World leaders will gather in Davos in Switzerland from 20th-23rd January and top of the agenda will be the digital technology driven Fourth Industrial Revolution.
This week the World Economic Forum released its 11th Global Risk Report (see link below for full report) with cyber security rising in importance for companies and countries.
Cascading Cyber Risks
Many hope that emerging technologies will fuel a new wave of productivity and growth. The pace of innovation is increasing and the spread of technologies is inevitable, giving rise to individual innovations and disrupting business models, processes and products in ways that will require rapid adaptation.
Mobile internet, automation of knowledge work, the Internet of Things and cloud technology will be the most disruptive and generate the most economic benefit.
The failure to understand and address risks related to technology, primarily the systemic cascading effects of cyber risks or the breakdown of critical information infrastructure, could have far-reaching consequences for national economies, economic sectors and global enterprises.
By one estimate, European countries that do not react appropriately to technological change could lose 600 billion euros in value added over the next 10 years, corresponding to about 10% of Europe’s industrial base.
Businesses, policy-makers and civil society therefore need to find appropriate frameworks to address four high-level risks associated with the transformation towards a more digitized economy.
Cyber dependencies
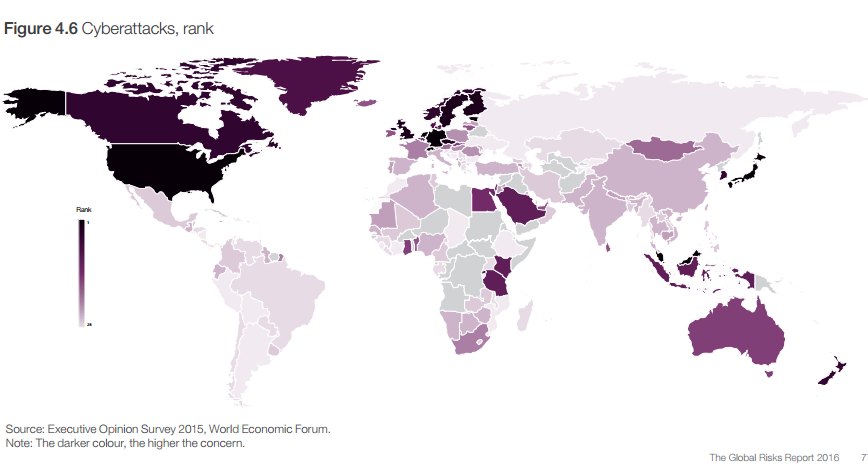
Cyberattacks and related incidents have been entering the global risks landscape as among the most likely and most potentially impactful risks for the past two to three years – in North America, cyberattacks ranks as the most likely risk by far.
Cases have been rising in both frequency and scale. They have so far been isolated, concerning mostly a single entity or country, but as the Internet of Things leads to more connections between people and machines, cyber dependency – considered by survey respondents as the third most important global trend will increase, raising the odds of a cyberattack with potential cascading effects across the cyber ecosystem.
As a result, an entity’s risk is increasingly tied to that of other entities. As cyber dependence rises, the resulting interconnectivity and interdependence can diminish the ability of organizations to fully protect their entire enterprise. As more organizations move to digitize their unique business value within more connected environments that rely more and more on machine learning and automated decision-making, cyber resilience takes on a new importance.
Investment priorities
Although organizations may recognize the benefit of cyber technologies for their bottom lines, they may not be fully internalizing cyber security risks and making the appropriate level of investment to enhance operational risk management and strengthen organizational resilience.
Particular attention is needed in two areas that are so far under-protected: mobile internet and machine-to-machine connections. It is vital to integrate physical and cyber management, strengthen resilience leadership and organizational and business processes, and leverage supporting technologies. Second: the exchange of data between countries and stakeholders.
Data have been called "the oil of the 21 century", and a predictable legal framework is needed to realize the full economic potential of digitization. Recent cases of policy reversal have created uncertainty about the legal situation, which can hamper investment and adaptation of the latest technologies. Given the inherent international nature of data flows, in areas such as supply chains or 3D printing, national governance needs to be complemented by a functioning international legal framework.
However, the current regulatory regime is underdeveloped and lacks the necessary legal certainty in areas such as privacy, transparency, encryption control, the effect of intellectual property regimes on data that cross borders, and the impact of proprietary data on competition. Given the many actors and industries involved and the competing interests at stake, stakeholders will probably struggle to find common agreement. Moreover, the physical infrastructure for data exchange, such as undersea cables, could also become a target in international conflict or terrorism.
