A controversial report alleging that China sneaked spy chips built to look like signal conditioning couplers into the motherboards of data centre servers across 30 companies, including Amazon, Apple and the US government has resulted in a flurry of corporate interest in hardware security audits, according to one specialist, Joe FitzPatrick.
The story, vehemently denied by all named parties, has seen the share price of Super Micro, the company allegedly impacted, fall over 40 percent, after Bloomberg, citing 17 unnamed sources, said investigations were still ongoing into the 2015 incident.
Both the US’s Department of Homeland Security and the UK’s National Cyber Security Centre say they have “no reason to doubt the detailed assessments” made by AWS and Apple. The story has triggered huge interest and controversy in the cybersecurity industry, with Bloomberg’s artist’s impressions of the rogue hardware pulled apart for further clues into the alleged compromise.
Zooming in on the Bloomberg animation showing the alleged malicious component in the Supermicro servers looks reasonable for the described attack. It is positioned on an unpopulated SOIC-8 SPI flash footprint between the SOIC-16 SPI flash chip and the BMC. pic.twitter.com/EdFweJk0EE
— Trammell Hudson ⚙ (@qrs) October 4, 2018
Hardware Security Audits: Not for the Faint of Heart
But FitzPatrick, an Instructor and Researcher at SecuringHardware.com, wrote in a blog this week: “Without an IOC [indicator of compromise], you need to do a time consuming, thorough, invasive, destructive analysis of every component on your board. This is EXPENSIVE. If it’s not time consuming, invasive, destructive, and expensive, you’re not getting a thorough job.”
Any such audit would involve electrically analysing the inputs and outputs of any unexpected modules (after checking with the vendor that they weren’t supposed to be there) in a live system. Then removing the part, dumping and analysing any firmware they might have; decapping and imaging the part and comparing to a known good identical part.
See also: Bombshell Report Warns of Huawei Risk to UK’s Critical Infrastructure Security
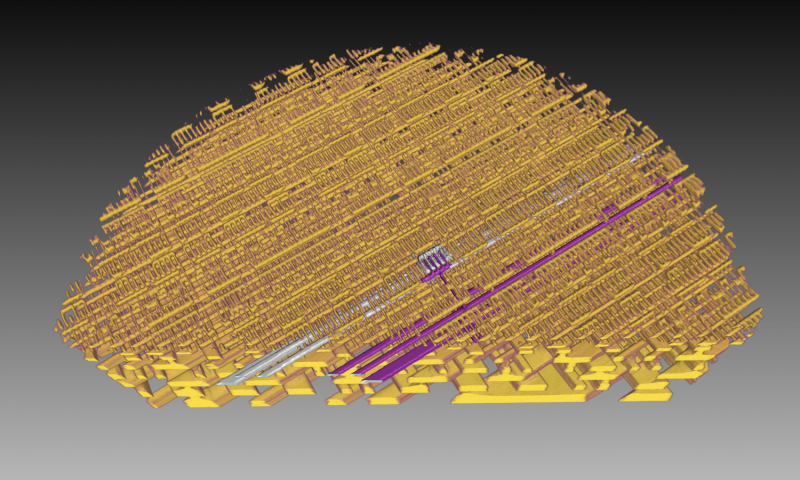
“Next, X-ray the whole board. Identify any differences between your board and board layout diagrams. Identify any components that don’t look exactly like they should, and repeat the component analysis process on each of them…”
He said: “It’s unlikely you’re affected. Really. Even assuming every claim is true, and even if there is a secret device on every single X brand motherboard, it’s unlikely you’re targeted by whatever payload the implant carries.”
Hector and others have identified the component used in the bloomberg article to represent the hardware implant. I'd like to share my perspective on whether it's realistically possible: https://t.co/fPsuETfFDh
— Joe Fitz (@securelyfitz) October 5, 2018
AWS Rebuttal
In a Detailed Rebuttal Late Last Week, AWS’s CISO Steve Schmidt wrote: “There are so many inaccuracies in this article as it relates to Amazon that they’re hard to count… when Amazon was considering acquiring Elemental [the servers of which allegedly contained compromised Supermicro motherboards], we did a lot of due diligence with our own security team, and also commissioned a single external security company to do a security assessment for us as well. That report did not identify any issues with modified chips or hardware. As is typical with most of these audits, it offered some recommended areas to remediate, and we fixed all critical issues before the acquisition closed. This was the sole external security report commissioned.”
He added: “We never found modified hardware or malicious chips in servers in any of our data centers… Amazon employs stringent security standards across our supply chain – investigating all hardware and software prior to going into production and performing regular security audits internally and with our supply chain partners. We further strengthen our security posture by implementing our own hardware designs for critical components such as processors, servers, storage systems, and networking equipment.”
Apple, meanwhile said: “As a matter of practice, before servers are put into production at Apple they are inspected for security vulnerabilities and we update all firmware and software with the latest protections. We did not uncover any unusual vulnerabilities in the servers we purchased from Super Micro when we updated the firmware and software according to our standard procedures.”
The company added: “We are deeply disappointed that in their dealings with us, Bloomberg’s reporters have not been open to the possibility that they or their sources might be wrong or misinformed. Our best guess is that they are confusing their story with a previously-reported 2016 incident in which we discovered an infected driver on a single Super Micro server in one of our labs. That one-time event was determined to be accidental and not a targeted attack against Apple.”
But…
Just this month the US government launched several government-industry initiatives to develop “near- and long-term solutions to manage risk posed by the complex challenges of increasingly global supply chains… to strengthen our nation’s collective cybersecurity and risk management efforts”, the DHS said however.
As Joe FitzPatrick concluded: “If you’re bold, you could be the first to publicly disclose full details of an actual malicious hardware implant. Double up on your foil, find a bunker, use tor, use signal, and tell everyone.”






