliance on HMG as a customer. Their grumbles seem somewhat well rehearsed, but the unpredictability of government procurement, and the restrictions placed on the export of devices HMG wants to retain as sovereign are frustrating. (Many augment these sales with exports to Five Eyes and other British partners, but there are limits to this too).
HMG: Enabler, Barrier; Both…
Richard Flitton, managing director of L3 TRL; a Tewkesbury-based specialist in advanced electronic security systems, sums up some of the frustrations. He tells Computer Business Review in a call: “The government wants a sovereign capability in its secure communications; particularly encryption.
“And to do that obviously it needs to have a UK industry that supports that. The government could potentially do it itself – but whether that would be efficient, effective or even viable is an open question. So industry steps in.
“The issue with the UK market is that it is profitable, but it’s unpredictable; it’s non-linear. At the moment it is pretty much a managed market.
“There are opportunities to bolster that by selling devices into overseas markets: we’ve been quite successful at selling into Australia and Canada, and much smaller amounts to some of our close friends in Scandinavia.
See also: Landmark GCHQ Publication Reveals Vulnerability Disclosure Process
“But typically the list of people that the UK government is willing to share even some technology with is fairly short. And in terms of the UK sovereign cases that’s really the challenge. There are certain technologies and certain algorithms that they want to be completely UK – so for obvious reasons you can’t sell those in export. Yet if you want to sell slightly different or adapted capabilities for export that’s ‘sort of’ possible.”
He adds: “The challenge then becomes what are the rules and guidelines and what is permissible and what’s not permissible… for all Jacqui’s team’s work, government often seems more like a barrier than an enabler. We’re not a huge company, but equally we’re not a startup of the type that Ministers like to champion. So you kind of end up in the middle, where you’re not really part of industrial strategy…”
“A Crashing End”
Others mutter darkly about a botched paper tape replacement programme some years ago: overly ambitious and poorly executed, it “came to a crashing end”.
Few interviewees are keen to offer details or point fingers, but it is clear that the lessons still sting. A more progressive, piecemeal effort to digitalise cryptographic key management is underway, but many industry partners say more could be done. And some say that they fear physical key distribution is both unsafe and inefficient.
(A sceptic would suggest that they are talking up their own book, but there is precedent. As the NSA’s Neil Ziring tells us: “Key tape segments were originally shipped around in plastic bags, until the spies Walker and Whitworth used to nick things out of the plastic bags, copy them and pass them to the Russians.” They’ve since been transported in tamper-resistant canisters.)
L3 TRL’s Richard Flitton says: “There’s two issues here: one is that you’ve got to distribute the key, so you’ve got to physically move the things around the country or even overseas. If you’re moving things they’re vulnerable to being intercepted or compromised. Then secondly there’s the cost and logistical burden of doing all that.
“The authority has a huge challenge to produce all those keys and then it’s got a challenge to distribute and install them all.
“And that’s not insignificant by the way. I won’t describe what happens. But if Joe Public knew, you would think this was all a bit 1960s really.”
MoD “Lives, Breaths and Sleeps Physical Media”
Adrian Cunningham, technical director of Amiosec, a Tewkesbury-based high-grade encryption technologies and applications specialist, tells Computer Business Review: “The challenge is that there is such a wide variety of platforms that these devices are installed into: they’re not always online, and they’re not always in-country.
“You’ve also got the challenge that we need to talk to other people [e.g. other NATO partners], so interoperability issues belong either below, or on top of that too. But with MoD, they live, breathe and sleep handling physical media and accounting for it. There’s a massive business change that needs to take place to move away from that.”
He adds: “With all the evaluation and rigour that goes into these products you can’t churn them very easily. Products used to take eight years to build. That’s now come down to around three years typically, but in this modern age, that’s still too long.
“From our perspective we’re focussing on the mobility side; secure remote access from inside and outside the office. We have an opportunity in that space where the old legacy systems just aren’t going to work. We are hoping that key management systems that are being developed by Jacqui and the team are pulled through – sooner rather than later – in the mobile space.”
(All of the people interviewed for this piece highlighted the challenges of facilitating remote and flexi-work arrangements for staff in the national security space: as in all sectors, high calibre recruits want a little wriggle room on location…)
“People Want to be on the ‘Sexy’ End of the Industry”

Ian Goslin, managing director of Airbus CyberSecurity, another close security partner of HMG, tells Computer Business Review that efforts to keep this niche industry vibrant are needed: the NCSC’s “CyberFirst” programmes are a great start, but more is required, he suggests, amid competition for talent.
He says: “When you’re not in a high volume industry, but you have to turn out products of such a standard, the barriers to entry are large.
“You can count the players who have the ability to develop products in this space on two hands – and you’re probably not filling up two hands. As a result, you end up having an intimate relationship with your customer base [because] NCSC are not in the business of producing products. If we are to sustain a small industry, we have to ensure that when we generate experts we get best value from them.
“People want to be on the sexy end of industry; hackers and the like… We have to do more to make the industry more attractive. We have to make it absolutely clear that there is a growing opportunity in the high grade crypto key place.
“The market has to have enough money in it to make it attractive to the players in it. There needs to be a clear strategy for valuing and rewarding those in the space.”

