An 18-strong alleged ATM skimming gang has been arrested after netting an estimated $20 million in a crime wave across the US.
New York Attorney General Geoffrey S. Berman, unsealed indictments against gang today, charging them with access device fraud, wire fraud, bank fraud, and aggravated identity theft among other suspected crimes.
The primarily Romanian gang, who went by the sobriquets like “The Boy”, “Johnny Ion”, “Sobo” and “Pitica”, even manufactured fake debit cards as part of their operations, the Attorney General’s office said.
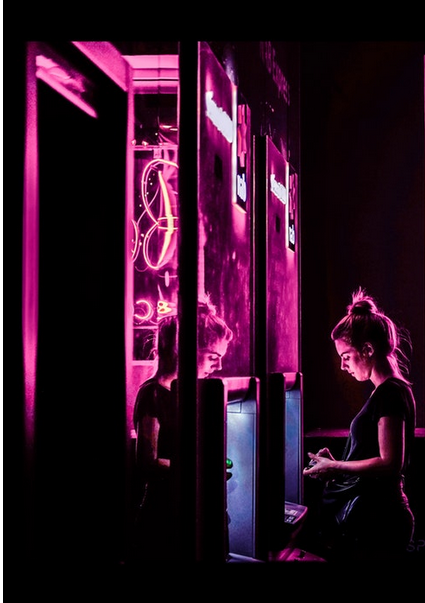
The crew used “advanced technological devices to surreptitiously record the debit card numbers and personal identification numbers at automatic teller machines (“ATMs”), and then manufactured counterfeit and fraudulent debit cards that bore the victim accountholders’ account information” Berman’s office claimed.
Berman said: “As alleged, the defendants participated in a wide-ranging international ATM skimming and money laundering operation, using their technological know-how to steal tens of millions of dollars from financial institutions and individual victims. Thanks to the FBI, CBP, and the NYPD, the defendants are in custody and facing felony charges for their alleged offenses.”
“Other defendants assisted in receiving packages containing skimming devices or component parts that were shipped from other parts of the U.S. and from abroad.

“Other defendants assisted in engineering the skimming devices that the Skimming Organization used. Still other defendants laundered the proceeds of the skimming attacks through bank accounts, properties, businesses, and the transportation of bulk cash” they said in a statement Monday.
Read also: Hack for Cash: These ATMs Take Just 20 Minutes to Crack
The security firm Positive Technologies late last year claimed that 85 percent of ATM cash machines can be hacked and tricked into dispensing cash within 20 minutes.
They targeted ATMs belonging to GRGBanking, NCR and Diebold Nixdorf and found four main vulnerability categories: insufficient network security; insufficient peripheral security; improper configuration of systems or devices; and vulnerabilities within the configuration of the application control.
The team’s researchers wrote in their report that due to the insufficient network security a criminal with access to the ATM network can “target available network services, intercept and spoof traffic, and attack network equipment.”
“Criminals can also spoof responses from the processing center or obtain control of the ATM”, they claimed, noting that poor physical security was the weakest link in the ATM security chain.
Each defendant arrested today is charged with one count of conspiracy to commit access device fraud, which carries a maximum sentence of seven and a half years in prison; one count of conspiracy to commit wire and bank fraud, which carries a maximum sentence of 30 years in prison; and one count of aggravated identity theft, which carries a mandatory sentence of two years in prison, consecutive to any other sentence imposed.
Berman’s office thanked the FBI, CBP, the NYPD, the United States Postal Inspection Service, INTERPOL-Rome, INTERPOL-Mexico City, and Mexico’s Agencia de Investigación Criminal and Instituto Nacional de Migración for their assistance.






