Despite the massive disruption it seems likely that the initial attacks have not resulted in a big pay day for the bad guys.
But it also creates opportunities to get the right messages to staff in order to protect organisations against similar malware threats. At the time of writing it is not clear whether a phishing email or direct exploit of an unpatched vulnerability was to blame for the rapid spread of WannaCry.
The chances are that attackers used mixture of both. Either way staff need to understand the dangers of improved phishing emails which will be carefully tailored and can appear almost identical to a real message from a named colleague.
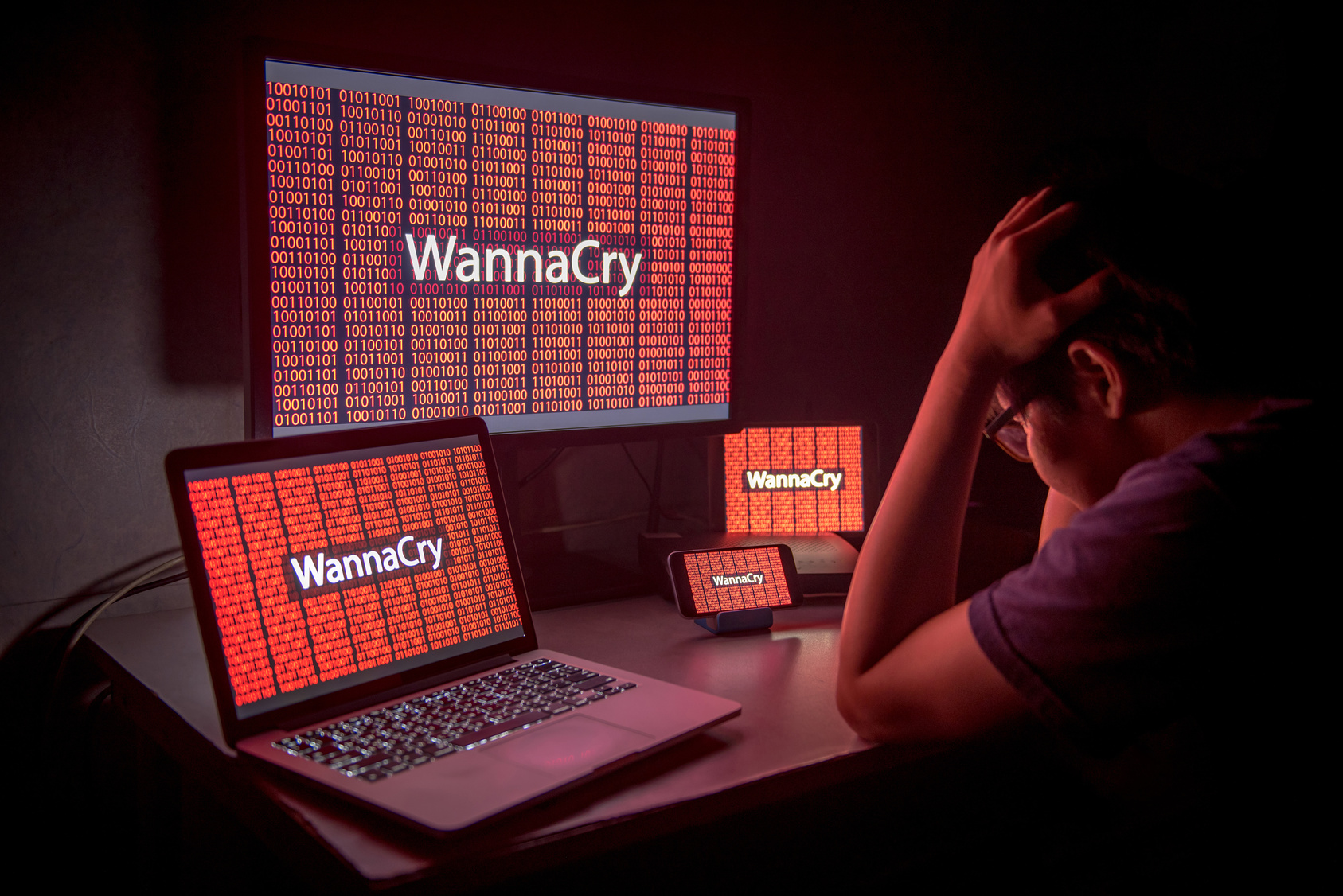
With victims in 150 countries including Telefonica in Spain and FedEx in the United States it is clear that even well prepared companies can fall to an organised attack.
There are several other lessons for enterprise technology teams.
Firstly WannaCry is a reminder of how important patching is.
Delaying the application of patches must be seen as a business risk. There are good reasons for not instantly applying them – testing bespoke software and the danger of other unknown problems – but these risks must be balanced against the real risk of leaving vulnerabilities in place. Ransomware exploits known vulnerabilities – and WannaCry was no exception.
Secondly this attack can be a good time to revisit email policies and who is allowed to run executables and macros. This needs to be done sensitively so that people can continue to do their jobs and don’t resort to ‘working around’ IT rules.
Thirdly don’t ignore other possible attack vectors like unrestricted web browsing but also use of storage devices and other removable media. Attackers can still use DVDs and USB sticks to get malware onto your network.
Finally WannaCry is a good time to think about what happens if you do become a victim. It provides a chance to get cyber security and recovery processes to the top of the corporate agenda.
Proper access controls within your network can hugely reduce the impact of a successful attack. Looking at just which systems, and which users, can access which parts of the network can be an affordable way to quickly improve overall security.
Making sure that back-up systems are properly protected and isolated and ready and capable of getting systems back online in a timely fashion is also vital.
At the time of writing it seems like WannaCry was stopped in its tracks thanks to the fast thinking of a young security researcher.
He spotted that the malware was sending a message to a web address which wasn’t registered. By registering that domain he was able to stop WannaCry encrypting systems.
He’s written a more technical explanation here: https://www.malwaretech.com/2017/05/how-to-accidentally-stop-a-global-cyber-attacks.html
This incident should also force governments to behave differently. WannaCry used a vulnerability which was spotted by intelligence agencies some time ago. But they did not warn the software providers to fix the problem.
Even worse the details of the problem then leaked so that cyber criminals could use it to make money.
WannaCry might be the final straw to get these agencies to work to improve cyber security for businesses rather than weaken it.
Regardless of the final fallout from WannaCry it is a warning that this threat will not go away. There will more attacks and they will keep getting smarter and better.
Defending them will not get easier but properly using the tools already available will make life more difficult for the bad guys and give your organisation the best chance of recovering fast if you do become a victim.