“Steven Snodgrass is Looking at it and his Head is Exploding Because It’s so Bloody Difficult to Use”
With interface and interoperability issues an ongoing challenge, one company that steps in to help with testing new products as modernisation efforts continue is QinetiQ, the company spun off from the MoD’s late Defence Evaluation and Research Agency in 2001.
QinetiQ’s managing director for cyber, information and training, James Willis tells Computer Business Review: “We have a model office environment where manufacturers and governments can come and test the process within the crypto to allow them to make sure it works and assure how they are using crypto.
“That way it’s both secure from an information perspective and it’s efficient. You can have greatest crypto process in the world, but if some poor guy in a submarine trying to do some validation of codes in crypto can’t use it because it’s so bloody inefficient or difficult to use… if Steven Snodgrass is looking at it and his brain is exploding because he doesn’t have the support of some research scientist who’s come up with a horrendous process to use it, then that’s no good for anyone.
“So we sit with NCSC [UKKPA] who create the keys and work with MoD to work with user requirements and user operator interface.
He adds, with regard to broader modernisation efforts: “There have been learnings from the previous programme, which was probably too wide in scope. They’ve broken it down and it’s moving forward. I think the crypto manufacturers always wanted to move forward quicker, because they’ve got development programs to fund, things like that. In a small market limited by the classifications we operate in, they’ve got to make a return on their investment as soon as they can.
“I think the good news is that NCSC and MoD absolutely recognise that.”

UKKPA: Keys for HMG, and NATO…
An additional responsibility for the UKKPA, meanwhile, is NATO.
The authority is one of just two cryptographic key suppliers to the military alliance; the other being the NSA: both provide keys for distribution via an entity called DACAN. (Canada for decades shared the workload, before deciding to shirk its share of the heavy lifting sometime around the year 2000).
The NATO role, the NCSC’s Jacqui Chard says, takes up about 25-30 percent of the UKKPA’s time. Once again, it comes with a host of interoperability issues that mean simple rip-and-replace with secure networks and digital keys is no simple task.

That’s not to say that progress is not happening across NATO and the industry.
As the NSA’s Neil Ziring tells us: “For [some] devices, especially ones that would be on a network to begin with – like a link encryptor – we have been moving towards ‘all over the air’ or ‘over the network’ key management, where a device can actually contact a key management system on its own, and if it is properly authorised then it will be given a key.”
Such innovations remove workload and are welcomed by many. But can military users expect every single bit of hardware to always be ‘on air’? And if not, how, exactly, does digitalised key management work?
As Neil Ziring explains: “A base or a depot would have an outpost of the key management system – there are various form factors for that – right on base.
“If they’re trying to put keys into some military aircraft; they’d have ‘fill devices’ in the hanger, you fill up the key fill device from the KMS, you take it around the airplanes – you’re talking about walking a couple hundred meters… It’s not like trying to ship it (a key fob) from Maryland out to a base from the other side of the world.”
Farewell to “Man-in-a-Van” Key Management?
Airbus is among the companies to have won recent contracts in the UK to update systems for the MoD, using similarly up-to-date techniques.
As the company’s Ian Goslin tells Computer Business Review: “We have one unit on the Typhoon call the Aircraft Variable Crypto Unit (AVCU) that allows all the keys to be injected in one go. It acts as a crypto custodian on the aircraft, offering up the right key to the pilot to when they load it. The root of that key is always the UKKPA.
“In the ‘good old days’ where distribution used to be ‘put a bunch of key tape into the back of a van, driven to a HQ, they’d take and log and distribute it to different units – it was a man-in-a-van exercise – we’re now moving keys electronically via speciality networks.”
It sounds like the shape of things to come. But for the time being, the UKKPA’s punched paper tape machine has more than a few production runs to do before it joins its NSA counterpart in museum-bound retirement.
It is a powerful reminder that modernising legacy systems is never entirely easy, even if – or rather, particularly when – those systems are mission-critical.
Learn about these technologies and more at the exhibition “Top Secret: From Ciphers to Cyber Security” which opens tomorrow, July 10, 2019 at the Science Museum and which coincides with/commemorates GCHQ‘s 100th anniversary.






