NETSCOUT
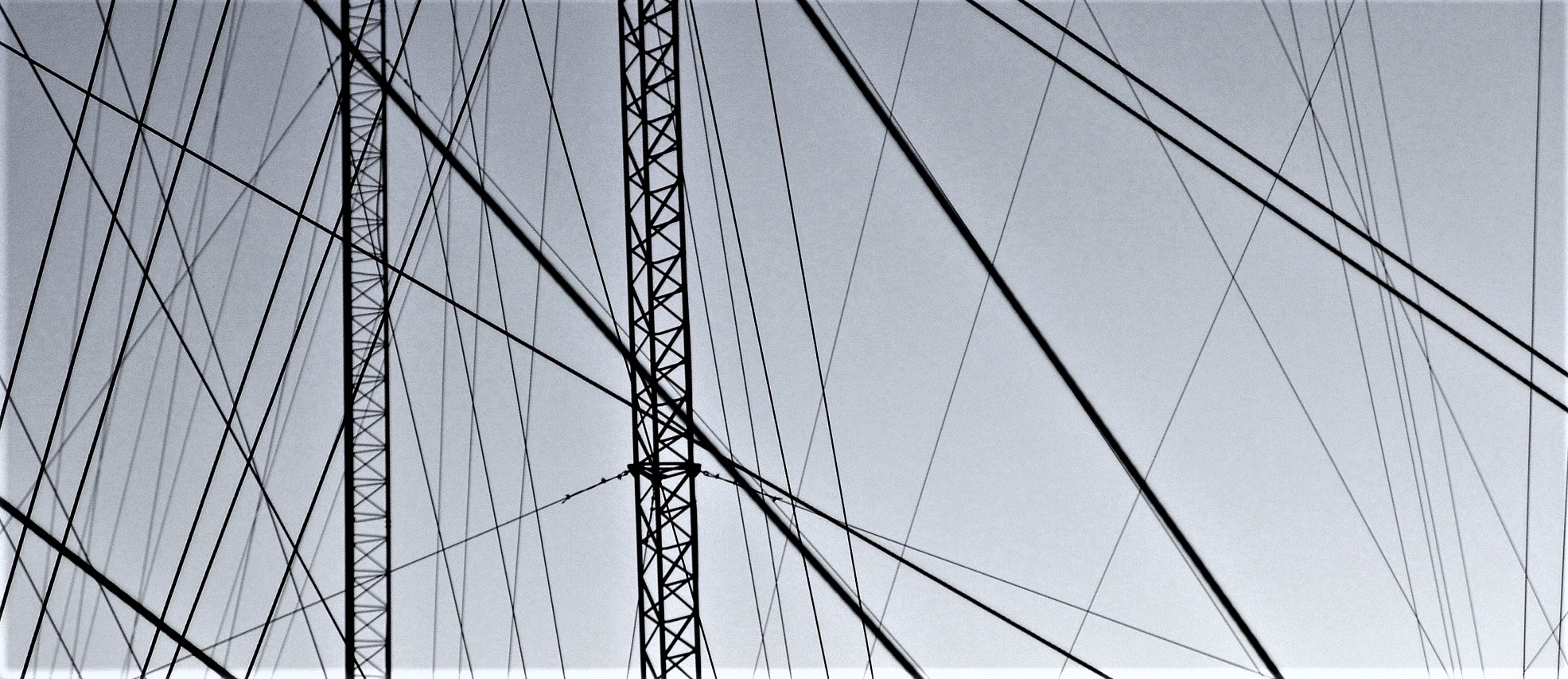
Hackers Feast on Exotic DDoS Threat Vectors, as Botnet “Buffet” Gets Ever Larger
Approximately 7.7 million new internet-connected devices are coming online everyday, and their typical insecurity means it's an "eat all you…
Smart Data and Visibility for Greater Application Security: The DevSecOps Opportunity
Today’s application-driven economy has fuelled an uptake of DevOps practices; today, more than a quarter of average IT departments will…
How Local Governments can Unlock the Power of the Cloud
With the cloud rapidly becoming a significant part of organisations’ innovation initiatives, it is little wonder that 85 percent of…
IBM Agrees to Bundle Network Analytics Tools with NETSCOUT
IBM has teamed up with NETSCOUT to integrate the latter’s network analytics tools into its telecommunications analytics suite. The move…
Tackling Hybrid Network Security Challenges
The Network Security Evolution Over the years, security threats have evolved from being singular attacks to being a complex combination…
Are you still buying custom hardware for your Packet Brokers?
Can you guess the answer to this series of facts: what saved Facebook $2 billion, ditto for Apple, cut Fidelity…