Russian cybercrime gang APT28, also known as FancyBear, exploits a vulnerability in Microsoft Outlook to target energy, transportation and government organisations across North America, Europe and the Middle East.
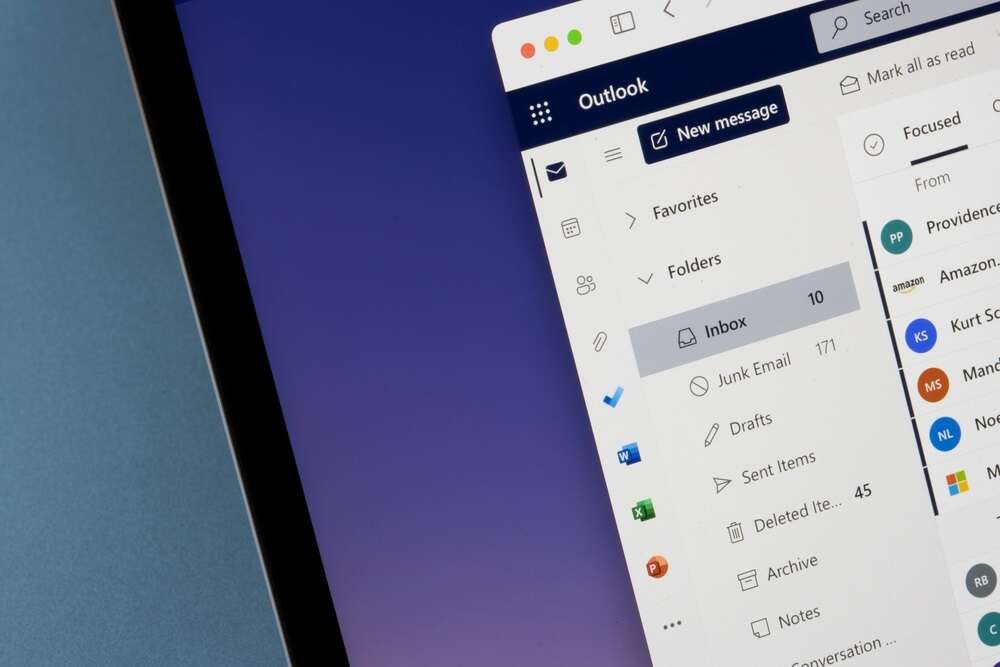
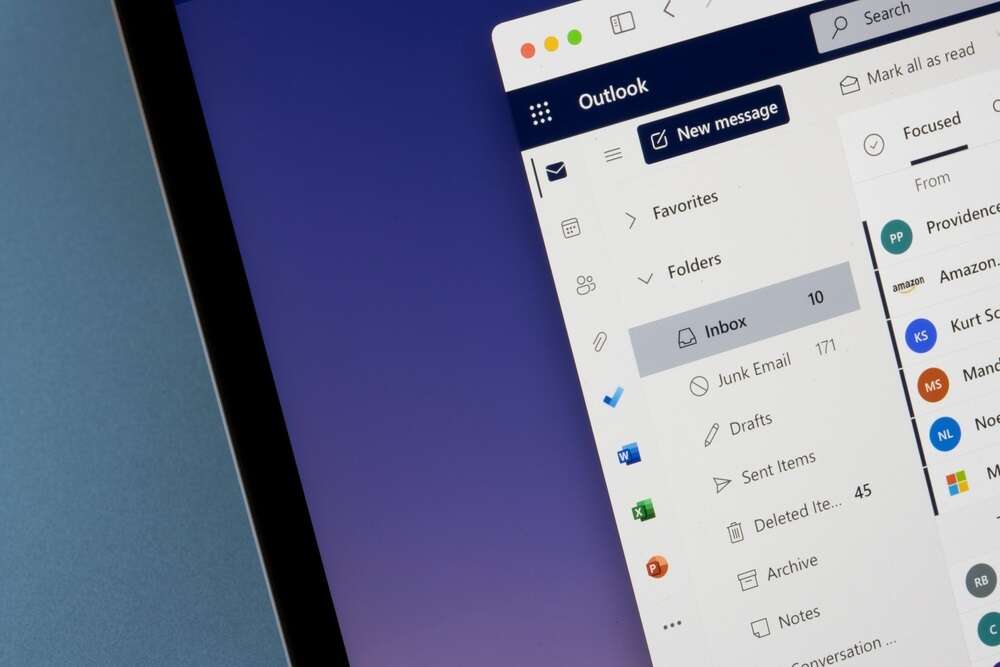
Microsoft has issued a new warning about the flaw, known as CVE-2023-23397, and says it is being used to obtain unauthorised access to email accounts within Microsoft Exchange servers. Microsoft recommended that all users verify that their versions of Microsoft Outlook are patched.
CVE-2023-23397 is a vulnerability in Outlook’s privilege settings on Windows and was patched by Microsoft in March. Despite this, it has persisted in an unknown number of systems around the world. It can be exploited through the dispatch of a specially crafted email to the target that allows for the theft of the user’s NTLMv2 hashes, which can be used to alter the victim account’s privilege settings. “The user does not need to interact with the message” for an Outlook account to be hijacked through the exploitation of this vulnerability, a newly published advisory from Microsoft warns. “If Outlook on Windows is open when the reminder is triggered, it allows exploitation.”
Microsoft’s complicated history with APT28
Microsoft said that one of the most prolific exploiters of this flaw has been the cybercriminal organisation APT-28, which used it to hack a string of French government agencies in October and Ukrainian organisations in June. Otherwise known as “STRONTIUM” and “FancyBear”, the gang has been linked to Russia’s GRU intelligence agency by both the US and the UK. Microsoft revealed that it had recently partnered with the Polish Cyber Command (DKWOC) to “identify and mitigate techniques used by the actor” in recent attacks on targets in Poland. In a separate advisory, however, the agency warned that APT28 was still employing these methods at the time of writing.
Microsoft strongly recommended that users apply security updates for CVE-2023-23397 and another vulnerability, CVE-2023-29324, to Outlook and Exchange. Passwords should also be reset and multi-factor authentication enabled for compromised users. “While leveraging NTLMv2 hashes to gain unauthorised access to resources is not a new technique, the exploitation of CVE-2023-23397 is novel and stealthy,” Microsoft added.
APT28 also has a history of targeting all organisations with unpatched vulnerabilities in its suite of Microsoft software programs. In September, for example, APT28 hackers launched spear-phishing attacks against the Ukrainian government through fake Windows update emails. Earlier this year, meanwhile, the UK’s National Cyber Security Centre warned that the gang was exploiting vulnerabilities in unpatched Cisco routers, flaws that had been identified as early as 2017.






