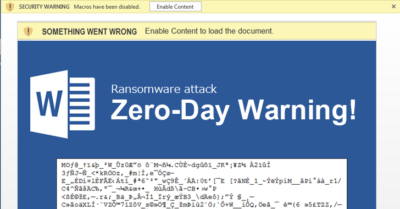
It has been revealed by researchers that a critical Microsoft Office zero-day attack has been targeting Word users since late January. The yet-to-be-patched vulnerability lets hackers remotely execute code on a targeted computer by luring users into opening a Word document which contains an embedded exploit.
Security researchers from McAfee and FireEye discovered that the attack works on all Microsoft Office versions, including the latest Office 2016 that runs on Windows 10, which security experts had previously had faith in as one of the most secure OS.
Explaining the zero-day in detail, FireEye explained:
“When the user opens the document, winword.exe issues a HTTP request to a remote server to retrieve a malicious .hta file, which appears as a fake RTF file. The Microsoft HTA application loads and executes the malicious script. In both observed documents the malicious script terminated the winword.exe process, downloaded additional payload(s), and loaded a decoy document for the user to see. The original winword.exe process is terminated in order to hide a user prompt generated by the OLE2link.”
Therefore, as McAfee believes, the threat could be used to deliver multiple types of malware. Due to the it being a logical bug, it can also navigate around any memory-based mitigations.
Read more: Microsoft takes a back seat to Philip Hammond and security
“The successful exploit closes the bait Word document, and pops up a fake one to show the victim. In the background, the malware has already been stealthily installed on the victim’s system,” said McAfee in a blogpost.


FireEye confirmed that its researchers had shared details of the vulnerability with Microsoft and had been working with the tech giant for several weeks in request for public disclosure along with the release of a patch by the company.
Following this, both McAfee and FireEye have advised Microsoft Office users to apply the patch once it is available.
McAfee also advised:
“Do not open any Office files obtained from untrusted locations. According to our tests, this active attack cannot bypass the Office Protected View, so we suggest everyone ensure that Office Protected View is enabled, said McAfee.”
According to reports, a patch for the Microsoft Office zero-day could be released by the tech giant as early as tomorrow, April 11th.






