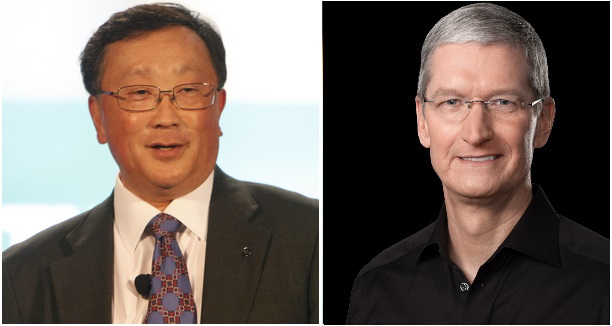
A post by John Chen, CEO of BlackBerry, on the official BlackBerry blog, saying that "we are…in a dark place when companies put their reputations above the greater good" seems to have widely been taken as a dig at Apple over its recent FBI feud.
Chen’s comments followed revelations around a recent case in Canada in which BlackBerry had helped the Canadian authorities, leading to a "major criminal organisation being dismantled".
"We have long been clear in our stance that tech companies as good corporate citizens should comply with reasonable lawful access requests," Chen wrote.
The comments attracted some criticism, with Kevin Bocek, VP Security Strategy at Venafi, saying that the "statements amount to supporting the tearing down the system of trust that the Internet itself relies on."
Saying that the FBI battle with Apple had set a precedent "not about breaking encryption but about breaking the systems of trust and privacy that have allowed the Internet to flourish", Bocek further commented that this was a danger in the context of increasing attacks on these systems by cybercriminals.
Compared to the very public dispute over access to the iPhone of San Bernandino killer Syed Rizwan Farook, BlackBerry seems to be sounding a comparatively conciliatory note towards governments.
In mid-February, US Magistrate Judge Sheri Pym ruled that Apple had to provide the FBI with software to make it easier to hack into the phone. Apple appealed against the decision.
However, before the case actually came to court, the FBI were able to unlock the smartphone with the help of an unspecified third party. Apple never had to weaken its protections.
The Apple-BlackBerry comparison in this case belies some key differences between the two cases and similarities between the approaches of the two companies.
For one thing, although Chen does not give specifics, BlackBerry is not necessarily claiming to have done anything that Apple refused to do. Chen said that the BES server was not involved and continues to be impenetrable, suggesting that there is a limit to how far BlackBerry would go in providing access: the limit being BlackBerry’s duty to its customers.

Chen would not say whether Canadian authorities had been provided with a master key of some kind to decrypt messages.
In the Apple case, Apple had actually been ordered to develop a new version of the iOS operating system, circumventing several important security features, and install it on an iPhone recovered during the investigation.
"Building a version of iOS that bypasses security in this way would undeniably create a backdoor," said Apple CEO Tim Cook in a letter to customers explaining the decision.
Apple’s stand was supported in a submission to the court by Apple’s tech compatriots including Box, Google, Facebook and Microsoft, in which they argued that the government’s order to Apple "will harm Americans’ security in the long run."
Chen meanwhile wrote in his post that his company’s product is "without the ability for backdoor access".
Additionally, while Chen reaffirms the company’s "lawful access principles", Cook said that Apple "has great respect for the professionals at the FBI, and we believe their intentions are good. Up to this point, we have done everything that is both within our power and within the law to help them."
If there appear to be little differences between the companies’ approaches, some of the ostensible differences in rhetoric may in fact lie in company culture, and to some extent even in marketing.
BlackBerry is the mobile phone brand most commonly associated with governments due to its reputation for security. To cite some of BlackBerry’s own figures, 16 of the G20 governments use BlackBerry and BlackBerry has received over 70 security certificates.
This is not to say that Apple is not trusted or used by governments and enterprises, but Apple has a very different brand image if the customer bases now overlap somewhat.
Dating back to the famous ‘1984’ advert introducing the Macintosh computer, Apple’s brand has been built on the idea of individual freedom. While its stand in this case can hardly be characterised as a frivolous act of rebellion, Apple’s customers are primarily consumers.
BlackBerry’s primary customers, by contrast, are governments themselves and enterprises.
So while their rhetoric may differ, if the two companies are to be believed then neither is likely to jeopardise the security of their products to please any government.
In fact, in the same blog post, Chen said that the company has managed to achieve a balance between "doing what’s right, such as helping to apprehend criminals, and preventing government abuse of invading citizen’s privacy."
In a case with some parallels to Apple vs FBI, BlackBerry recently came close to pulling out of Pakistan after the government there demanded access to the content of customers’ BES traffic and to BES servers.
What the Apple case really shows, though, is how hard Chen’s concept of a "balance" is to realise in a world where privacy boundaries in technology are still being defined.







