Cyber attacks and hacking have risen to a new pinnacle of prominence in only the last few years as attacks have become capable of effecting vast numbers of people. It has become commonplace that we hear of hundreds of thousands, or even millions, of customers having their data stolen by cyber criminals, and that nobody is safe.
Attacks such as these have grabbed headlines in mainstream news, with instances such as the WannaCry ransomware attack reaching the front pages of newspapers. People are becoming familiar with the fact that even their televisions and fridges could be compromised by a hacker.
While the notoriety of cyber crime has exploded only relatively recently, the origins of the cyber attack began long before ransomware, malware or phishing were ever spoken of.
With a history stretching back to the very beginning of the last century, it is clear that humans have always been lured by the dark attraction of launching a powerful, anonymous attack, or picking the locks of technology.
The origin
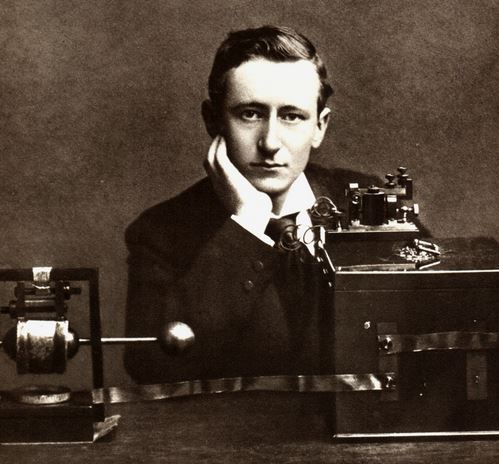
The year 1903 marks the first instance of hacking, and the man at the seminal point of the timeline was nothing short of a magician. Manager of a wireless telegraphy company, and magician, Nevil Maskelyne stood in opposition to the famous Guglielmo Marconi, the long-distance radio transmission pioneer.
Marconi had succeeded in being considered the first to send a wireless telegraphic message in history in the year 1885. This involved electromagnetic waves representing the dots and dashes of Morse code. This would ultimately earn him a Nobel Prize for Physics, and even titles of nobility.
At a public display of the security and privacy that his method of wireless telegraphy could provide, Maskelyne took the opportunity to strike. At the Royal Institution in London, John Ambroise Fleming was poised to receive a message sent by Marconi from Cornwall.
Maskelyne intercepted the process, tarnishing Marconi’s promise of security, and repeatedly sending the word “Rats” within the message. Fleming was shocked upon interpreting the message, and referred to the act as “scientific vandalism”, a concept that seems eerily familiar to the malicious, hooded hackers of today.
Cracking the code

In 1939 there was another great stride towards the cyber world of today, in an instance of what might now be considered a form of nation state activity.
This example is of course the decryption device used at Bletchley Park by British cryptologists to decipher encrypted German messages during the Second World War. This device was known as the Bombe, and the US Army and Navy soon developed similar designs.
The great mathematician, cryptanalyst and computer scientist, Alan Turing was behind this device that was so crucial to the allied victory. Gordon Welchman and Harold Keen were also instrumental in the device’s creation. Using this device, settings of German Enigma machines could be gradually discovered to decrypt critical military messages.
Hacking as we know it is born
In 1963 the term “hacking” and “hackers” became directly linked to malicious activity. A MIT newspaper covered the story of people managing to use an early computer, the Programmed Data Processor-1 (PDP), to make free calls. Use of the term “hack” had been used to refer to activity that involved tampering with machines to influence their processes.
Shortly after this point, in 1965, a Compatible Time-Sharing System (CTSS) was found to be vulnerable. This was running on an IBM 7094 computer system, this occurred when a password was switched with another file when two people were working on the device.
Then in 1979, an information technology consultant managed to hack into the Digital Equipment Corporation computer system. This instance is marked as the first time a major system was compromised. Mitnick went on to further activity to earn the title of being a hacker.
‘Technical experts; skilled, often young’
In 1980 hacking had reached a new height when it came under investigation by the FBI. The incident was a security breach of the time-sharing firm National CSS.
The New York Times described these mysterious perpetrators at the time, saying that hackers are: “technical experts; skilled, often young, computer programmers, who almost whimsically probe the defenses of a computer system, searching out the limits and the possibilities of the machine. Despite their seemingly subversive role, hackers are a recognized asset in the computer industry, often highly prized.”
In 1983 another major shift toward the modern world of hacking and cyber attacks took place, as the comparatively huge number computers were breached, 60 in fact, by a gang of hackers called The 414s. This formation and organisation of a group of malicious cyber adversaries is also a common factor is the modern world.
After the issue had grown in size, and awareness had been raised to the dangers of this new and fast emerging form of crime, the Computer Fraud and Abuse Act was passed in the United States, legally criminalising this kind of activity.
The dark era of today
An example of an attack that scars modern cyber history is Heartbleed, a bug that was turned into OpenSSL. Hackers used this to construct portals through which to access databases. Many would argue that this was the largest cyber attack the world has ever seen, with reports stating that 17% of all websites were affected.
The scale of attacks since the turn of the 21st century has grown at an exponential rate, and this is hardly a surprise with the internet becoming so rapidly ingrained in so many people’s lives. Other major developments include the huge influx of devices, meaning that we are connected and vulnerable at all times.
Internet of Things devices also present a whole world of new cyber risks, with many devices carrying insufficient cyber security features, and they are now imbedded in the homes and workplaces of millions of people across the world.
READ MORE: SCADA cyber attacks: Eugene Kaspersky warns of global blackout
Nation state activity has also mutated into a monster unrecognisable from the times of decrypting German military Enigma messages, with governments now employing many deadly forms of attack for the purposes of warfare.
SCADA attacks for example have been used to knock out power grids in the Ukraine, and fears at this very moment are growing in regard to the potential for attacks on critical infrastructure such as power plants.