Cross border cyber concerns
Cyberattacks are of high concern in Estonia, Germany, the Netherlands and Switzerland. Given the cross-border nature of cyberspace, there is obvious potential for cyberattacks to have ramifications well beyond the countries in which they occur.
In North America, which includes the United States and Canada, two risks have been selected as being among the five of highest concern for doing business in both countries: cyberattacks and asset bubbles. In the United States, the top risk is cyberattack, followed by data fraud or theft (the latter is in 7th position in Canada,
The risks related to the internet and cyber dependency are considered to be of highest concern for doing business, following recent important attacks on businesses. The United States is extremely well connected, and ICT usage is high – 87% of the population use the internet,13 and the country ranks second globally for online business-to-consumer transactions.
The risk of terrorist attacks is third on the list (and 13th in Canada): according to the House Committee on Homeland Security, the home-grown Islamist extremist threat in the United States has escalated dramatically in 2015, with more terror cases than in any full year since September 11, 2011.15
New Cyberattack vulnerabilities for businesses
From personal finances to business operations and national infrastructure, public and private services and amenities are increasingly managed via some form of computer network and are consequently vulnerable to attack.
The Internet of Things is a growing reality, introducing new efficiencies as well as new vulnerabilities and interconnected consequences. Recent technological advances have been beneficial in many respects, but have also opened the door to a growing wave of cyberattacks – including economic espionage, cybercrime, and even state-sponsored exploits – that are increasingly perpetrated against businesses.
In 2014, The Center for Strategic and International Studies and McAfee estimated that cybercrime alone cost the global economy US$ 445 billion.56 Businesses in all industries and of all sizes have been affected by the increased complexity, novelty and persistence of cyberattacks, with consequences ranging from the reputational to economic and legal. A sharp increase in high-profile cases in 2014 has continued into 2015, and shows no sign of slowing down.
The EOS results indicate that cyberattack is perceived as the risk of highest concern in eight economies: Estonia, Germany, Japan, Malaysia, the Netherlands, Singapore, Switzerland, and the United States. Public sector bodies in at least two of these countries have recently been disrupted by cyberattacks: the US Office of Personnel Management and the Japanese Pension Service. The 2015 Fortune 500 CEO survey found that cyber security came second when CEOs were asked about their companies’ biggest challenges.57 Attempts to detect and address attacks are made harder by their constantly evolving nature, as perpetrators quickly find new ways of executing them.
Businesses trying to match this speed in their development of prevention and response methods are sometimes constrained by a poor understanding of the risk, a lack of technical talent, and inadequate security capabilities.
Ownership of cyber risk within business
Although CEOs worry about rising cyber risks, the ownership of and responsibility for the cyber risk is less clear. Who in the corporation is the actual owner of the risk? While there are many "C" level owners (CISO, CFO, CEO, CRO, Risk Management), each of these owners has differing but related interests and unfortunately often does not integrate risk or effectively collaborate on its management. Defining clear roles and responsibilities for cyber risk is crucial. Outdated laws and regulations inhibit governments’ ability to capture criminals but also to expedite the often lengthy procedure of elaborating and implementing legal and regulatory frameworks to reflect evolving realities.
The sophisticated threats of government-sponsored economic espionage also exceed the defensive capabilities of many commercial enterprises, which are more and more frequently looking to other governments to intervene.
The G-20 recently took an unexpected, but applauded, step and collectively affirmed "that no country should conduct or support ICT-enabled theft of intellectual property, including trade secrets or other confidential business information, with the intent of providing competitive advantages to companies or commercial sectors."
Prevention and mitigation
Businesses are increasingly accepting the fact that they cannot hope to prevent all cyberattacks.
The difficulty in preventing attacks is not outmatched by the difficulty in identifying and effectively mitigating them. Given the types of vulnerabilities utilized by attackers and their methods, many attacks and intrusions are not immediately discovered – some are recognized only months and in some cases years later.
The emphasis needs to be on streamlining mechanisms for early detection, response and recovery, to mitigate and better manage the consequences – limiting the damage, and ensuring business continuity. It is also becoming clearer that cybercrime cannot be fought unilaterally.
Although businesses can follow standard industry practices or adopt individually tailored ways to deal with cybercrimes, cooperation throughout the value chain (because attacks can be made through supplier systems) and with law enforcement is also helpful, As is often the case, however, public-private partnership can be held back by lack of trust and misaligned incentives.
