We tend to think of cyber security as a software issue with a software solution: install antivirus or firewall software on your device and it can protect against the majority of threats out there.
However, this is ignoring hardware-based attacks, a type of cyber threat that security providers are taking increasingly seriously.
To some extent, this is because a lot of the work to combat hardware threats is happening under the hood. Providers of chips to the car industry, service providers and device manufacturers, as well as the banking and military industries, such as NXP, will build hardware security into the chips they sell.
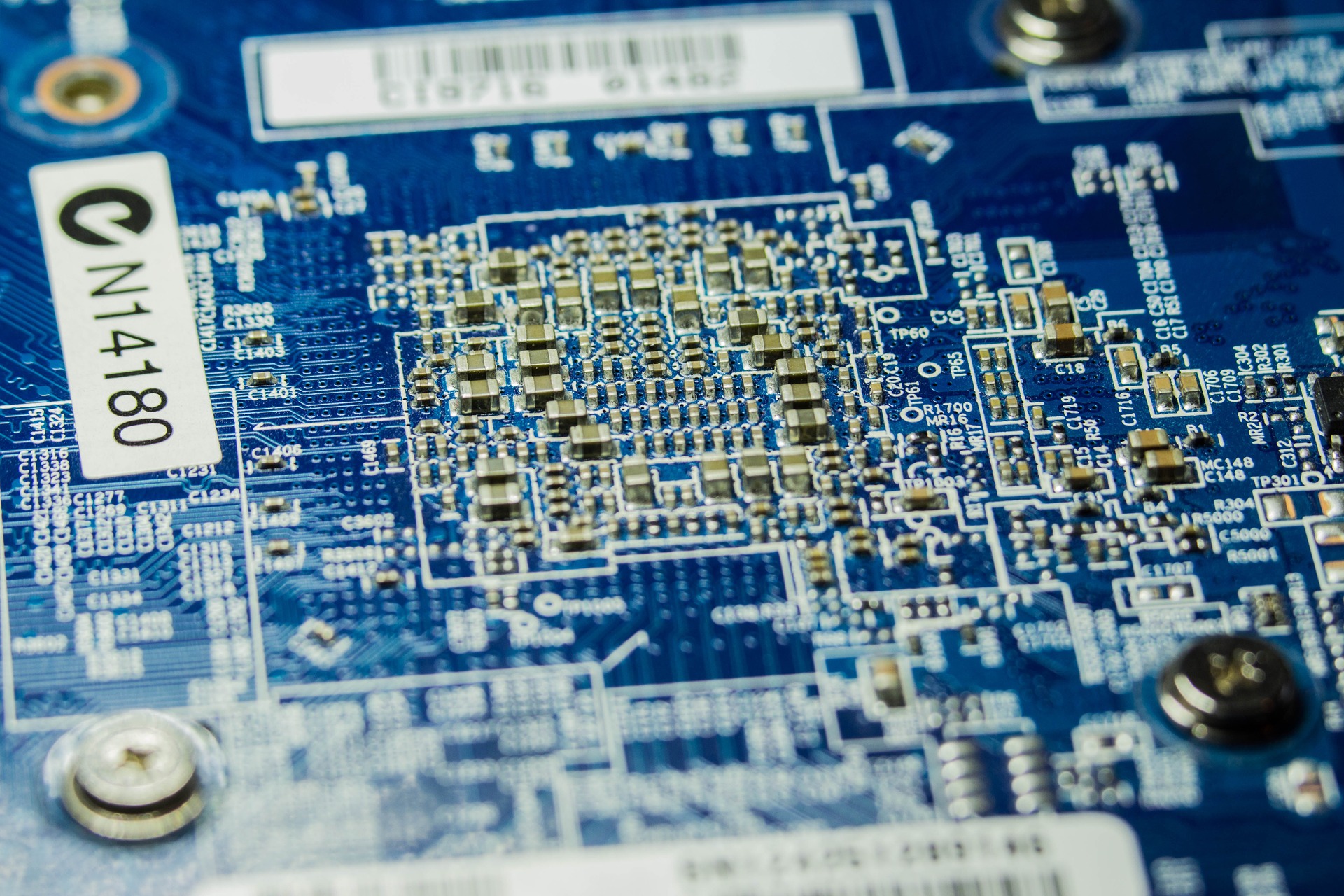
However, there are still plenty of unsecured chips out there, vulnerable to several major types of hardware attack.
These include side-channel attacks, which are techniques that allow attackers to monitor the analogue characteristics and interface connections and any electromagnetic radiation.
Differential power analysis (DPA) is a type of side-channel attack which measures the electrical power consumption or electromagnetic emissions from the device. From these measurements, attackers can derive cryptographic keys and private data.
These keys allow attackers to easily gain unauthorised access to a device, decrypt or forge messages, steal identities, clone devices, create unauthorised signatures and perform additional unauthorised transactions.
Another type of attack, fault generation, uses “abnormal environmental conditions to generate malfunctions in the system that provide additional access,” according to Cambridge professor Dr Sergei Skorobogatov’s paper Hardware Security of Semiconductor Chips: Progress and Lessons. This could include electrical glitches introduced to cause a chip to fail to execute a command.
According to Mathias Wagner, Security Fellow at NXP, this phenomenon also occurs naturally in space as a result of cosmic radiation, which means that trips into space have to have multiple computers to retain accuracy.
Reverse engineering, another type of attack allows attackers to deconstruct a chip to understand how the secure key works.
Some of these attacks are fairly basic, with the required equipment costing anywhere from £5000 to £40000, according to NXP’s Wagner. Much of the equipment is commercially available, he adds. For example, a DPA based attack would simply require an oscilloscope, which measures voltage.
He says that a device with an unsecured chip could be hacked using these techniques very quickly. If secured it could take much longer.
Unlike a software attack, a hardware-based attack requires a degree of proximity. This is why the danger of losing devices is such a big one.
The memory and storage company Crucial obtained figures revealing that almost two laptops per day are lost on the London Underground network, with 3,533 laptops reported lost in the last five years on the Transport for London rail network.
An additional 801 have gone missing in the last three years at eleven Network Rail operated stations across the UK.
Wagner says that hardware attacks could potentially work against a device such as an iPhone, although not against the secure elements themselves but rather against a microcontroller being used for an apps controller.
“If you use software on a standard microcontroller you are vulnerable to this kind of attack,” says Wagner.
For example, it is possible that a side-channel attack might have been used to hack into the phone of the iPhone of San Bernandino shooter.
In March, the FBI dropped a court battle against Apple after a third-party provided a means to hack into the killer of Syed Rizwan Farook. An unnamed third party was credited with providing the solution.
Experts interviewed by IEEE Spectrum in a feature on the hack acknowledged that a side-channel attack was a possibility.
So what are the ways of protecting against this kind of hack? As mentioned above, the use of secured chips such as NXP’s is one. The company’s chips are used in half of chips worldwide in the banking arena, for example.
Boeing has recently licensed Rampus DPA Countermeasures to protect its aerospace and defence systems from security threats.
This means that advanced DPA countermeasures will be included in Boeing products.
Rambus is also working with smartphone manufacturers. Rambus’ CryptoManager platform establishes a hardware-based root-of-trust, embedding a security core in the SoC itself. Vendors can therefore securely provision unique keys for each chip during the silicon manufacturing and testing process.
Whatever the chosen solution, this is an area that we can expect to attract more attention in cyber security in the future.






