It also turned out not to be traditional ransomware either.
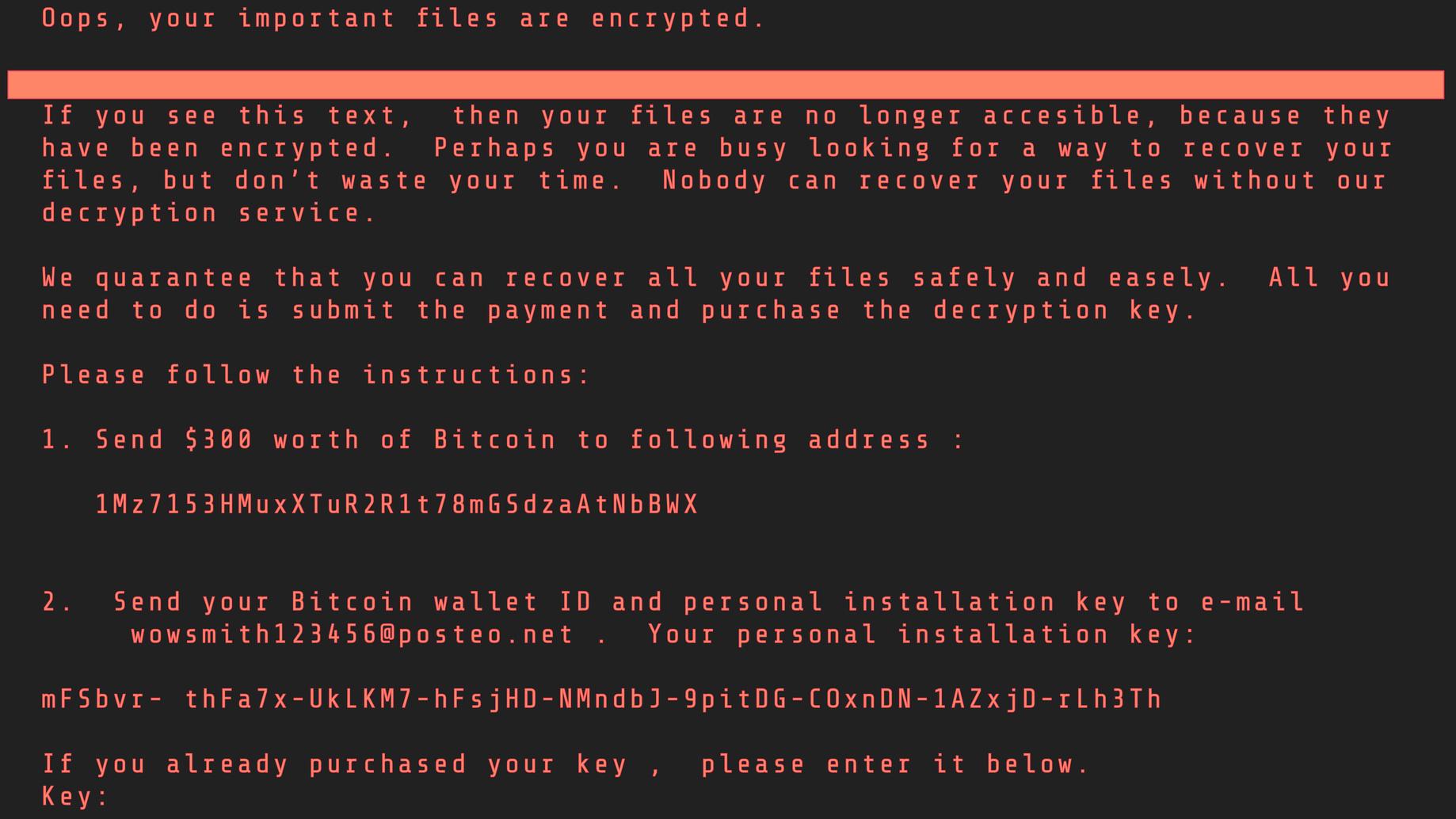
Although the software, after encrypting file indexes and individual files asked for a ransom in bitcoins, the crooks asked for the money to be sent to an email address, which was quickly shut down by the provider.
Normal practise is to provide an individual code to identify victims’ systems so they could be fixed and to send the money direct to various bitcoin wallets. This meant that even though the malware hit hundreds of victims the criminals only made a few thousand dollars.
