
A nagging fear exists within the public cloud that it is less secure than either private or on-premises, a fear that Microsoft hopes to dispel.
Azure Confidential Computing, a new service from Microsoft that’s currently in early access testing, aims to protect cloud data as it is in use through encryption.
The idea being that data can be processed in the cloud but remain under control of the customer.
Everyone is targeting greater cloud security
Hybrid Cloud Security and How to Do It Right
It’s not just cloud Microsoft wants to dominate, it’s AI as well
Microsoft CTO for Azure, Mark Russinovich said on the company’s site that the Azure team, along with Microsoft Research, Intel, Windows, and its Developer Tools Group had been working on the software and hardware technologies for the Azure Confidential Computing products for over four years.
Obviously, Microsoft is hoping to make its cloud look even more secure so that customers will be more willing to throw their data into it, the company highlights customer reluctance to move sensitive data to the cloud for fear of attacks against their data when it is in-use. 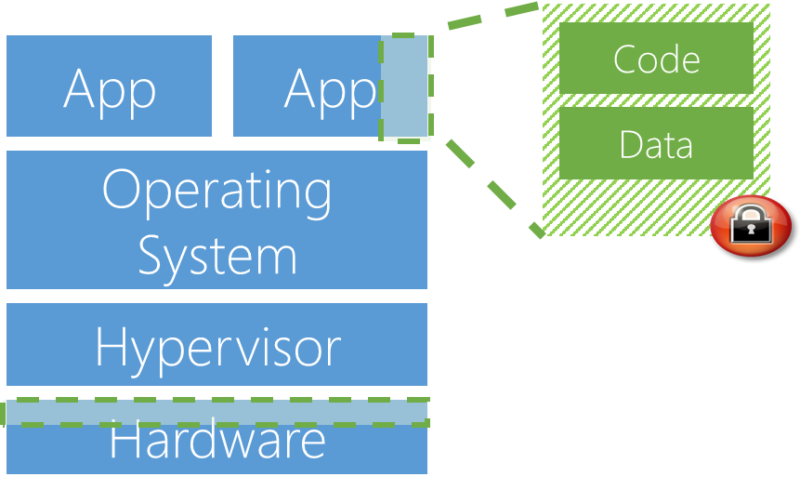
The solution, in Microsoft’s eyes, is being able to move data to Azure but ensure its security by protecting from things like malicious insiders, hackers and malware, and third parties accessing it without consent.
Russinovich said: “Confidential computing ensures that when data is “in the clear,” which is required for efficient processing, the data is protected inside a Trusted Execution Environment (TEE – also known as an enclave), an example of which is shown in the figure below.
“TEEs ensure there is no way to view data or the operations inside from the outside, even with a debugger. They even ensure that only authorized code is permitted to access data. If the code is altered or tampered, the operations are denied and the environment disabled. The TEE enforces these protections throughout the execution of code within it.”
For more information on Microsoft’s security update head here.






