DDoS
Taiwan Presidential Office website hit by ‘overseas’ DDoS attack
The website of Taiwan's Presidential Office was hit by an "overseas DDoS attack" earlier today, according to reports, with traffic…
Port of London Authority hit by ‘politically motivated’ cyberattack
The Port of London Authority (PLA) fell victim to a cyberattack last night which has knocked its website offline. The…
XorDdos malware is targeting Linux and putting millions of devices at risk
Hackers are increasingly deploying the XorDdos malware to infiltrate Linux systems and launch distributed denial of service (DDoS) attacks, with…
Romania DDoS attack shows Ukraine allies are in Russia’s crosshairs
Government websites in Romania have been crippled by a distributed denial of service (DDoS) cyber attack carried out by Russia-supporting…
European NGO Specialising in “Disinformation” Analysis Knocked Offline in Cyber Attack
Non-profit organisation the EU Disinfo Lab has had its website knocked offline for the bulk of today in an apparent…
T-Mobile Outage Whipped Conspiracy Theorists Into a Frenzy — Here’s What Really Happened
A widespread T-Mobile outage across the carrier's US network on Monday triggered a frenzied firestorm of conspiracy theories, amid unverified…
AWS Hit With a Record 2.3 Tbps DDoS Attack
AWS says it was hit with a record DDoS attack of 2.3 Tbps earlier this year, with the (unsuccessful) attempt…
AWS Hit by DDoS Attack – Google Cloud Issues Unrelated
Updated with Google comment 23/10/2019: 20:02 BST AWS late yesterday was hit by a sustained DDoS attack, which appears to…
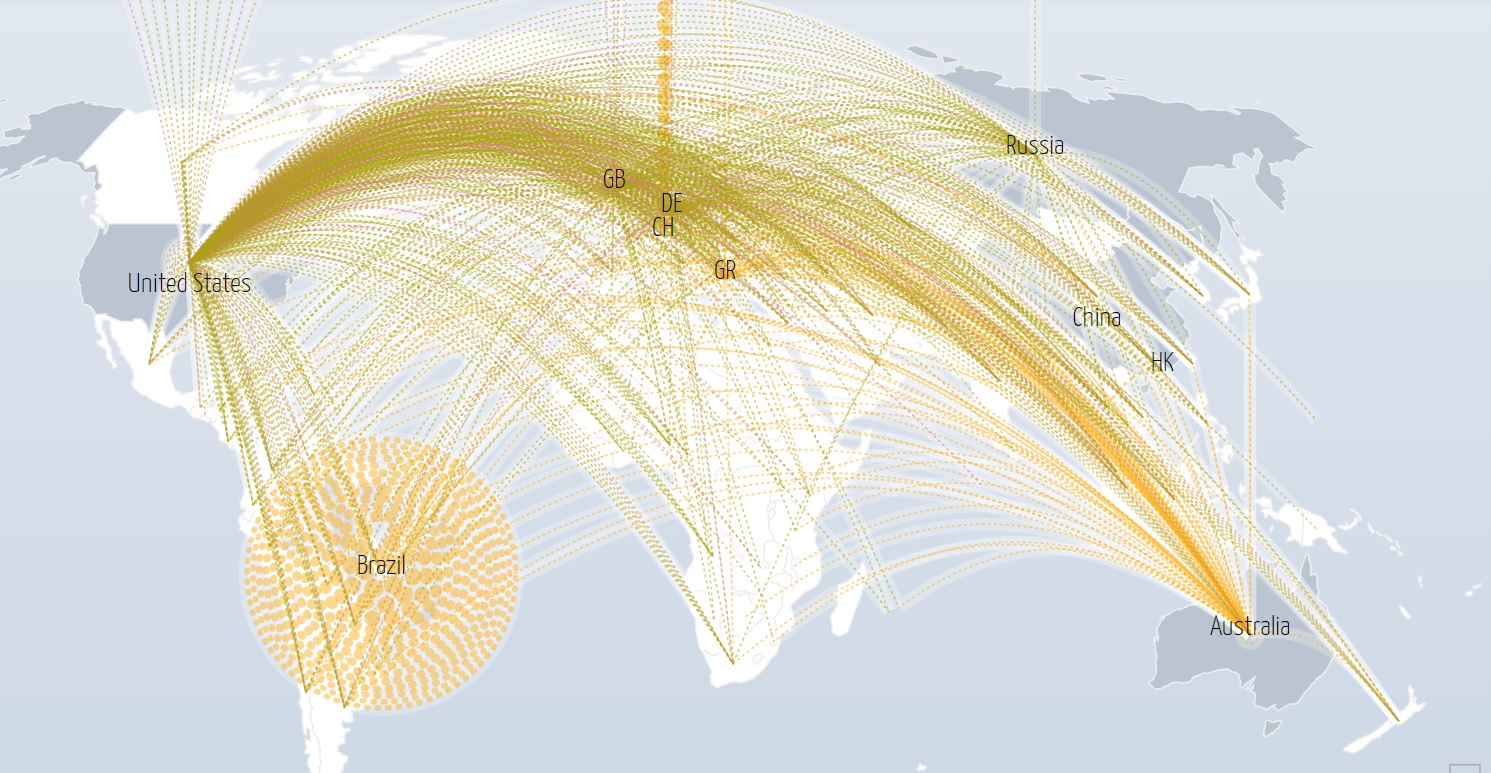
Hackers Feast on Exotic DDoS Threat Vectors, as Botnet “Buffet” Gets Ever Larger
Approximately 7.7 million new internet-connected devices are coming online everyday, and their typical insecurity means it's an "eat all you…
UK Police Conduct Fresh Wave of DDoS Raids
British police are conducting a number of live operations against users of the Distributed Denial of Service (DDoS) marketplace webstresser.org,…