Tying each victim to one bitcoin address allows crooks to ensure they’re paid, and encourages victims to think their systems will be decrypted if they pay the ransom.
NotPetya hit networks in Russia and Ukraine but did hit some companies in the UK, Germany and Australia too.
NotPetya used EternalBlue which was identified and kept secret by US security services. It was then stolen from the spooks and is now being sold to cyber-criminals. The vulnerability was also used by the WannaCry ransomware which hit far more organisations across the world.
Even though WannaCry spread further the NotPetya ransomware was in some ways a more sophisticated attack.
It spread horizontally across the infected network rather than trying to spread to other networks. As well as sending itself on the malware also checked infected machines for administrator rights and log-in credentials so that it could take control of other machines on the same network.
These key differences – its poor method of securing the ransoms, and a tendency to do deep damage locally instead of spreading far and wide – have led researchers to blame a politically-motivated attack on Ukraine instead of cyber crooks trying to make money.
Microsoft analysts estimate that 70 per cent of infected systems were inside Ukraine.
Ukrainian security services, backed up by several malware analysts, have been quick to blame Russia and said infrastructure and power systems were particularly targeted.
But whatever the motives the malware still managed, even if accidentally, to do damage to systems outside of Ukraine and there are still important lessons to be learnt for enterprise cyber security.
First of all while WannaCry relied on unpatched systems NotPetya could also hit companies running up-to-date and properly patched software.
The original way into systems was via updates to a tax payment service commonly used in Ukraine although some phishing emails were also used.
The malware clearly demonstrated the importance of restricting admin privileges rather than handing them out to users who do not need them. The malware searched infected systems for common admin tools which it could then take over.
One simple way to do this is by ‘leasing’ privileges – people who need them can only have access to admin rights for a limited amount of time before reverting to normal user status.
The attack also highlighted the need for firms to look at other forms of security like endpoint monitoring, network zoning and security intelligence platforms.
But the lesson for any organisation is that the threat from ransomware is real and is getting ever more sophisticated.
Attacks no longer rely on users clicking on email attachments or downloading dodgy software from the internet.
We also know that the bad guys now have a stockpile of vulnerabilities which they will likely use to power new attacks.
The hacker group ShadowBrokers – which made the original EternalBlue exploit available – has already released a dump of other NSA vulnerabilities for sale.
Although both WannaCry and NotPetya have not done a good job of making money for crooks they both showed how vulnerable government and business systems are to this type of attack.
The next generation of malware is likely to be better than WannaCry and NotPetya which both had glaring flaws which allowed organisations to defend themselves quite easily.
But organisations can still defend themselves against even the most sophisticated attack.
Firstly even if it does not guarantee safety it is vital that every part of your infrastructure is running up-to-date and fully patched systems. Think carefully about running any part of your infrastructure on software which is no longer supported. If you absolutely have to use outdated software to run specific machines consider how you can isolate them from the rest of your infrastructure.
Trained staff who are not afraid to blow the whistle if they suspect something is going wrong can also help protect systems.
Automated and intelligent cyber security is important too as is staying up-to-date with the latest types of attack.
But however good your defences the expert advice is still to assume that an attack will get through eventually.
So just as important as defence is properly planning what happens when your organisation is hit by a successful ransomware attack.
This means making sure your systems are properly and frequently backed up. Consider just how long it would take you to get systems, and data, back up and running from those systems.
That means you have to practise doing it – restoring everything from back-ups and not just assume everything will work.
Beyond back-up you also need to practise your ‘incident response plan’.
Consider who will be involved and how they will communicate. Think also about partner companies which can help you but also what impact your failure would have on the rest of your supply chain. Equally you need to talk to those partners about how prepared they are if they get hit.
Consider also if you need to talk to regulators or law enforcement.
Security experts say that organisations with well drilled response plans can hugely reduce the damage and downtime caused by successful attacks.
Assuming you have systems in place which quickly alert you to an attack the first few minutes, or even hours, after an attack are hugely important.
Make sure systems are responsive enough to effectively run what will be a very fast moving situation.
But your systems should also provide a record of exactly how the incident unravels. This will allow you to further improve defences and your response to the next incident.
This sort of attack is not going away and although defences will continue to improve it seems unlikely that a magic bullet will be found any time soon.
Making sure you have both the systems, processes and people in place to deal with the inevitable attack will make a big difference to the damage the hackers can do.






