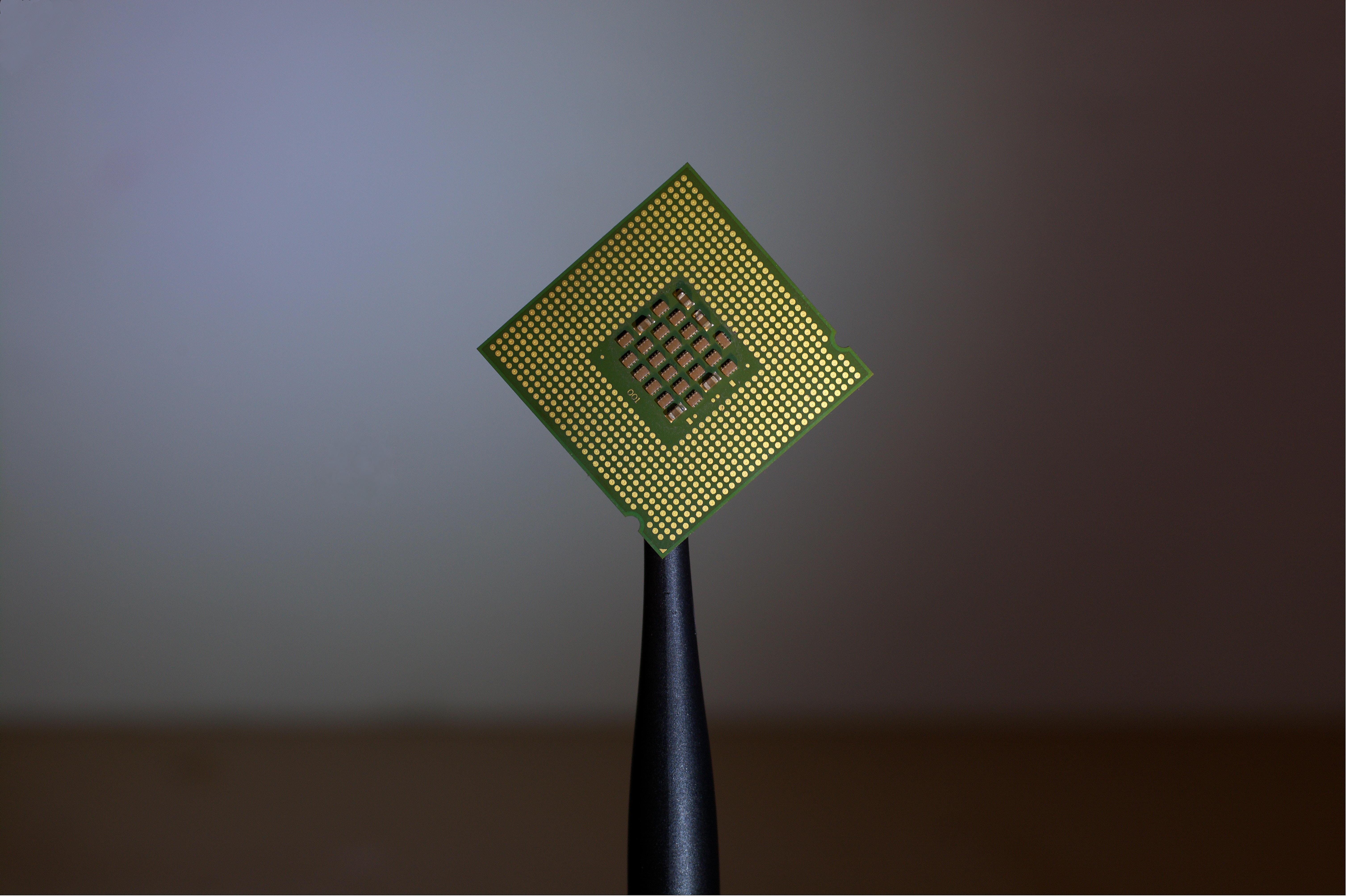
Semiconductor maker Rambus has released a new programmable chip that aims to “establish the trust chain” early in the silicon manufacturing process, amid widespread industry concerns about chip vulnerabilities.
The release comes after security flaws “Meltdown” and “Spectre” were independently disclosed by multiple security researchers, including Rambus’s then-chief scientist Paul Kocher and Mike Hamburg, in January 2018.
The two security flaws exploit critical vulnerabilities across a wide range of modern processors, including Intel, ARM and AMD. The vulnerability affects nearly every computer chip manufactured in the last 20 year. Critics have warned that – particularly amid a proliferation of connected devices – the vulnerability could prove catastrophic.
Rambus’ CryptoManager Root of Trust (CMRT) is built around a custom RISC-V CPU. The California-based company said its core creates a siloed architecture that isolates and secures the execution of sensitive code, processes and algorithms from the primary processor, allowing designers to “optimize the primary processor for high performance, low power, or other characteristics while optimizing security in the siloed core.”
Aimed at Cars, IOT
Rambus is particularly targeting Internet of Things (IoT) and automotive customers, the company said.
The chip is being released after automotive research consortium FASTR published a detailed framework for secure Over The Air (OTA) vehicle updates, that identifies a number of potential threats and attack vectors targeting OTA updates, including spoofing, tampering, repudiation, escalation of privileges, information leakage and DDoS attacks – these could result in seizing control of critical systems such as brakes or accelerators.
Rambus claims its CMRT can be “seamlessly” embedded in electronic control units, infotainment head-end/gateway processors, as well as advanced driver assistance systems (ADAS) and autonomous car chips.
Anti-Tamper Techniques
The company adds in a white paper: “The CMRT core utilizes advanced anti-tamper techniques to provide the highest level of security and protection against a wide range of attacks, including fault injection. These include logic and crypto redundancy, secure state encoding and ephemeral keys that are generated on-the-fly from multiple splits and flushed immediately after use. In addition, the CMRT core features an optional Entropic Array with a proprietary logic structure that provides robust protection against emulation and reverse engineering.”
IDC research director for IoT Security, Abhi Dugar, said in a release: “The semiconductor industry faced some of its biggest security issues this year with recent vulnerabilities, and the potential to encounter additional security flaws will not go away any time soon as more IoT devices enter the market. To address existing and new threats, establishing trust at the hardware level will be critical, and a secure siloed core can help ensure that this new generation of devices can be protected from security flaws.”
One hardware security expert, Scott Cadzow of Cadzow Communications Consulting, told Computer Business Review: “I read Rambus’s announcement and whilst I see it as a good step forward I’m a little wary. The vulnerabilities exploited by Spectre and Meltdown were design decisions and at the time of the decision no exploit was available and the performance gain from the decisions more than justified the design decision. However over time exploits became viable (i.e. Spectre and Meltdown) and whilst some countermeasures exist to limit the dangers from the exploits it is near impossible to assure those countermeasures are implemented before the exploit is launched.”
He added: “What Rambus have done it is a useful step forward and similar approaches have been available in the past with other forms of TPM. Over the long term attackers will look to exploit any platform and find weaknesses in the system. My gut feel is that Rambus’ breakthrough will mean attackers look away from the chip for the near future – you always exploit with the lowest cost of exploit first. So a good step forward for today but gives no long term guarantee of protection of assets as it is just one of many links in the protection chain.”






