Introducing the Wire Messenger
Nobody wants their emails leaking. It’s personally embarrassing and if you’re a business – humans being what they are – likely to result in reputational risk that registers on the Richter scale.
Despite this, email – a system of communication built with zero privacy at its heart – still dominates business communications, even in a post-Snowden, hack-happy era in which few secrets are sacred.
If Wire CEO Morten Brøgger has his way however, not for much longer.
As chief executive of the privately held company – backed by Skype veteran Janus Friis’s venture capital fund Iconical – he is gunning hard for a piece of the secure enterprise communications market.
He told Computer Business Review: “Email has peaked. The email stack was not written with security in mind. Security is written on top of it and is often clunky to use.”
He adds: “Business email users also get a lot of emails they don’t want and moreover the generation coming through simply don’t use email. I live in the US and my children in Copenhagen. If I send an email I’m not going to get a reply; it’s just not what they’d use.”
Not Yet Profitable, but Growing Fast
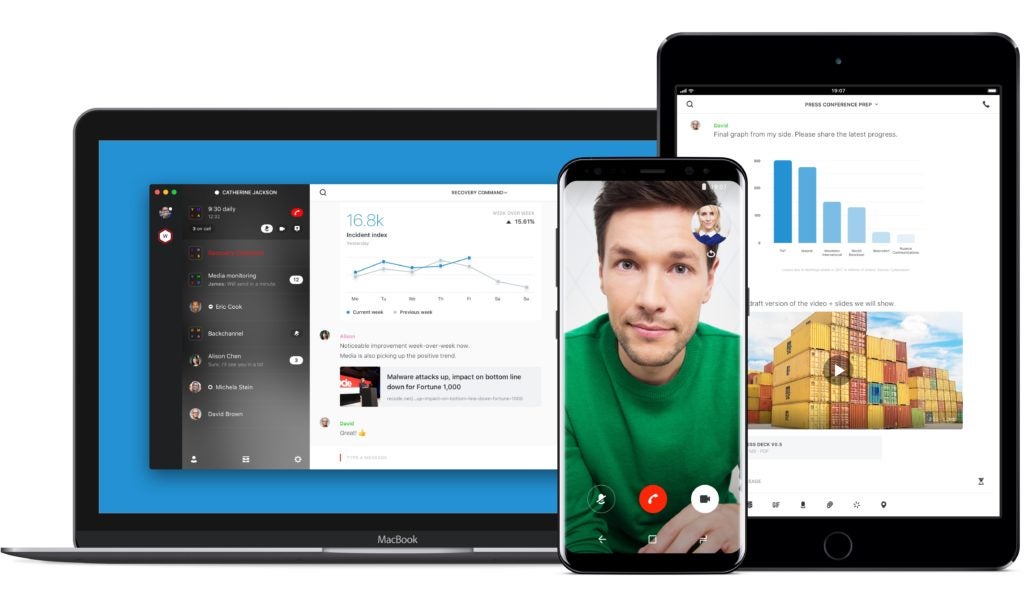
Wire can be used for group/team messaging as well as one-to-one. It regularly adds new features; most recently including a “secure guest rooms” feature. The platform works across Android and iOS apps, as well as desktop.
After some initial teething problems it is now growing at what the former telecoms executive says is “five to seven percent each week” – although he admits it is some years from profitability.
So what is Wire, how secure is it – and what are Brøgger’s plans?
Distributed Encryption Architecture
The collaboration platform uses a distributed encryption architecture.
Each entity/device has its own encryption key that gets updated with each message, whether that is a text, file share or conference call, using Proteus, an implementation of the axolotl protocol (Double Ratchet algorithm) without header keys.
The idea is ephemerality: as Brøgger puts in in a call with Computer Business Review: “Each message is a fortress. Imagine taking the time to crack something and all you get is a single message saying ‘are we on for next week’? After that, the key has reset.”
He adds: “All the security is distributed onto the devices. The encryption keys only exists on the devices of our customers. We don’t have a copy and can’t look over shoulders. If we get hacked, people can’t see anything.”
(Wire’s independent implementation of the Open Whisper System-developed Double Ratchet, written by Brøgger’s team in Rust, was not without its hiccups. As a May 2016 blog by Wire CTO Alan Duric reveals, it resulted in a legal dispute with Open Whisper’s Moxie Marlinspike that was ultimately settled out of court; all now in the past).
Can We Audit That?

The information security world is one that is red in tooth and claw; vulnerabilities are pounced on mercilessly and reputations can be trashed fast.
Wire has tried to gainsay any critics by ratcheting up its transparency: all of its code is now open source and available on GitHub – and the company is admirably honest about any bugs. Every year it hires an independent security consultancy to audit its code then publishes the unexpurgated findings within five days
“We want to drive a change in the communication industry where regular security audits become not only the best practice but a new norm. It is not good enough to advertise audits from years ago when the whole code base of your product has changed. It is also not good enough to publish glossy executive summaries of non-public security audits of solutions that are not even open source”, the company says.
(The most recent, by Kudelski Security and X41, available for Android Client, iOS Client and Web, Calling found two high severity vulnerabilities and eight medium severity ones, all now fixed).
The Route to Profitability
Following a growing cascade of leaks and hacks, businesses are growing increasing concerned about protecting communications; whether internal or external and Brøgger told Computer Business Review that he was excited by the future.
“We now have couple of hundred government, non-profit and business customers and some very interesting customers reaching out to us, including some top ten pharmaceutical companies, top five private banks and large government institutions with hundreds of users.”
The company does not run adverts and aims to make money through subscriptions, which are priced at as little as €4 per month.
The focus, beyond raising visibility, is on new features and call quality. Users of encrypted messengers will know that reliability can be patchy and Brøgger is frank about where and when this happens.
He told Computer Business Review: “Each user on Wire can have up to eight devices. Each will have their own encryption key. Let’s say that there are 10 people on a conference call; and they have on average four devices connected to Wire, that’s 40 encryption keys and 40X encryption that happens on a conference call. If one is on a low bandwith connection, it can give issues.”
He adds: “That said, I use it myself regularly including from my car on networks in Denmark that are not always the best and reliability has been good. Any issues I shake my iPhone and it sends a log to our dev team immediately.”
The 65-strong team, based primarily in Berlin, look set to be kept on their toes as the company grows. So what’s the end-game? An IPO?
Brøgger is reluctant to answer but a fundamental honesty wins out: “We have a good pipeline of clients and are looking for more. At some point down the road there may be a new owner, perhaps a larger software company. The most likely exit is an M&A not an IPO. Whatever is fantastic for the company is the answer, but that’s not on the horizon right now.”
With that, he’s off on a plane to catch up in person with those email-ignoring but hopefully Wire-answering children.






