As governments worldwide extend their control over the world wide web, illegal activity continues across the dark net beyond their knowledge and control.
Buried under layers of encryption and only accessible via dedicated browsers such as Tor, the dark net has both supporters and detractors. Supporters cite the importance of an anonymous and uncensored space, free from snooping by governments.
Critics cite the widespread criminal activity taking place, with a recent survey by Ipsos and the Centre for International Governance Innovation (CIGI) finding that 71 percent of citizens globally believe that the dark net should be shut down.
This criminal activity includes conventional criminality such as selling illegal services and items such as weapons or drugs.
It also includes cyber crime. Forums exist on the dark net where users can buy exploit kits and rent out the infrastructure required to carry out distributed denial of service (DDoS) attacks according to their desired specifications.
Cyber criminals sell on identities compiled from various pieces of information such as healthcare records, bank details, or sell access to back-end systems.
John P. Watters, Chairman and CEO of iSIGHT Partners, describes these forums as a "full-on Walmart" for cyber crime.
Regardless of whether one supports shutting down the dark net or not, it’s hard to avoid the conclusion that trying to do so would likely be impossible.
In fact, as Watters, says, trying to police the problem just drives it elsewhere or even makes it bigger.
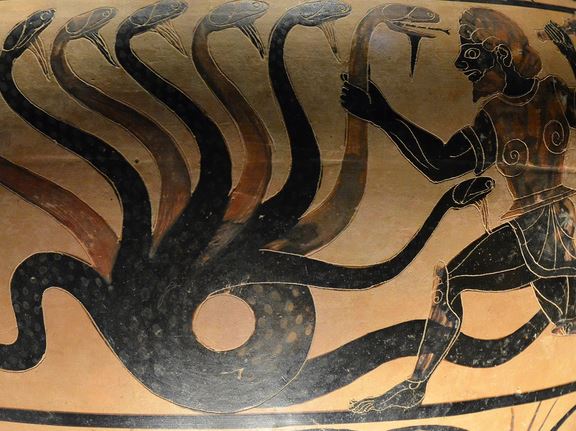
Watters likens it to the story of the demi-God Hercules trying to kill the hydra; every time Hercules cut off one of the hydra’s heads, more would grow.
He cites the example of Operation Firewall in 2004, in which the FBI and secret service in the US cracked down on dark net actors. Before this, the threat actors worked primarily in English language forums.
John Watters, CEO of iSIGHT Partners
"There were very few convictions but there were a lot of arrests and it made a lot of noise," he says of Firewall.
The result was that the English forums went to local languages and the cyber criminals "got really fussy about who they’d deal with."
"That increased the degree of difficulty," says Watters. "I knew that would be a differentiator between those who could really execute in cyber security and those for whom it was just a nice to have."
He says the same of Russian Business Network, a big rogue hoster that was taken down five years ago. The result, he says, is that the organised network of hosters all went their own way, with the same capabilities spreading throughout the dark net.
So if high-profile crackdowns just lead to a few arrests but fairly to wipe out the threat from dark net cyber criminals, what is the remedy?
iSIGHT Partners, which was recently acquired by FireEye, has experts that trail the dark web and analyse code in order to find new threats and identify the people responsible.
The company used its intelligence to attribute the recent attacks on the Ukraine energy grid to the Sandworm team and linked FIN6 hacking group to a breach of 20 million cards.
The team also uncovered that Russian ‘Sandworm‘ hackers were spying on the EU, as well as revealing a cyber espionage campaign originating in China using Forbes.com in an attempt to hack US military and government networks.
Watters says that monitoring the dark net is all about "longevity".
"We’ve been in this business a long time and our employees have been with us for a long time," he says.
Over this long period, they have had to cultivate identities that will not be detected by the hackers.
"You can tell very quickly who’s law enforcement and who’s new," says Watters. "These guys will get made quickly and booted off the site."
Having an identity is about several things; part of it means simply interacting as a human, since bots are quickly and easily detected in the dark net forums.
However, equally important is knowing "the local market, tools, tradecraft and pricing". Since Operation Firewall, knowledge of local languages is crucial due to the way the forums now operate.
Watters emphasises the company’s credentials as a global business, quickly opening up in a large number of questions after its launch.
It’s a growing threat, he says.
"We’ve gone from tracking hundreds of criminal actors nine years ago to thousands a few years ago to 16000 plus now."
The intelligence will now be integrated with FireEye‘s technology, providing context to attacks on its customers.
Whatever citizens want, attempts to police the dark net through conventional law enforcement techniques are likely to be frustrated. If Watters is right, the only way to stop dark net hackers is to think and act like one.
Are we losing the battle in cyberspace? Read our exclusive interview with Nuix here.