Businesses may fear exposing their data and practices to competitors or to law enforcement agencies. And the private sector’s primary interest in rapid recovery and continuity of business operations may not align with the public sector’s primary interest in apprehending and prosecuting perpetrators. In addition, governments need to balance their investments in cyber offensive weapons and efforts to enhance capabilities for cybersecurity and defence.
Conclusions
Addressing global risks lies beyond the capacity of individual businesses. Businesses need to strengthen their resilience to ensure continued operation and survival in the face of risks. At the same time, the clear role for collaboration among public and private sector actors becomes evident, for example, to develop better cybercrime prevention methods, to establish cybersecurity norms for both governments and industry, and to align international approaches to enforcement and establish industry norms.
Above all, it is in the key interest of businesses to find new ways to partner with governments to address global risks. Many risks, ranging from energy security to unemployment, can only be addressed through diverse stakeholders recognizing the need for joint action. Such collaboration requires the identification of key risks and related interests and strong alignment and robust agreement among business and other stakeholders.
Advice for Business Leaders on how to react to a crisis
1. Clarify roles and responsibilities. During a crisis, it is critical to have clearly delineated and understood senior official and c-suite executive roles and responsibilities for risk and incident management. Confusion around "who is in charge" or "who has authority" wastes crucial time and resources, and makes response and recovery less efficient and effective. The need for well-defined roles becomes heightened when an organization faces novel or rapid-onset disasters or emergencies, such as those resulting from cyberattacks. Pre-determining, training and exercising roles, capabilities and plans helps to ensure an organization’s risk readiness.
The successful management of complex crises also requires a capacity for adaptability and flexibility. Crisis managers must be able to adjust pre-established plans as needed given the unique characteristics of the crisis.
2. Develop Crisis Leadership Characteristics. Organizations that successfully position for, respond to and recover from major events also consistently have effective leadership – the qualities and actions of those with authority and influence can empower their entities to be resilient. Such leaders are steady and decisive in the face of uncertainty and pressure.
They make decisions in a timely and prioritized way, and communicate them transparently. Recognizing that they cannot address risks alone, they galvanize others and are clear about what assistance they require. They understand when a disaster requires them to cut through policies that may prevent or delay action. Leaders who are effective during and after a crisis are those who have earned trust through their demonstration of openness, transparency, responsiveness and accountability.
They are seen as honest and standing up against corruption. For example, an IMF assessment attributes much of Chile’s effective recovery from the 2010 earthquake to the nation’s "technocratic, rules-based, and transparent" leadership – and to its institutional practices, including the rule of law.
Another example is seen in Norwegian Prime Minister Jens Stoltenberg’s speech in the wake of the July 2011 terrorist attacks in Norway, which demonstrated how leadership during a crisis can significantly result in both increased trust in government and meet citizens’ expectations of responsiveness. These examples also highlight the role of meaning making – that is, the capacity for leaders to make sense of an adverse event and articulate to the public a clear path forward in a state of emergency.
3. Leverage expertise. When confronted with an unprecedented emergency, strategic crisis managers must be able to quickly identify and mobilize the most relevant and trustworthy expertise to help understand and respond to the crisis.
Knowledge management systems and expert networks need to be set up in advance and across multiple sectoral, professional and disciplinary boundaries. Understanding the implications of the crisis beyond the immediate consequences and anticipating the potential pathways of cascading effects requires appropriate crisis management structures that enable additional expertise to formally support decision-making.
For example, the United Kingdom’s Scientific Advisory Group in Emergency (SAGE) is an independent support group that provides science-based expertise for the management of complex and unprecedented crises to the UK cabinet. Access to such expert "force-multipliers" could help both public and private entities understand and address the unique aspects of a crisis. Having access to specialized expertise is especially crucial for novel or multi-faceted evolving crises – such as the Great East Japan Earthquake, which impacted the Fukushima nuclear reactor and caused many companies to struggle with what decisions to make.
4. Create a culture of integrated risk management and multi-stakeholder partnerships.
Another necessary institutional value is the recognition of the scope of global risks and the need for partnerships to address them.
A culture of risk management – the beliefs, norms and values that underpin daily actions – must span the whole organization, including its supply chains. Entities can no longer afford to have different types of risks managed by different policies and operating procedures and by different officials, executives and agencies.
All parts of an organization must collaborate transparently on risk management through integrated planning because of the potential for risks to have cascading consequences, including spillovers between the virtual and physical realms – for example, a flood disabling a server farm, or a cyberattack interrupting electricity supply.
These are edited extracts from The Global Risk Report 2016 issued by the World Economic Forum. Read the full report.






