A misconfigured Akamai CDN (content delivery network) server and files with the password “intel123” have been pinpointed as the apparent cause of a major leak from Intel which has seen 20GB of source code, schematics and other sensitive data published online.
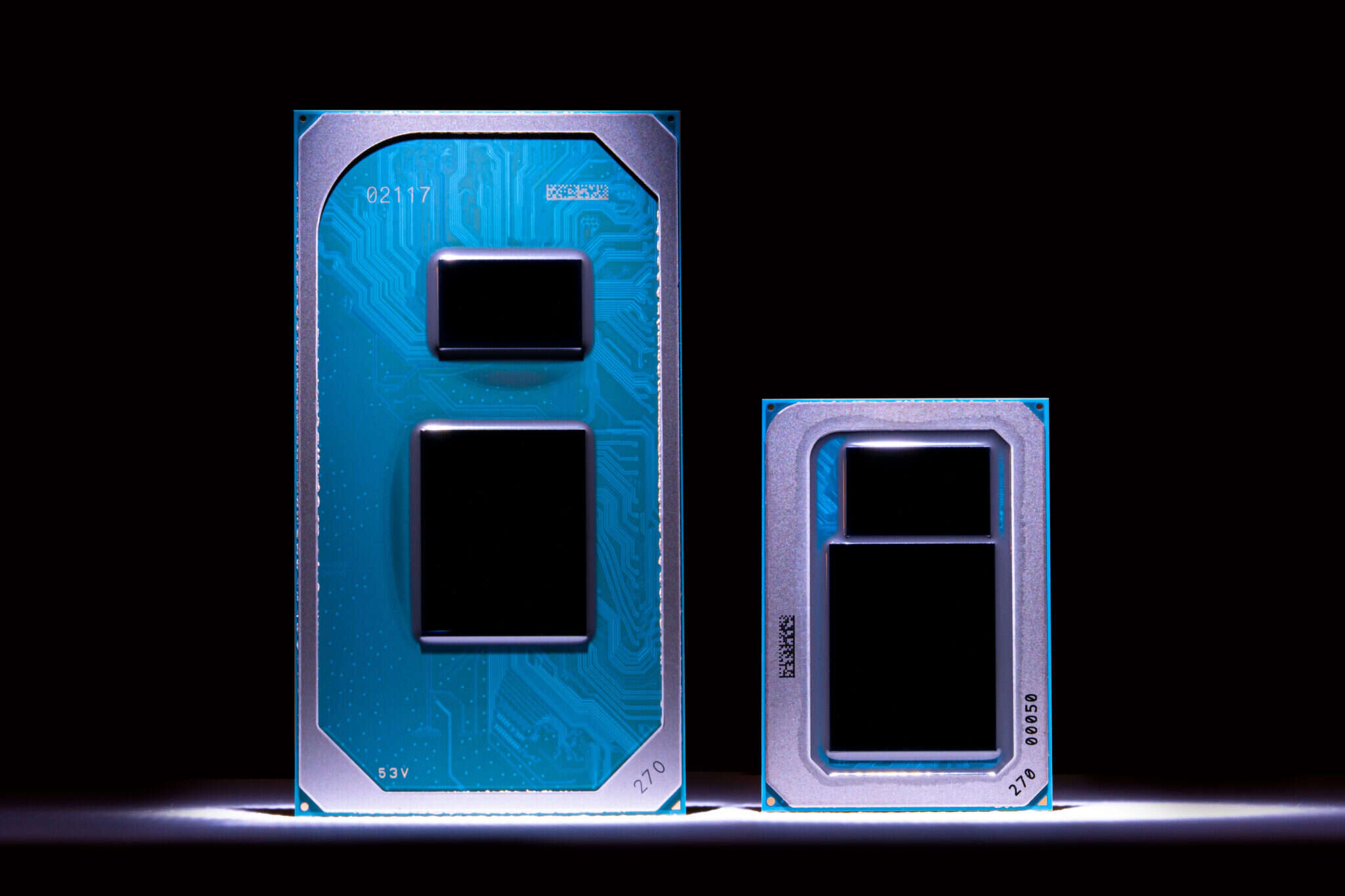
The leak, posted last night by Tillie Kottman, an IT consultant based in Switzerland, contains files provided to partners and customers by chip maker Intel under non-disclosure agreement (NDA), and includes source code, development and debugging tools and schematics, tools and firmware for the company’s unreleased Tiger Lake platform.
Read more: Intel’s 7nm ‘Defect’ Leaves Investors Fretting
In a now-deleted post, the alleged source of the leak said: “They have a service hosted online by Akami CDN that wasn’t properly secure. After an internet-wide nmap scan I found my target port open and went through a list of 370 possible servers based on details that nmap provided with an NSE script.
“The folders were just lying open and I could just guess the name of one. Then you were in the folder you could go back to the root and just click into the other folders that you don’t know the name of.

“Best of all, due to another misconfiguration, I could masquerade as any of their employees or make my own user.”
The source added that though many of the zip files on the folder were password-protected, “most of them [have] the password Intel123 or a lowercase intel123.”
Intel exconfidential Lake Platform Release 😉
This is the first 20gb release in a series of large Intel leaks.
Most of the things here have NOT been published ANYWHERE before and are classified as confidential, under NDA or Intel Restricted Secret. pic.twitter.com/KE708HCIqu
— Tillie 1312 Kottmann #BLM ???? (@deletescape) August 6, 2020
Kottman expects the data dump will be the first in a series of leaks from Intel.
“Unless I am misunderstanding my source, I can already tell you that the future parts of this leak will have even juicier and more classified stuff,” he said on Twitter.
A spokesman for Intel said the chipmaker is investigating the leak, but declined to comment on the claims about the misconfigured server and weak passwords.
She said:“The information appears to come from the Intel Resource and Design Center, which hosts information for use by our customers, partners and other external parties who have registered for access.
“We believe an individual with access downloaded and shared this data.”
The incident is a stark reminder — if any were needed — that proactively mimicking these kinds of tactics by hackers is crucial to enterprise security, whether that is via regular Red Teaming, or other tactics.
Recent security guidance from the NSA (focussed on OT environments, but applicable across many IT environments too), noted that best practices include:
- Fully patching all Internet-accessible systems.
- Segmenting networks to protect workstations from direct exposure to the internet. Implement secure network architectures utilizing demilitarized zones (DMZs), firewalls, jump servers, and/or one-way communication diodes.
- Ensure all communications to remote devices use a virtual private network (VPN) with strong encryption further secured with multifactor authentication.
- Check and validate the legitimate business need for such access.
- Filter network traffic to only allow IP addresses that are known to need access, and use geo-blocking where appropriate.
- Connect workstations to network intrusion detection systems where feasible.
- Capture and review access logs from these systems.
- Encrypt network traffic to prevent sniffing and man-in-the-middle tactics.






